热门标签
热门文章
- 1Proxmox VE 6.0管理指南——4.超融合基础设施_proxmox 公共网络
- 2UOS和Deepin的前世今生_deepin和uos
- 3Android——直播推流SDK_android 免费的推流sdk
- 4Python入门初学一、Python简介及发展,带你深入认识Python_大学计算机科学技术专业对python新技术的认识了解
- 5glib源码安装使用方法
- 6【力扣hot100】刷题笔记Day14
- 7100天精通Golang(基础入门篇)——第1天:学习Go语言基本概念_golang从入门到精通得需要多长时间
- 8Qt Remote Objects 简介_qremoteobject
- 9推荐系统——电影评分预测算法(基于用户的协同过滤、基于物品的协同过滤)_下载movielens 100k数据集 ,实现user-based cf,计算预测准确度
- 10使用PyTorch构建卷积神经网络(CNN)源码(详细步骤讲解+注释版) 01 手写数字识别_pytorch 一维cnn手写数据集分类代码
当前位置: article > 正文
springboot解决XSS存储型漏洞_springboot xss漏洞修复
作者:小丑西瓜9 | 2024-02-27 05:19:54
赞
踩
springboot xss漏洞修复
springboot解决XSS存储型漏洞
XSS攻击
XSS 攻击:跨站脚本攻击(Cross Site Scripting),为不和 前端层叠样式表(Cascading Style Sheets)CSS 混淆,故将跨站脚本攻击缩写为 XSS。
XSS(跨站脚本攻击):是指恶意攻击者往 Web 页面里插入恶意 Script 代码,当用户浏览该页时,嵌入其中 Web 里面的 Script 代码会被执行,从而达到恶意攻击用户的目的。类似于 sql 注入。是目前最普遍的 Web 应用安全漏洞,也是 Web 攻击中最常见的攻击方式之一。
XSS( 跨站脚本攻击)攻击通常指的是通过利用网页开发时留下的漏洞,通过巧妙的方法注入恶意指令代码到网页,使用户加载并执行攻击者恶意制造的网页程序。这些恶意网页程序通常是 JavaScript,但实际上也可以包括 Java、 VBScript、ActiveX、 Flash 或者甚至是普通的 HTML。攻击成功后,攻击者可能得到包括但不限于更高的权限(如执行一些操作)、私密网页内容、会话和 cookie 等各种内容。
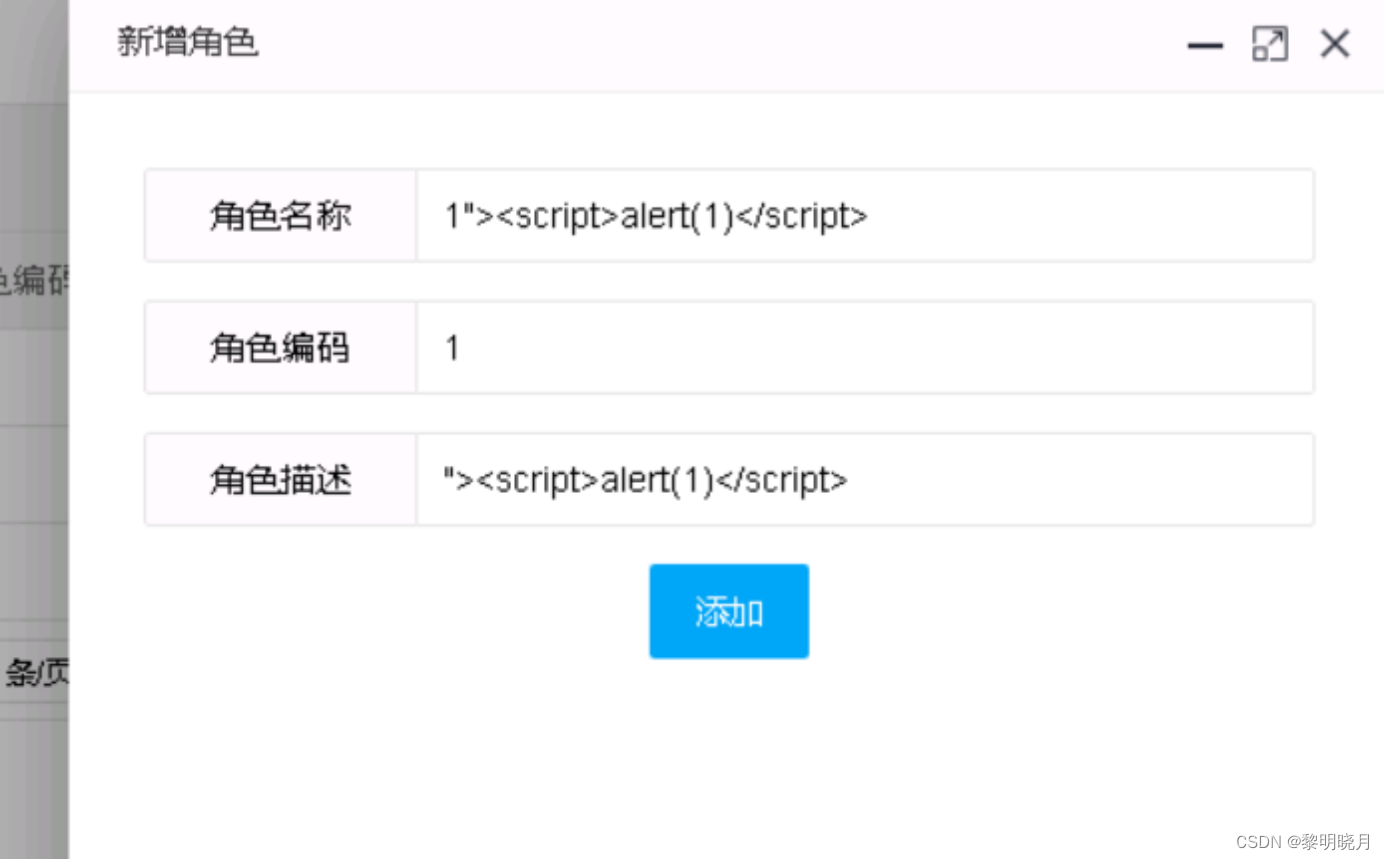
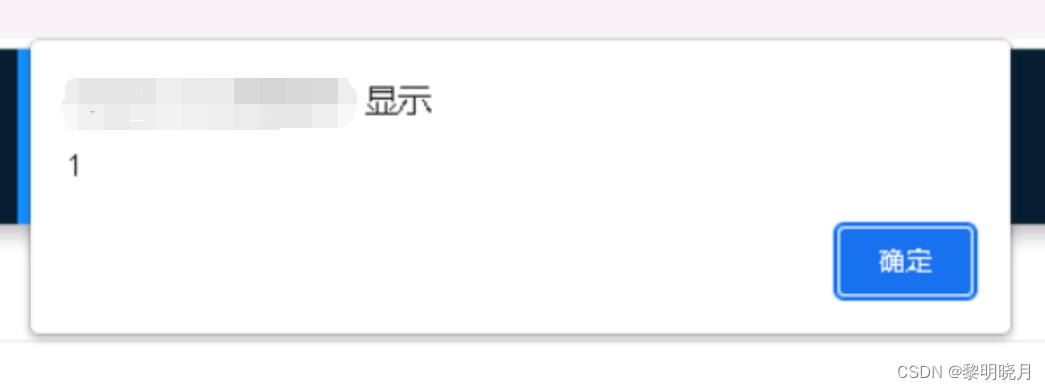
XSS攻击示例:
过滤请求非法内容XSS类:XssRequestWrappers
这个类用来过滤请求非法内容,详细代码如下:
import java.util.HashMap; import java.util.Map; import java.util.Set; import java.util.regex.Pattern; import javax.servlet.http.HttpServletRequest; import javax.servlet.http.HttpServletRequestWrapper; import org.springframework.util.StringUtils; import org.springframework.web.multipart.MultipartHttpServletRequest; import org.springframework.web.multipart.commons.CommonsMultipartResolver; /** * @ClassName XssRequestWrappers * @Description TODO * @Author tongxueqiyue * @Date 2023/12/18 10:43 * @Version 1.0 */ public class XssRequestWrappers extends HttpServletRequestWrapper { private CommonsMultipartResolver multiparResolver = new CommonsMultipartResolver(); public XssRequestWrappers(HttpServletRequest request) { super(request); String type = request.getHeader("Content-Type"); if (!StringUtils.isEmpty(type) && type.contains("multipart/form-data")) { MultipartHttpServletRequest multipartHttpServletRequest = multiparResolver.resolveMultipart(request); Map<String, String[]> stringMap = multipartHttpServletRequest.getParameterMap(); if (!stringMap.isEmpty()) { for (String key : stringMap.keySet()) { String value = multipartHttpServletRequest.getParameter(key); striptXSS(key); striptXSS(value); } } super.setRequest(multipartHttpServletRequest); } } @Override public String[] getParameterValues(String parameter) { String[] values = super.getParameterValues(parameter); if (values == null) { return null; } int count = values.length; String[] encodedValues = new String[count]; for (int i = 0; i < count; i++) { encodedValues[i] = striptXSS(values[i]); } return encodedValues; } @Override public String getParameter(String parameter) { String value = super.getParameter(parameter); return striptXSS(value); } @Override public String getHeader(String name) { String value = super.getHeader(name); return striptXSS(value); } @Override public Map<String, String[]> getParameterMap() { Map<String, String[]> map1 = super.getParameterMap(); Map<String, String[]> escapseMap = new HashMap<String, String[]>(); Set<String> keys = map1.keySet(); for (String key : keys) { String[] valArr = map1.get(key); if (valArr != null && valArr.length > 0) { String[] escapseValArr = new String[valArr.length]; for (int i = 0; i < valArr.length; i++) { String escapseVal = striptXSS(valArr[i]); escapseValArr[i] = escapseVal; } escapseMap.put(key, escapseValArr); } } return escapseMap; } //处理非法内容,如果有新的在此处增加即可 public static String striptXSS(String value) { if (value != null) { // 替换空字符串,以便清除潜在的恶意脚本 value = value.replaceAll("", ""); // 移除<script>标签及其内容 Pattern scriptPattern = Pattern.compile("<script>(.*?)</script>", Pattern.CASE_INSENSITIVE); value = scriptPattern.matcher(value).replaceAll(""); // 移除带有src属性的标签,支持单引号和双引号包围的属性值 scriptPattern = Pattern.compile("src[\r\n]*=[\r\n]*\\\'(.*?)\\\'", Pattern.CASE_INSENSITIVE | Pattern.MULTILINE | Pattern.DOTALL); value = scriptPattern.matcher(value).replaceAll(""); scriptPattern = Pattern.compile("src[\r\n]*=[\r\n]*\\\"(.*?)