- 1霍兰德职业兴趣测试全解析,助你找到理想工作!_职业性向测试
- 2hive实验的学习实验报告_hive实践报告
- 3python停止打印日志/重复打印日志_python logging 关闭日志文件的方法
- 4[渝粤教育] 四川工程职业技术学院 焊条电弧焊技术与操作 参考 资料_焊条电弧焊在电厂和化工设备安装中应用较多。
- 5docker三剑客docker-compose、docker-machine、swarm
- 6一文搞懂MySQL索引数据结构_数据库索引
- 7java入门实战_java实战
- 8VisibleDeprecationWarning: Creating an ndarray from ragged nested sequences (which is a list-or-tupl
- 9CentOS7离线安装gcc_glibc离线安装
- 10一个好评如潮的UI框架,Quasar Framework
linun——SElinux的简单理解_selinux regular file all file
赞
踩
SElinux简单理解
一.什么是SElinux?
SELinux 全称 Security Enhanced Linux (安全强化 Linux),是 MAC (Mandatory Access Control,强制访问控制系统)的一个实现.目的在于明确的指明某个进程可以访问哪些资源(文件、网络端口等)。举例来说,系统上的 Apache 被发现存在一个漏洞,使得某远程用户可以访问系统上的敏感文件(比如 /etc/passwd 来获得系统已存在用户) ,而修复该安全漏洞的 Apache 更新补丁尚未释出。此时 SELinux 可以起到弥补该漏洞的缓和方案。因为 /etc/passwd 不具有 Apache 的 访问标签,所以 Apache 对于 /etc/passwd 的访问会被 SELinux 阻止。 相比其他强制性访问控制系统,SELinux 有如下优势:
控制策略是可查询而非程序不可见的。
可以热更改策略而无需重启或者停止服务。
可以从进程初始化、继承和程序执行三个方面通过策略进行控制。
控制范围覆盖文件系统、目录、文件、文件启动描述符、端口、消息接口和网络接口。
本博文将会对安全上下文、网络接口等进行一个简单的说明。
二、安全上下文(Security Context)
安全上下文是一个简单的、一致的访问控制属性,在SELinux中,类型标识符是安全上下文的主要组成部分,,一个进程的类型通常被称为一个域,"域"和"域类型"意思都一样,即都是安全上下文中的“TYPE”。
SELinux对系统中的许多命令做了修改,通过添加一个-Z选项显示客体和主体的安全上下文。
安全上下文的查看
id -Z 显示shell的安全上下文
ps -Z 检查进程的安全上下文
ls -Z 检查文件、目录的安全上下文
[root@localhost ~]# id -Z
unconfined_u:unconfined_r:unconfined_t:s0-s0:c0.c1023
[root@localhost ~]# ps -Z
LABEL PID TTY TIME CMD
unconfined_u:unconfined_r:unconfined_t:s0-s0:c0.c1023 2117 pts/0 00:00:00 bash
unconfined_u:unconfined_r:unconfined_t:s0-s0:c0.c1023 2149 pts/0 00:00:00 dbus-l
unconfined_u:unconfined_r:unconfined_t:s0-s0:c0.c1023 2184 pts/0 00:00:00 ps
[root@localhost ~]# ls /var/ftp/
pub
[root@localhost ~]# ls -Z /var/ftp/ <span style="color:#3366FF;">##检查目录/var/ftp/的安全上下文</span>
drwxr-xr-x. root root system_u:object_r:public_content_t:s0 pub
[root@localhost ~]#cp:会重新生成安全上下文
mv:安全上下文则不变
[root@localhost mnt]# ls -Z tutu butterfly
-rw-r--r--. root root unconfined_u:object_r:<span style="color:#CC0000;">mnt_t</span>:s0 butterfly
-rw-r--r--. root root unconfined_u:object_r:<span style="color:#CC0000;">mnt_t</span>:s0 tutu
[root@localhost mnt]# ls -Z /var/ftp
drwxr-xr-x. root root system_u:object_r:<span style="color:#CC0000;">public_content_t</span>:s0 pub
[root@localhost mnt]# cp tutu /var/ftp
[root@localhost mnt]# mv butterfly /var/ftp
[root@localhost mnt]# ls -Z /var/ftp
-rw-r--r--. root root unconfined_u:object_r:<span style="color:#CC0000;">mnt_t</span>:s0 butterfly
drwxr-xr-x. root root system_u:object_r:<span style="color:#CC0000;">public_content_t</span>:s0 pub
