前言
以前搞过这游戏。自从某版本的签名验证加强之后基本很难搞了。今天看了下,
lua采用加密方式 EVP_aes_128_cbc()+gzip压缩,用openssl-android的静态库,
(导出函数全没了)不过不影响分析。
正文
关键库libhegame.so。IDA载入。查看j_j_AAssetManager_open 交叉引用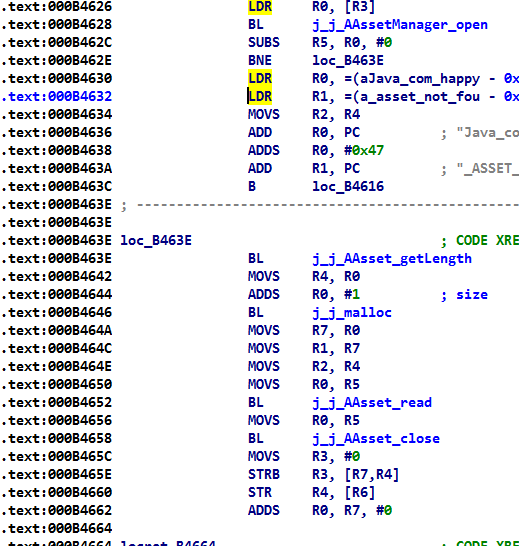
上述代码assets目录下读取文件到内存。并返回内存指针
接着向上层层追踪,最终来到这方法。
f5查看伪代码,分析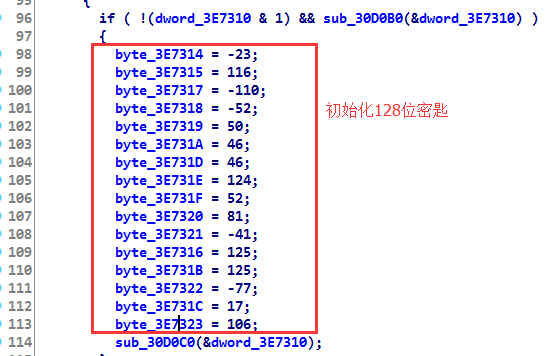
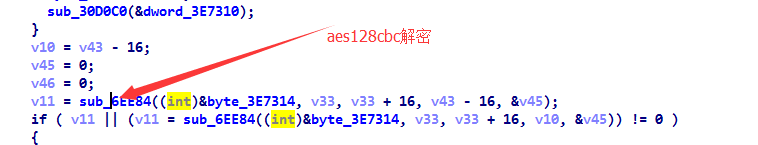
查看方法sub_6EE84: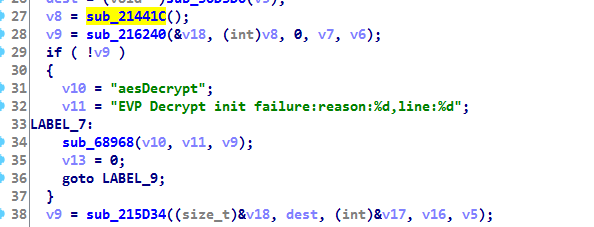
经过整理关键代码:
- void aesDecrypt(unsigned char* data,const char*path)
- {
- unsigned char keyData[16] = { 0xE9, 0x74, 0x7D, 0x92, 0xCC, 0x32, 0x2E, 0x7D, 0x11, 0x2E, 0x7C, 0x34, 0x51, 0xD7, 0xB3, 0x6A };
- EVP_CIPHER_CTX ctx;
- const EVP_CIPHER *cipher;
- cipher = EVP_aes_128_cbc();
- unsigned char iv[EVP_MAX_IV_LENGTH];
- memcpy_s(iv, 16, data, 16);
- EVP_CIPHER_CTX_init(&ctx);
- int ret = EVP_DecryptInit_ex(&ctx, cipher, nullptr, keyData, iv);
- assert(ret == 1);
- unsigned char* result = new unsigned char[datasize - 16];
- memset(result, 0, datasize);
- int len1 = 0;
- ret = EVP_EncryptUpdate(&ctx, result, &len1, (data + 16), datasize - 16);
- assert(ret == 1);
- int len2 = 0;
- if (datasize % 16 != 0)
- {
- int isSuccess = EVP_DecryptFinal_ex(&ctx, result + len1, &len2);
- if (!isSuccess)
- {
- printf("EVP_DecryptFinal_ex() failed\n");
- EVP_CIPHER_CTX_cleanup(&ctx);
- }
- result += len1;
- assert(ret == 1);
- return;
- }
- Byte* undata = new Byte[BUF_SIZE];
- uLong nodata = BUF_SIZE;
- zdecompress(result, datasize - 16, undata, &nodata);
- remove(path);
- FILE* file = fopen(path, "wb");
- fwrite(undata, nodata, 1, file);
- fclose(file);
- delete[] undata;
- delete[] data;
- printf("解密成功:%s\n",path);
- return;
- }
测试结果:
结束语
由于采用aes对称加密算法,加密解密密匙一样的,修改完加密回去应该没问题,需要注意的是是否存在lua文件校检。



