热门标签
热门文章
- 1使用PyTorch实现图像处理和识别
- 2spring actuator 自定义shutdown_「Java」 - SpringBoot & Actuator
- 3【无人机三维路径规划】基于遗传算法实现无人机航迹规划附matlab代码_基于遗传算法的无人机三维航迹规划研究[
- 4自从Notion有了AI……
- 5部署使用AutoGPT全过程_auto-gpt部署教程
- 6VAE——生成数字(Pytorch+mnist)
- 7Debezium日常分享系列之:Debezium2.5稳定版本之处理常见问题
- 8推特社交机器人分类
- 9vue项目转桌面应用程序_如何将一个springboot+vue项目打包成桌面应用
- 10Java&python实现网页内容自动识别与提取技术实现_htmlsucker
当前位置: article > 正文
基于门限算法的SM2协同签名算法分析-openssl源码验证
作者:你好赵伟 | 2024-04-08 21:27:52
赞
踩
sm2协同签名算法
基于门限算法的SM2协同签名算法分析-openssl源码验证
介绍
门限密码体制 是安全多方计算中对抗合谋攻击的一个重要工具,在门限密码体制中, n个参与者联合生成公钥,解密密钥由 n 个参与者联合持有公可以直接加密消息但解密需要 n个参与者中一定数量人员参与才能正确解密.
接下来介绍一种基于门限密码思想的SM2协同签名方法,是一种(2,2)门限密码方案,即需要两方参与的协同签名流程。
参考文献《基于SM2的双方共同签名协议及其应用》
该方法主要分两个流程,协同公钥生成和协同签名。
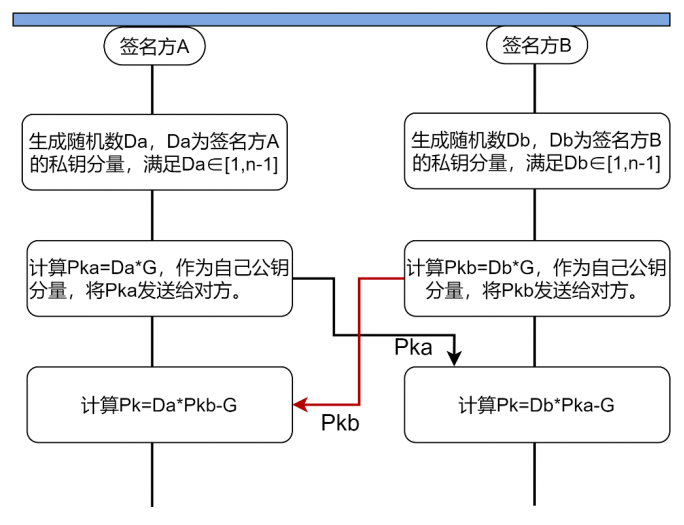
1 协同公钥生成流程

双方主要交互流程如下图:
2 协同签名流程
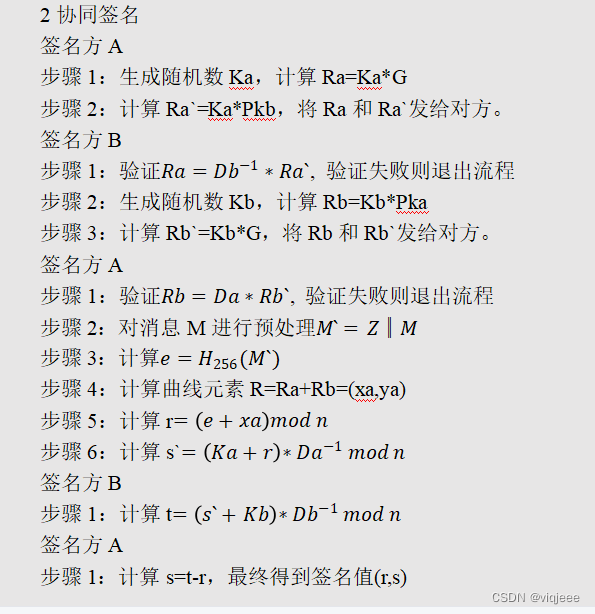
双方主要交互流程如下图:

3 正确性分析

4 使用openssl接口进行代码测试
测试数据如下:
======================================= 生成协同公钥: ======================================= 发送方A: Da 密钥分量: 0xd4, 0xf3, 0x1d, 0x15, 0x17, 0x07, 0x51, 0x33, 0x72, 0xd7, 0x5e, 0x56, 0x26, 0x61, 0xf7, 0x9d, 0x95, 0x61, 0xe8, 0x8a, 0xa3, 0xb9, 0xa9, 0xf7, 0x67, 0xaf, 0x23, 0x95, 0x5e, 0xbb, 0xe2, 0x82, 公钥分量Pka: -X 0x06, 0x00, 0x38, 0x73, 0x0e, 0xfe, 0x5b, 0x48, 0x28, 0x6b, 0x97, 0xd7, 0xff, 0x1e, 0xbb, 0xe7, 0x55, 0x0c, 0xe4, 0x5d, 0x94, 0x34, 0x4f, 0x15, 0x50, 0xa6, 0x63, 0x10, 0x37, 0xd7, 0x3c, 0xe8, -Y 0xbc, 0x42, 0x36, 0xcf, 0xf3, 0x41, 0xb1, 0x23, 0xf7, 0x49, 0x38, 0x1a, 0x4c, 0x64, 0xbc, 0x81, 0x84, 0x3b, 0xf0, 0xc4, 0x5c, 0x38, 0xde, 0x2d, 0x82, 0xfe, 0x46, 0xa6, 0xbf, 0x1c, 0xe8, 0xfc, 发送方B: Db 密钥分量: 0xca, 0xe1, 0x6c, 0x68, 0x4b, 