-rw-r--r--. root root unconfined_u:object_r:<span style="color:#CC0000;">public_content_t</span>:s0 tutu
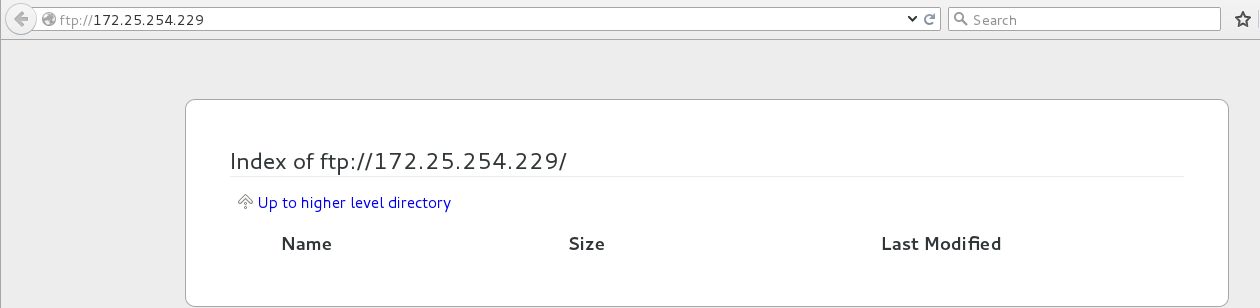
[root@localhost mnt]#安全上下文实验,lftp查看,以及更改安全上下文类型:
目录/var/ftp下的文件安全上下文与/var/ftp的安全上下文不符合的,用lftp查看时,显示不出来
目录/var/ftp下的文件安全上下文与/var/ftp的安全上下文符合的,用lftp查看时,可以显示出来
[root@localhost ftp]# pwd <span style="color:#3366FF;">##显示当前所在位置</span>
/var/ftp
[root@localhost ftp]# touch tutu1
[root@localhost ftp]# ls -Z
drwxr-xr-x. root root system_u:object_r:public_content_t:s0 pub
-rw-r--r--. root root unconfined_u:object_r:public_content_t:s0 tutu1
[root@localhost ftp]# touch /mnt/tutu2
[root@localhost ftp]# mv /mnt/tutu2 /var/ftp <span style="color:#3366FF;">##只能移动,不能复制,复制过去文件的安全上下文会改变成目标目录的安全上下文</span>
[root@localhost ftp]# ls -Z
drwxr-xr-x. root root system_u:object_r:<span style="color:#CC0000;">public_content_t</span>:s0 pub
-rw-r--r--. root root unconfined_u:object_r:public_content_t:s0 tutu1
-rw-r--r--. root root unconfined_u:object_r:<span style="color:#CC0000;">mnt_t</span>:s0 tutu2
[root@localhost ftp]# lftp 172.25.254.229
lftp 172.25.254.229:~> ls <span style="color:#3366FF;">##显示目录/var/ftp下的文件、目录等。文件tutu2的安全上下文不符合,所以显示不出</span>
drwxr-xr-x 2 0 0 6 Mar 07 2014 pub
-rw-r--r-- 1 0 0 0 May 14 01:24 tutu1
lftp 172.25.254.229:/> quit
[root@localhost ftp]# semanage fcontext -l | grep /var/ftp <span style="color:#3366FF;">##查看目录/var/ftp的所有内容的安全上下文</span>
/var/ftp(/.*)? all files system_u:object_r:public_content_t:s0
/var/ftp/bin(/.*)? all files system_u:object_r:bin_t:s0
/var/ftp/etc(/.*)? all files system_u:object_r:etc_t:s0
/var/ftp/lib(/.*)? all files system_u:object_r:lib_t:s0
/var/ftp/lib/ld[^/]*\.so(\.[^/]*)* regular file system_u:object_r:ld_so_t:s0
[root@localhost ftp]# chcon -t public_content_t tutu2 <span style="color:#3366FF;">##更改文件tutu2的安全上下文类型为public_content_t</span>
[root@localhost ftp]# ls -Z
drwxr-xr-x. root root system_u:object_r:public_content_t:s0 pub
-rw-r--r--. root root unconfined_u:object_r:public_content_t:s0 tutu1
-rw-r--r--. root root unconfined_u:object_r:public_content_t:s0 tutu2
[root@localhost ftp]# lftp 172.25.254.229
lftp 172.25.254.229:~> ls
drwxr-xr-x 2 0 0 6 Mar 07 2014 pub
-rw-r--r-- 1 0 0 0 May 14 01:24 tutu1
-rw-r--r-- 1 0 0 0 May 14 01:25 tutu2
lftp 172.25.254.229:/> quit
[root@localhost ftp]#
下面用实验证明:
[root@localhost ~]# mkdir /tutu/
[root@localhost ~]# touch /tutu/butterfly
[root@localhost ~]# vim /etc/vsftpd/vsftpd.conf <span style="color:#3366FF;"> ##编辑该配置文件,添加anon_root=/tutu</span>
