热门标签
热门文章
- 1算法空间复杂度详解
- 2DELL 服务器 RAID 配置教程 在启动电脑的时候按 CTRL+R 进入 RAID 设置见面如下图 名称解释_dell服务器vd和pd和ctrl mgmt
- 3初级、中级、高级测试/开发程序员的区别在哪里?传说中的码农......_初级软件测试和中级软件测试的区别
- 4通信教程 | USB、HDMI、DP接口及速度
- 5利用虚拟机做Web服务器,使用物理机通过在浏览器输入IP和域名来访问自己做的网站_您可以通过浏览器访问虚拟机的ip地址来测试默认主页是否可访问成功。
- 6OSI七层参考模型_osi七层模型单位
- 7VSCode下载与插件安装_vscode扩展包下载
- 8银河麒麟高级服务器V10 SP1下supervisor的安装及配置_supervisor 4 银河麒麟
- 9计算机网络_所有用户在同一时段都占用不同的平台一旦分配出去用户就会占用该平台直的通信
- 10卷积层,池化层,全连接层_卷积层,池化层,全连接层
当前位置: article > 正文
centos 6远程ssh登录和本地login(tty)登录 密码错误N次 锁定登录_开启tty登录密码错误锁定用户,修改
作者:你好赵伟 | 2024-02-26 19:46:01
赞
踩
开启tty登录密码错误锁定用户,修改
pam_tally2.so的PAM模块,来限定用户的登录失败次数,如果次数达到设置的阈值,则锁定用户
配置过程
系统是CentOS release 6.9 (Final)
1.如果只限制本地login方式登录(tty),只需配置 /etc/pam.d/login
$ cat /etc/pam.d/login #%PAM-1.0 auth required pam_tally2.so deny=3 unlock_time=300 even_deny_root root_unlock_time=300 auth [user_unknown=ignore success=ok ignore=ignore default=bad] pam_securetty.so auth include system-auth account required pam_nologin.so account include system-auth password include system-auth # pam_selinux.so close should be the first session rule session required pam_selinux.so close session required pam_loginuid.so session optional pam_console.so # pam_selinux.so open should only be followed by sessions to be executed in the user context session required pam_selinux.so open session required pam_namespace.so session optional pam_keyinit.so force revoke session include system-auth -session optional pam_ck_connector.so
- 1
- 2
- 3
- 4
- 5
- 6
- 7
- 8
- 9
- 10
- 11
- 12
- 13
- 14
- 15
- 16
- 17
- 18
even_deny_root : 也限制root用户;
deny : 设置普通用户和root用户连续错误登陆的最大次数,超过最大次数,则锁定该用户
unlock_time:设定普通用户锁定后,多少时间后解锁,单位是秒;
root_unlock_time:设定root用户锁定后,多少时间后解锁,单位是秒;
此处使用的是 pam_tally2 模块,如果不支持 pam_tally2 可以使用 pam_tally 模块。另外,不同的pam版本,设置可能有所不同,具体使用方法,可以参照相关模块的使用规则。
将auth required pam_tally2.so deny=3 unlock_time=300 even_deny_root root_unlock_time=300
放置在#%PAM-1.0的下面,即第二行,添加内容,一定要写在前面,如果写在后面,虽然用户被锁定,但是只要用户输入正确的密码,还是可以登录的!

2.远程ssh登录限制
首先需要打开sshd_config里的UsePAM yes 配置
$ cat /etc/ssh/sshd_config |grep UsePAM
UsePAM yes
- 1
- 2
编辑 /etc/pam.d/sshd (自己创建此文件)
$ cat /etc/pam.d/sshd #%PAM-1.0 auth required pam_tally2.so deny=3 unlock_time=300 even_deny_root root_unlock_time=300 #auth [user_unknown=ignore success=ok ignore=ignore default=bad] pam_securetty.so auth include system-auth account required pam_nologin.so account include system-auth password include system-auth # pam_selinux.so close should be the first session rule session required pam_selinux.so close session required pam_loginuid.so session optional pam_console.so # pam_selinux.so open should only be followed by sessions to be executed in the user context session required pam_selinux.so open session required pam_namespace.so session optional pam_keyinit.so force revoke session include system-auth -session optional pam_ck_connector.so
- 1
- 2
- 3
- 4
- 5
- 6
- 7
- 8
- 9
- 10
- 11
- 12
- 13
- 14
- 15
- 16
- 17
- 18
- 19
重启sshd
service sshd restart
- 1
用其他机器进行验证
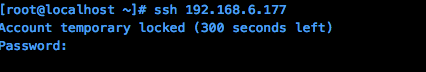
查看用户登录失败的次数
$ pam_tally2 -r -u root
Login Failures Latest failure From
root 5 10/16/19 18:10:49 192.168.6.177
- 1
- 2
- 3
解锁指定用户
$ pam_tally2 --user root
Login Failures Latest failure From
root 0
- 1
- 2
- 3
声明:本文内容由网友自发贡献,不代表【wpsshop博客】立场,版权归原作者所有,本站不承担相应法律责任。如您发现有侵权的内容,请联系我们。转载请注明出处:https://www.wpsshop.cn/w/你好赵伟/article/detail/146438
推荐阅读
相关标签