0x21, 0xad, 0x08, 0x4c, 0xd3, 0x01, 0x5c, 0xdb, 0xfa, 0xa8, 0x62, 0x6e, 0x89, 0xd3, 0x1f, 0xa8, 0x01, 0x04, 0xe4, 0x13, 0x6c, 0x75, 0xa9, 0xca, 0x4d, 0x44, 0xa9, 公钥分量Pkb: -X 0xc7, 0x11, 0x15, 0x28, 0xc8, 0x31, 0x1f, 0xe9, 0x96, 0xb6, 0x6a, 0x2f, 0x07, 0xbe, 0x69, 0x30, 0x4a, 0x9f, 0x22, 0x4c, 0x23, 0x40, 0xe9, 0x2a, 0x0e, 0x6c, 0x15, 0x21, 0x62, 0x2e, 0xcb, 0xa6, -Y 0x7d, 0xfd, 0xa6, 0x61, 0x45, 0xe4, 0x1f, 0x22, 0xa5, 0x28, 0xfb, 0x8e, 0x04, 0x2b, 0x0b, 0x13, 0xc3, 0x30, 0xda, 0x74, 0x05, 0x8e, 0x9c, 0x2e, 0xe1, 0xbf, 0x07, 0xc8, 0x77, 0x2d, 0x08, 0xf9, 共同公钥Pk: 0x04, 0x1b, 0xde, 0x21, 0x21, 0x98, 0xb4, 0xb9, 0x6d, 0x24, 0x72, 0x5e, 0x57, 0x51, 0x3c, 0x95, 0xf9, 0xb7, 0x3c, 0x91, 0x2a, 0x7a, 0x6a, 0x1f, 0x82, 0xf6, 0x80, 0x8a, 0x2d, 0x79, 0x51, 0xa1, 0xc6, 0xca, 0xd8, 0x89, 0xf2, 0x91, 0x3b, 0x0f, 0xd7, 0xe1, 0x1c, 0x55, 0xe7, 0xa9, 0x98, 0xcc, 0x65, 0x5e, 0x1c, 0x46, 0x17, 0xd7, 0x33, 0x8d, 0x90, 0x62, 0x80, 0x80, 0xff, 0xb9, 0xaa, 0x03, 0xe5, ======================================= 协同签名: ======================================= 发送方A: Ka: 0x4c, 0xa0, 0xf7, 0xae, 0xe8, 0x18, 0x79, 0x59, 0x88, 0x4d, 0x2b, 0x1a, 0x78, 0xca, 0xa9, 0x4c, 0xb1, 0x70, 0x5f, 0x0b, 0x11, 0x31, 0x0f, 0xa3, 0xb4, 0x1c, 0xfe, 0x2b, 0x15, 0xc7, 0x05, 0xa8, Ra: -X 0x87, 0xca, 0xb9, 0x85, 0xe4, 0xda, 0xcc, 0xd6, 0xe1, 0x8d, 0xba, 0xed, 0x7e, 0x6d, 0x8e, 0xd5, 0x80, 0xd4, 0x29, 0xac, 0x1e, 0x83, 0xb3, 0x13, 0x94, 0xb8, 0x82, 0x0f, 0x0b, 0x52, 0xf9, 0x47, -Y 0xf8, 0xb0, 0xd8, 0x75, 0xd5, 0xf7, 0x79, 0x9e, 0xce, 0xa1, 0x44, 0x7f, 0x79, 0xdb, 0x1a, 0x31, 0x37, 0x1d, 0x0f, 0xaf, 0x25, 0xad, 0xb6, 0x42, 0x25, 0x7a, 0xb5, 0xcd, 0xda, 