[root@localhost ~]# systemctl restart vsftpd <span style="color:#3366FF;"> ##每次编辑该配置文件后,都需要重启vsftpd服务</span>
[root@localhost ~]# lftp 172.25.254.229
lftp 172.25.254.229:~> ls
lftp 172.25.254.229:/> ls
lftp 172.25.254.229:/> quit
[root@localhost ~]# setenforce 0 <span style="color:#3366FF;"> ##修改selinux的值为警告,不需要重启,直接生效</span>
[root@localhost ~]# lftp 172.25.254.229
lftp 172.25.254.229:~> ls
-rw-r--r-- 1 0 0 0 May 14 02:02 butterfly
lftp 172.25.254.229:/> quit
[root@localhost ~]# ls -Z /tutu/ -d
drwxr-xr-x. root root unconfined_u:object_r:<span style="color:#CC0000;">default_t</span>:s0 /tutu/
[root@localhost ~]# chcon -t public_content_t /tutu -R
<span style="color:#3366FF;">##更改文件tutu2的安全上下文类型为public_content_t -R(recursive)——operate on files and directories recursively</span>
[root@localhost ~]# ls -Z /tutu/ <span style="color:#3366FF;">##显示目录下文件的安全上下文</span>
-rw-r--r--. root root unconfined_u:object_r:<span style="color:#CC0000;">public_content_t</span>:s0 butterfly
[root@localhost ~]# ls -Z /tutu/ -d <span style="color:#3366FF;">##显示当前目录的安全上下文</span>
drwxr-xr-x. root root unconfined_u:object_r:<span style="color:#CC0000;">public_content_t</span>:s0 /tutu/
[root@localhost ~]# vim /etc/sysconfig/selinux <span style="color:#3366FF;"> ##修改selinux的值为disabled</span>
[root@localhost ~]# reboot <span style="color:#3366FF;"> ##重启,使selinux的值生效</span>
[root@localhost ~]# vim /etc/sysconfig/selinux <span style="color:#3366FF;">##修改selinux的值为enforcing</span>
[root@localhost ~]# reboot
[root@localhost ~]# ls -Zd /tutu/
drwxr-xr-x. root root unconfined_u:object_r:<span style="color:#CC0000;">default_t</span>:s0 /tutu/
更改目录本身及其内容的安全上下文类型
[root@localhost ~]# ls -Zd /tutu/
drwxr-xr-x. root root unconfined_u:object_r:<span style="color:#CC0000;">default_t</span>:s0 /tutu/
[root@localhost ~]# ls -Zd /var/ftp/
drwxr-xr-x. root root system_u:object_r:public_content_t:s0 /var/ftp/
[root@localhost ~]# semanage fcontext -l | grep /var/ftp <span style="color:#3366FF;"> ##查看目录/var/ftp的所有内容的安全上下文</span>
<span style="color:#CC0000;">/var/ftp(/.*)? all files system_u:object_r:public_content_t:s0 </span>
/var/ftp/bin(/.*)? all files system_u:object_r:bin_t:s0
/var/ftp/etc(/.*)? all files system_u:object_r:etc_t:s0
/var/ftp/lib(/.*)? all files system_u:object_r:lib_t:s0
/var/ftp/lib/ld[^/]*\.so(\.[^/]*)* regular file system_u:object_r:ld_so_t:s0
[root@localhost ~]# semanage fcontext -l | grep /tutu <span style="color:#3366FF;"> ##查看目录/tutu本身及其内容的安全上下文,目录/tutu在默认情况下没有安全上下文</span>
[root@localhost ~]# semanage fcontext -a -t public_content_t '/tutu(/.*)?'