\\\"", Pattern.CASE_INSENSITIVE | Pattern.MULTILINE | Pattern.DOTALL); value = scriptPattern.matcher(value).replaceAll(""); // 移除</script>标签 scriptPattern = Pattern.compile("</script>", Pattern.CASE_INSENSITIVE); value = scriptPattern.matcher(value).replaceAll(""); // 移除以<script...>开头的标签 scriptPattern = Pattern.compile("<script(.*?)>", Pattern.CASE_INSENSITIVE | Pattern.MULTILINE | Pattern.DOTALL); value = scriptPattern.matcher(value).replaceAll(""); // 移除eval()函数调用 scriptPattern = Pattern.compile("eval\\((.*?)\\)", Pattern.CASE_INSENSITIVE | Pattern.MULTILINE | Pattern.DOTALL); value = scriptPattern.matcher(value).replaceAll(""); // 移除expression()函数调用 scriptPattern = Pattern.compile("expression\\((.*?)\\)", Pattern.CASE_INSENSITIVE | Pattern.MULTILINE | Pattern.DOTALL); value = scriptPattern.matcher(value).replaceAll(""); // 移除以"javascript:"开头的字符串 scriptPattern = Pattern.compile("javascript:", Pattern.CASE_INSENSITIVE); value = scriptPattern.matcher(value).replaceAll(""); // 移除以"vbscript:"开头的字符串 scriptPattern = Pattern.compile("vbscript:", Pattern.CASE_INSENSITIVE); value = scriptPattern.matcher(value).replaceAll(""); // 移除以"onload..."开头的字符串 scriptPattern = Pattern.compile("onload(.*?)=", Pattern.CASE_INSENSITIVE | Pattern.MULTILINE | Pattern.DOTALL); value = scriptPattern.matcher(value).replaceAll(""); // 移除包含任何<和>字符的字符串 scriptPattern = Pattern.compile(".*<.*", Pattern.CASE_INSENSITIVE); value = scriptPattern.matcher(value).replaceAll(""); } // 返回处理后的字符串 return value; } }
- 1
- 2
- 3
- 4
- 5
- 6
- 7
- 8
- 9
- 10
- 11
- 12
- 13
- 14
- 15
- 16
- 17
- 18
- 19
- 20
- 21
- 22
- 23
- 24
- 25
- 26
- 27
- 28
- 29
- 30
- 31
- 32
- 33
- 34
- 35
- 36
- 37
- 38
- 39
- 40
- 41
- 42
- 43
- 44
- 45
- 46
- 47
- 48
- 49
- 50
- 51
- 52
- 53
- 54
- 55
- 56
- 57
- 58
- 59
- 60
- 61
- 62
- 63
- 64
- 65
- 66
- 67
- 68
- 69
- 70
- 71
- 72
- 73
- 74
- 75
- 76
- 77
- 78
- 79
- 80
- 81
- 82
- 83
- 84
- 85
- 86
- 87
- 88
- 89
- 90
- 91
- 92
- 93
- 94
- 95
- 96
- 97
- 98
- 99
- 100
- 101
- 102
- 103
- 104
- 105
- 106
- 107
- 108
- 109
- 110
- 111
- 112
- 113
- 114
- 115
- 116
- 117
- 118
- 119
- 120
- 121
- 122
- 123
- 124
- 125
- 126
- 127
- 128
- 129
- 130
- 131
- 132
- 133
- 134
- 135
- 136
- 137
定义过滤器监听XSSFilter 重写Filter