0x81, 0x68, 0x42, Ra`: -X 0xb8, 0xcb, 0xe1, 0x48, 0x05, 0x7d, 0xaf, 0x00, 0xb6, 0x58, 0x36, 0xcd, 0x47, 0xd0, 0x09, 0x37, 0xe3, 0x00, 0x40, 0x9e, 0x0a, 0xd1, 0x5a, 0x62, 0x50, 0xac, 0x06, 0x2e, 0x1e, 0x75, 0x50, 0xf5, -Y 0x78, 0xf6, 0x85, 0xca, 0x70, 0x56, 0xaa, 0x5a, 0x67, 0x2c, 0x6a, 0xf2, 0x73, 0xf6, 0xbd, 0xc4, 0xa7, 0x35, 0x17, 0x84, 0x4d, 0xd4, 0x82, 0x37, 0xa9, 0xfb, 0x72, 0x08, 0x30, 0xab, 0x3e, 0x3d, 发送方B: point Ra verify sucessful Kb: 0x2c, 0xe9, 0xf7, 0x07, 0x21, 0x87, 0xd6, 0x56, 0x50, 0xf9, 0x4a, 0x5c, 0x43, 0x26, 0x2e, 0x33, 0x83, 0xfc, 0x0d, 0xf5, 0xa4, 0x0c, 0x3d, 0x49, 0xe1, 0xff, 0x18, 0xd4, 0x5c, 0xe6, 0x1d, 0xee, Rb: -X 0x98, 0xc7, 0xdf, 0xaa, 0x41, 0xaf, 0x2a, 0xb9, 0x34, 0x30, 0xc9, 0x7d, 0xda, 0xad, 0x8c, 0xd2, 0x3a, 0xa1, 0x71, 0x3e, 0xda, 0x33, 0x1f, 0xa5, 0x16, 0xd7, 0x6c, 0xf7, 0x56, 0xe4, 0xee, 0xa6, -Y 0x62, 0xce, 0x50, 0xc7, 0x1e, 0x5e, 0xeb, 0x90, 0x29, 0x93, 0x0a, 0xfb, 0x69, 0x07, 0x29, 0x19, 0xa8, 0xd7, 0x6d, 0xdc, 0x5c, 0x10, 0x23, 0x69, 0xa4, 0x7f, 0xbe, 0x78, 0xf2, 0x35, 0xfe, 0x46, Rb`: -X 0x5f, 0xeb, 0x24, 0x52, 0xdf, 0x08, 0xd2, 0xda, 0xac, 0x48, 0x4d, 0xfe, 0x3f, 0x44, 0x03, 0x55, 0xaf, 0x67, 0xde, 0x60, 0x98, 0x80, 0xbb, 0xa8, 0xfd, 0x9c, 0xaa, 0x6b, 0x86, 0x58, 0xa0, 0x54, -Y 0x56, 0x6a, 0x6b, 0xdc, 0x76, 0xcb, 0x19, 0x0c, 0x31, 0xce, 0xad, 0xb8, 0x5b, 0x28, 0xe0, 0x38, 0x3c, 0x32, 0x59, 0x0c, 0x88, 0x54, 0xcf, 0x9b, 0xfd, 0xe6, 0x2e, 0x6a, 0xfd, 0xf1, 0x01, 0x56, 发送方A: 消息M: 0x01, 0x02, 0x03, 0x04, 0x05, 0x06, 0x07, 0x08, 0x09, Z值: 0x31, 0x32, 0x33, 0x34, 0x35, 0x36, 0x37, 0x38, 0x31, 0x32, 0x33, 0x34, 0x35, 0x36, 0x37, 0x38, e: 0xfe, 0x7c, 0x9f, 0x48, 