<span style="color:#3366FF;">##-a 添加 -t 更改类型
##更改目录/tutu本身及其内容的安全上下文类型
##/tutu(/.*)? === /tutu/* === /tutu/*/*/*.... 祥见正则表达式</span>
[root@localhost ~]# semanage fcontext -l | grep /tutu
/tutu(/.*)? all files system_u:object_r:public_content_t:s0
[root@localhost ~]# restorecon -FvvR /tutu/ <span style="color:#3366FF;">##用来恢复SElinux文件属性,即恢复文件的安全上下文</span>
restorecon reset /tutu context unconfined_u:object_r:<span style="color:#CC0000;">default_t</span>:s0<span style="color:#CC0000;">-></span>system_u:object_r:<span style="color:#CC0000;">public_content_t</span>:s0
restorecon reset /tutu/butterfly context unconfined_u:object_r:<span style="color:#CC0000;">default_t</span>:s0<span style="color:#CC0000;">-></span>system_u:object_r:<span style="color:#CC0000;">public_content_t</span>:s0
[root@localhost ~]# lftp 172.25.254.229
lftp 172.25.254.229:~> ls
-rw-r--r-- 1 0 0 0 May 14 02:02 butterfly
lftp 172.25.254.229:/> quit
[root@localhost ~]# touch /.autorelabel <span style="color:#3366FF;">##建立该文件的作用是使得系统在重启时就会对整个文件系统进行relabeling</span>
[root@localhost ~]# 
命令restorecon参数祥解
-i:<span style="color:#3366FF;">忽略不存在的文件</span>
-f:<span style="color:#3366FF;">infilename 文件 infilename 中记录要处理的文件</span>
-e:<span style="color:#3366FF;">directory 排除目录</span>
-R/-r:<span style="color:#3366FF;">递归处理目录</span>
-n:不改变文件标签
-o/outfilename:<span style="color:#3366FF;">保存文件列表到 outfilename,在文件不正确的情况下</span>
-v:<span style="color:#3366FF;">将过程显示到屏幕上</span>
-F:<span style="color:#3366FF;">强制恢复文件安全语境</span>semanage fcontext -a -t public_content_t '/tutu/' <span style="color:#CC0000;">##该命令执行后,看上去将安全上下文更改成功了,实际上并没有</span>semanage fcontext -a -t public_content_t '/tutu(/.*)?' <span style="color:#CC0000;">##该命令执行后,是将本目录及其内容的安全上下文进行成功更改</span>证明实验:
[root@localhost ~]# mkdir /tutu
[root@localhost ~]# ls -Zd /tutu/
drwxr-xr-x. root root unconfined_u:object_r:<span style="color:#CC0000;">default_t</span>:s0 /tutu/
[root@localhost ~]# semanage fcontext -a -t public_content_t '/tutu/'
[root@localhost ~]# semanage fcontext -l | grep /tutu
<span style="color:#CC0000;">/tutu/ all files system_u:object_r:public_content_t:s0
</span>[root@localhost ~]# touch /tutu/butterbly{1..3}
[root@localhost ~]# restorecon -FvvR /tutu/
restorecon reset /tutu context unconfined_u:object_r:<span style="color:#CC0000;">default_t</span>:s0<span style="color:#CC0000;">-></span>system_u:object_r:<span style="color:#CC0000;">default_t</span>:s0
restorecon reset /tutu/butterbly1 context unconfined_u:object_r:<span style="color:#CC0000;">default_</span>t:s0<span style="color:#CC0000;">-></span>system_u:object_r:<span style="color:#CC0000;">default_t</span>:s0
restorecon reset /tutu/butterbly2 context unconfined_u:object_r:<span style="color:#CC0000;">default_t</span>:s0<span style="color:#CC0000;">-></span>system_u:object_r:<span style="color:#CC0000;">default_t</span>:s0
restorecon reset /tutu/butterbly3 context unconfined_u:object_r:<span style="color:#CC0000;">default_t</span>:s0<span style="color:#CC0000;">-></span>system_u:object_r:<span style="color:#CC0000;">default_t</span>:s0
[root@localhost ~]# ls -Z /tutu/
-rw-r--r--. root root system_u:object_r:<span style="color:#CC0000;">default_t</span>:s0 butterbly1
-rw-r--r--. root root system_u:object_r:<span style="color:#CC0000;">default_t</span>:s0 butterbly2
-rw-r--r--. root root system_u:object_r:<span style="color:#CC0000;">default_t</span>:s0 butterbly3
[root@localhost ~]# semanage fcontext -a -t public_content_t '/tutu(/.*)?'