在这个过滤器中监听XSSFilter,使用上面写的XssRequestWrappers来处理请求中的非法内容
import java.io.IOException; import javax.servlet.Filter; import javax.servlet.FilterChain; import javax.servlet.FilterConfig; import javax.servlet.ServletException; import javax.servlet.ServletRequest; import javax.servlet.ServletResponse; import javax.servlet.http.HttpServletRequest; /** * @ClassName XSSFilter * @Description TODO * @Author tongxueqiyue * @Date 2023/12/18 10:45 * @Version 1.0 */ public class XSSFilter implements Filter { @Override public void init(FilterConfig arg0) throws ServletException { } @Override public void destroy() { } @Override public void doFilter(ServletRequest request, ServletResponse response, FilterChain chain) throws IOException, ServletException { chain.doFilter(new XssRequestWrappers((HttpServletRequest) request), response); } }
- 1
- 2
- 3
- 4
- 5
- 6
- 7
- 8
- 9
- 10
- 11
- 12
- 13
- 14
- 15
- 16
- 17
- 18
- 19
- 20
- 21
- 22
- 23
- 24
- 25
- 26
- 27
- 28
- 29
- 30
- 31
- 32
- 33
注册这个XSSFilter为Bean
import org.springframework.boot.web.servlet.FilterRegistrationBean; import org.springframework.context.annotation.Bean; import org.springframework.context.annotation.Configuration; @Configuration public class WebConfig { @Bean public FilterRegistrationBean<XSSFilter> xssFilterRegistrationBean() { FilterRegistrationBean<XSSFilter> registrationBean = new FilterRegistrationBean<>(); registrationBean.setFilter(new XSSFilter()); registrationBean.addUrlPatterns("/*"); // 这里配置需要过滤的URL registrationBean.setName("xssFilter"); registrationBean.setOrder(1); // 设置过滤器的执行顺序,数字越小越优先 return registrationBean; } }
- 1
- 2
- 3
- 4
- 5
- 6
- 7
- 8
- 9
- 10
- 11
- 12
- 13
- 14
- 15
- 16
- 17
执行这三步应该就可以了,不过启动可能会报错,如果报错添加以下依赖即可:
<dependency>
<groupId>commons-fileupload</groupId>
<artifactId>commons-fileupload</artifactId>
<version>1.4</version>
</dependency>
- 1
- 2
- 3
- 4
- 5
到这里XSS存储型漏洞应该就能解决了
参考:
https://blog.csdn.net/qq_25580555/article/details/128237542
https://blog.csdn.net/qq_26244285/article/details/122586506
声明:本文内容由网友自发贡献,不代表【wpsshop博客】立场,版权归原作者所有,本站不承担相应法律责任。如您发现有侵权的内容,请联系我们。转载请注明出处:https://www.wpsshop.cn/w/小丑西瓜9/article/detail/150320
推荐阅读
相关标签