0x39, 0x4a, 0xa7, 0xfa, 0x0a, 0x0f, 0x99, 0x9e, 0x1e, 0xe1, 0x41, 0xb5, 0x5a, 0xbe, 0x20, 0xc5, 0x59, 0x47, 0x13, 0x6b, 0xaa, 0x9e, 0x52, 0x1b, 0x31, 0x77, 0x76, 0x7b, point Rb verify sucessful 点R (xa,ya): -X 0xa0, 0x73, 0x36, 0x10, 0xd1, 0x74, 0x5d, 0xcd, 0x77, 0xb4, 0x5b, 0x5e, 0xa2, 0x0e, 0xba, 0xdc, 0xc5, 0xd9, 0x9c, 0x34, 0xe2, 0x9e, 0xb9, 0xe9, 0x59, 0xb0, 0xa4, 0x90, 0xd6, 0x23, 0x13, 0x89, -Y 0xde, 0x3c, 0x28, 0xa9, 0xfc, 0xbd, 0x1f, 0x32, 0xc6, 0x1a, 0xd7, 0x63, 0x16, 0xa7, 0x0f, 0x20, 0x41, 0x67, 0x29, 0x3f, 0x53, 0xb2, 0x2b, 0x07, 0x5d, 0x2d, 0x5e, 0x9d, 0xce, 0x62, 0xdf, 0x0e, r: 0x9e, 0xef, 0xd5, 0x5a, 0x0a, 0xbf, 0x05, 0xc7, 0x81, 0xc3, 0xf4, 0xfc, 0xc0, 0xef, 0xfc, 0x92, 0xae, 0x93, 0xdd, 0x8f, 0x1a, 0x1f, 0xc8, 0x29, 0xb0, 0x93, 0x02, 0xa2, 0xcd, 0xc5, 0x48, 0xe1, s`: 0x91, 0xa1, 0xd9, 0x3f, 0x0f, 0x9b, 0xd0, 0xf6, 0x87, 0x4d, 0xdd, 0x98, 0x1e, 0xf1, 0x98, 0xa3, 0xc8, 0xbc, 0xce, 0x21, 0xd3, 0x99, 0xdd, 0x02, 0x33, 0x9c, 0xc5, 0xdf, 0xaa, 0xfd, 0x3d, 0xcd, 发送方B: t: 0xc7, 0xd6, 0x11, 0xd0, 0x79, 0xed, 0xb7, 0x91, 0x0c, 0x06, 0xb5, 0xe8, 0xf7, 0xe6, 0x44, 0xc8, 0xe2, 0x48, 0x97, 0xa4, 0xa6, 0x44, 0xbe, 0x04, 0x2a, 0x90, 0x5e, 0x36, 0x3c, 0x7f, 0x0a, 0x4b, 发送方A: r: 0x9e, 0xef, 0xd5, 0x5a, 0x0a, 0xbf, 0x05, 0xc7, 0x81, 0xc3, 0xf4, 0xfc, 0xc0, 0xef, 0xfc, 0x92, 0xae, 0x93, 0xdd, 0x8f, 0x1a, 0x1f, 0xc8, 0x29, 0xb0, 0x93, 0x02, 0xa2, 0xcd, 0xc5, 0x48, 0xe1, s: 0x28, 0xe6, 0x3c, 0x76, 0x6f, 0x2e, 0xb1, 0xc9, 0x8a, 0x42, 0xc0, 0xec, 0x36, 0xf6, 0x48, 0x36, 0x33, 0xb4, 0xba, 0x15, 0x8c, 0x24, 0xf5, 0xda, 0x79, 0xfd, 0x5b, 0x93, 0x6e, 0xb9, 0xc1, 0x6a, r: 0x9e, 0xef, 0xd5, 0x5a, 0x0a, 