[root@localhost ~]# restorecon -FvvR /tutu/
restorecon reset /tutu context system_u:object_r:<span style="color:#CC0000;">default_t</span>:s0<span style="color:#CC0000;">-></span>system_u:object_r:<span style="color:#CC0000;">public_content_t</span>:s0
restorecon reset /tutu/butterbly1 context system_u:object_r:<span style="color:#CC0000;">default_t</span>:s0<span style="color:#CC0000;">-></span>system_u:object_r:<span style="color:#CC0000;">public_content_t</span>:s0
restorecon reset /tutu/butterbly2 context system_u:object_r:<span style="color:#CC0000;">default_t</span>:s0<span style="color:#CC0000;">-></span>system_u:object_r:<span style="color:#CC0000;">public_content_t</span>:s0
restorecon reset /tutu/butterbly3 context system_u:object_r:<span style="color:#CC0000;">default_t</span>:s0<span style="color:#CC0000;">-></span>system_u:object_r:<span style="color:#CC0000;">public_content_t</span>:s0
[root@localhost ~]# ls -Z /tutu/
-rw-r--r--. root root system_u:object_r:<span style="color:#CC0000;">public_content_t</span>:s0 butterbly1
-rw-r--r--. root root system_u:object_r:<span style="color:#CC0000;">public_content_t</span>:s0 butterbly2
-rw-r--r--. root root system_u:object_r:<span style="color:#CC0000;">public_content_t</span>:s0 butterbly3
[root@localhost ~]#

三、关于/var/log/messages和/var/log/audit/audit.log在vsftpd服务方面的区别
/var/log/messages ##日志的存放,当访问ftp://ip出现报错时,此文件中会有报错的解决方法,但是安全性不高
/var/log/audit/audit.log ##审计消息存放处,没有报错的解决方法
[root@localhost ~]# cd /var/ftp/
[root@localhost ftp]# ls
butterfly pub tutu
[root@localhost ftp]# rm -fr *
[root@localhost ftp]# > /var/log/messages
[root@localhost ftp]# cat /var/log/messages
[root@localhost ftp]# touch /mnt/tutu
[root@localhost ftp]# ls /mnt/
tutu
[root@localhost ftp]# mv /mnt/tutu /var/ftp/
[root@localhost ftp]# ls -Z
-rw-r--r--. root root unconfined_u:object_r:<span style="color:#CC0000;">mnt_t</span>:s0 tutu
[root@localhost ftp]# getenforce
Enforcing
[root@localhost ftp]# lftp 172.25.254.229
lftp 172.25.254.229:~> ls
lftp 172.25.254.229:/> quit
[root@localhost ftp]# > /var/log/messages
[root@localhost ftp]# cat /var/log/messages
[root@localhost ftp]# getenforce
Permissive
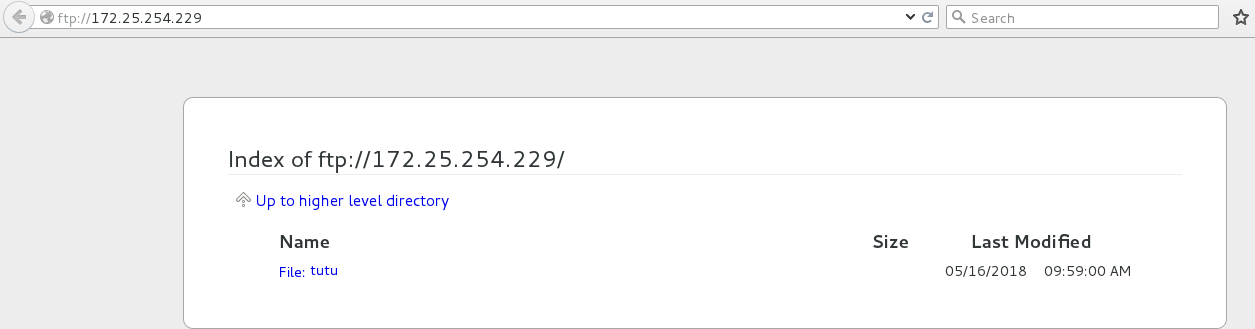
[root@localhost ftp]# lftp 172.25.254.229
<span style="color:#3366FF;">##当SElinux的值为警告时,还是可以看到目录/var/ftp下的文件,但是会有报错,报错信息在/var/log/messages中</span>
lftp 172.25.254.229:~> ls
-rw-r--r-- 1 0 0 0 May 16 09:59 tutu
lftp 172.25.254.229:/> quit
当SElinux值为Enforcing时,看不到任何文件
当SElinux值为Permissive时,可以看到文件
然后查看日志结果如下
<span style="color:#3366FF;">##设置SElinux值为Permissive后,用浏览器测试</span>
[root@localhost ftp]# cat /var/log/messages
<span style="color:#3366FF;">##日志内容略其他部分,以下的日志内容就是报错的解决方法</span>
Then execute:
<span style="color:#CC0000;">restorecon -v '$FIX_TARGET_PATH'</span>
***** Plugin catchall (7.64 confidence) suggests **************************
If you believe that vsftpd should be allowed getattr access on the file by default.
Then you should report this as a bug.
You can generate a local policy module to allow this access.
Do
allow this access for now by executing:
# grep vsftpd <span style="color:#CC0000;">/var/log/audit/audit.log</span> | audit2allow -M mypol
# semodule -i mypol.pp
[root@localhost ftp]# cat /var/log/audit/audit.log
<span style="color:#CC0000;">type=AVC msg=audit(1526469623.797:1978): avc: denied { getattr } for pid=1269 comm="vsftpd" path="/tutu" dev="vda1" ino=8846773 scontext=system_u:system_r:ftpd_t:s0-s0:c0.c1023 tcontext=unconfined_u:object_r:mnt_t:s0 tclass=file
type=SYSCALL msg=audit(1526469623.797:1978): arch=c000003e syscall=6 success=yes exit=0 a0=7f19dfeba660 a1=7f19dfec27e0 a2=7f19dfec27e0 a3=0 items=0 ppid=1267 pid=1269 auid=4294967295 uid=14 gid=50 euid=14 suid=14 fsuid=14 egid=50 sgid=50 fsgid=50 tty=(none) ses=4294967295 comm="vsftpd" exe="/usr/sbin/vsftpd" subj=system_u:system_r:ftpd_t:s0-s0:c0.c1023 key=(null)
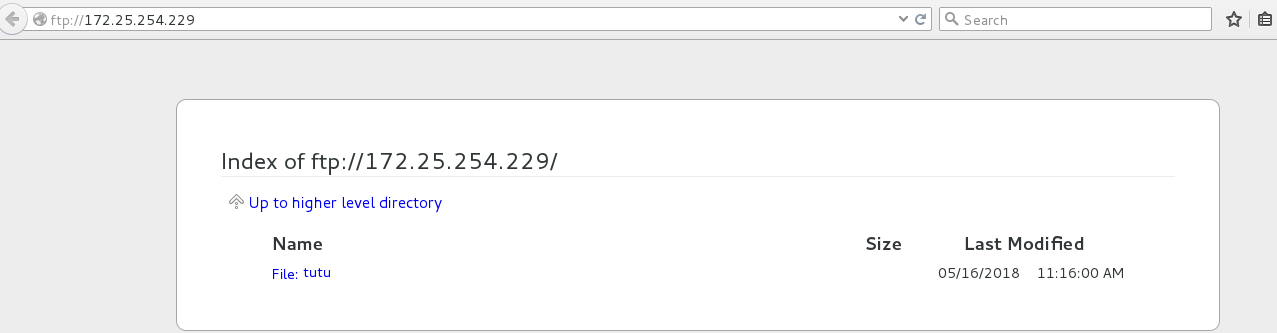
</span>[root@localhost ftp]# restorecon -v /var/ftp/*
restorecon reset /var/ftp/tutu context unconfined_u:object_r:mnt_t:s0->unconfined_u:object_r:public_content_t:s0
[root@localhost ftp]# > /var/log/messages
[root@localhost ftp]# > /var/log/audit/audit.log
<span style="color:#3366FF;">##此时进行浏览器测试</span>
[root@localhost ftp]# cat /var/log/audit/audit.log
[root@localhost ftp]# cat /var/log/messages
[root@localhost ftp]# lftp 172.25.254.229
lftp 172.25.254.229:~> ls
-rw-r--r-- 1 0 0 0 May 16 09:59 tutu
lftp 172.25.254.229:/> quit
[root@localhost ftp]# ls -Z
-rw-r--r--. root root unconfined_u:object_r:public_content_t:s0 tutu
四、协议端口
1.什么是协议端口?