0xbf, 0x05, 0xc7, 0x81, 0xc3, 0xf4, 0xfc, 0xc0, 0xef, 0xfc, 0x92, 0xae, 0x93, 0xdd, 0x8f, 0x1a, 0x1f, 0xc8, 0x29, 0xb0, 0x93, 0x02, 0xa2, 0xcd, 0xc5, 0x48, 0xe1, s: 0x28, 0xe6, 0x3c, 0x76, 0x6f, 0x2e, 0xb1, 0xc9, 0x8a, 0x42, 0xc0, 0xec, 0x36, 0xf6, 0x48, 0x36, 0x33, 0xb4, 0xba, 0x15, 0x8c, 0x24, 0xf5, 0xda, 0x79, 0xfd, 0x5b, 0x93, 0x6e, 0xb9, 0xc1, 0x6a,
- 1
- 2
- 3
- 4
- 5
- 6
- 7
- 8
- 9
- 10
- 11
- 12
- 13
- 14
- 15
- 16
- 17
- 18
- 19
- 20
- 21
- 22
- 23
- 24
- 25
- 26
- 27
- 28
- 29
- 30
- 31
- 32
- 33
- 34
- 35
- 36
- 37
- 38
- 39
- 40
- 41
- 42
- 43
- 44
- 45
- 46
- 47
- 48
- 49
- 50
- 51
- 52
- 53
- 54
- 55
- 56
- 57
- 58
- 59
- 60
- 61
- 62
- 63
- 64
- 65
- 66
- 67
- 68
- 69
- 70
- 71
- 72
- 73
- 74
- 75
- 76
- 77
- 78
- 79
- 80
- 81
- 82
- 83
- 84
- 85
- 86
- 87
- 88
- 89
- 90
- 91
- 92
- 93
- 94
- 95
- 96
- 97
- 98
- 99
- 100
- 101
- 102
- 103
- 104
- 105
- 106
- 107
- 108
- 109
- 110
经过和标准SM2签名对比,可以验签通过:
验签 通过
算法: SM2公钥验签
数据 长度9(0x09)字节
01 02 03 04 05 06 07 08 09
签名结果 长度64(0x40)字节
9E EF D5 5A 0A BF 05 C7 81 C3 F4 FC C0 EF FC 92 AE 93 DD 8F 1A 1F C8 29 B0 93 02 A2 CD C5 48 E1 28 E6 3C 76 6F 2E B1 C9 8A 42 C0 EC 36 F6 48 36 33 B4 BA 15 8C 24 F5 DA 79 FD 5B 93 6E B9 C1 6A
ID:16(0x10)字节
31 32 33 34 35 36 37 38 31 32 33 34 35 36 37 38
HASH:32(0x20)字节
FE 7C 9F 48 39 4A A7 FA 0A 0F 99 9E 1E E1 41 B5 5A BE 20 C5 59 47 13 6B AA 9E 52 1B 31 77 76 7B
- 1
- 2
- 3
- 4
- 5
- 6
- 7
- 8
- 9
- 10
5 测试源码
https://download.csdn.net/download/qq_39952971/87966483
声明:本文内容由网友自发贡献,不代表【wpsshop博客】立场,版权归原作者所有,本站不承担相应法律责任。如您发现有侵权的内容,请联系我们。转载请注明出处:https://www.wpsshop.cn/w/你好赵伟/article/detail/388318
推荐阅读
相关标签