如果把IP地址比作一间房子,端口就是出入这间房子的门。真正的房子只有几个门,但是一个IP地址的端口可以有65536(即:2^16)个之多,端口是通过端口号来标记的,端口号只有整数,范围是从0 到65535(2^16-1)。本地操作系统会给那些有需求的进程分配协议端口(即我们常说的端口),每个协议端口有一个正整数标识,如:80,139,445,等等。当目的主机接收到数据包后,将根据报文首部的目的端口号,把数据发送到相应端口,而与此端口相对应的那个进程将会领取数据并等待下一组数据的到来。
2.协议端口的查找与更改
该实验说明了更改的端口需要添加,才会生效
注意:新添加的端口不能是系统中已存在的!!!
[root@localhost ~]# yum install httpd -y
Loaded plugins: langpacks
<span style="color:#3366FF;">##安装过程略</span>
Complete!
[root@localhost ~]# cat /etc/services | grep http <span style="color:#3366FF;">##查看httpd服务的所有端口(信息较为详细)</span>
# http://www.iana.org/assignments/port-numbers
http 80/tcp www www-http # WorldWideWeb HTTP
http 80/udp www www-http # HyperText Transfer Protocol
http 80/sctp # HyperText Transfer Protocol
https 443/tcp # http protocol over TLS/SSL
https 443/udp # http protocol over TLS/SSL
https 443/sctp # http protocol over TLS/SSL
<span style="color:#3366FF;">##信息比较多,这里只显示部分</span>
[root@localhost ftp]# semanage port -l | grep http <span style="color:#3366FF;">##列出httpd的所有端口,没有上一个命令的信息详细</span>
http_cache_port_t tcp 8080, 8118, 8123, 10001-10010
http_cache_port_t udp 3130
http_port_t tcp 80, 81, 443, 488, 8008, 8009, 8443, 9000
pegasus_http_port_t tcp 5988
pegasus_https_port_t tcp 5989
[root@localhost ftp]#
[root@localhost ~]# vim /etc/httpd/conf/httpd.conf
<span style="color:#3366FF;">##修改httpd协议的端口,第42行,该实验是将80改为6666</span>
[root@localhost ~]# systemctl restart httpd
Job for httpd.service failed. See 'systemctl status httpd.service' and 'journalctl -xn' for details.
<span style="color:#3366FF;">##重启httpd失败,查看SElinux值</span>
[root@localhost ~]# getenforce
Enforcing
[root@localhost ~]# setenforce 0 <span style="color:#3366FF;"> ##设置SElinux值为Permissive</span>
[root@localhost ~]# systemctl restart httpd <span style="color:#3366FF;"> ##重启httpd服务成功</span>
[root@localhost ~]# semanage port -l | grep http <span style="color:#3366FF;"> ##列出httpd的所有端口,可见没有6666这个端口</span>
http_cache_port_t tcp 8080, 8118, 8123, 10001-10010
http_cache_port_t udp 3130
http_port_t tcp 80, 81, 443, 488, 8008, 8009, 8443, 9000
pegasus_http_port_t tcp 5988
pegasus_https_port_t tcp 5989
[root@localhost ~]# semanage port -a -t http_port_t -p tcp 6666
<span style="color:#3366FF;">##-a 添加,-t 类型,-p portocol协议
##将6666添加为httpd的tcp协议的http_port_t的端口</span>
[root@localhost ~]# semanage port -l | grep http
http_cache_port_t tcp 8080, 8118, 8123, 10001-10010
http_cache_port_t udp 3130
http_port_t tcp <span style="color:#CC0000;">6666</span>, 80, 81, 443, 488, 8008, 8009, 8443, 9000 <span style="color:#3366FF;"> ##添加6666端口成功</span>
pegasus_http_port_t tcp 5988
pegasus_https_port_t tcp 5989
[root@localhost ~]# setenforce 1
[root@localhost ~]# systemctl restart httpd <span style="color:#3366FF;"> ##当SElinux值为Enforcing时,成功重启服务</span>
[root@localhost ~]#