- 1Joplin Typora 粘贴图片 | 当使用Typora作为Joplin编辑器时,如何粘贴图片并上传到Joplin服务器,替换链接
- 22024年最全Redis配置项汇总(超级详细)_配置库及配置项列表示例,2024年抓住金三银四涨薪好时机_redis参数配置
- 3实验七:定时/计数器8253、8254_8253定时器计数器实验
- 4LORA技术学习 一_lora 空中波特率
- 5XXE外部实体引入漏洞原理及复现_xml外部实体注入漏洞怎么修复
- 6忆龙2009:详解SSH的工作流程_简述ssh协议在整个通信中,服务器端和客户端需要经历的五个阶段
- 7Hadoop实验——熟悉常用的HDFS操作_hdfs的基本操作实验报告
- 8Keil在线或使用调试器调试仿真教程_keil在线调试
- 9SQL Server 查询处理过程_sql server怎么把调试改成查询
- 10企业跨境文件传输的核心痛点,怎样保证稳定可靠的传输性能?
Ubuntu系统离线安装RKE2+Rancher2.7.5全过程记录_rke2 安装
赞
踩
安装前准备
| Hostname | IP | Note |
|---|---|---|
| mu01 | 192.168.1.20 | 部署私有镜像库,有外网 |
| cu01 | 192.168.1.21 | 部署rke2-server,无外网 |
| cu02 | 192.168.1.22 | 部署rke2-server,无外网 |
| cu03 | 192.168.1.23 | 部署rke2-server,无外网 |
| cu04 | 192.168.1.24 | 部署kubernetes |
| cu05 | 192.168.1.25 | 部署kubernetes |
1.1 部署私有镜像仓库
在一台能够访问docker.io和quay.io的服务器mu01上部署该私有镜像仓库。
参考如下链接,本人对比了Harbor,Nexus3和Jfrog Contianer Registry, 个人倾向于使用JCR,可以自动缓存远程镜像,且官方资料较全面:
https://blog.csdn.net/u010438035/article/details/131442003
https://blog.csdn.net/u010438035/article/details/131537945
https://blog.csdn.net/u010438035/article/details/131560407
私有镜像仓库开启匿名访问,同时配置docker.io 和 quay.io的remote repository
将私有镜像仓库服务器的证书复制到cu01-cu05所有节点
cp server.crt /usr/local/share/ca-certificates/server.crt
update-ca-certificates
- 1
- 2
1.2 在cu01-05服务器执行如下配置
apt-get -y update apt-get -y dist-upgrade apt-get -y install chrony ipset ipvsadm #sudo 替换{{username}}为ubuntu系统登录用户 cat > /etc/sudoers.d/{{username}}<< EOF # add in user AFTER the sudo and admin group {{username}} ALL=(ALL) NOPASSWD: ALL EOF #hosts cat >> /etc/hosts << EOF 192.168.1.21 cu01 192.168.1.22 cu02 192.168.1.23 cu03 192.168.1.22 cu04 192.168.1.23 cu05 EOF #time chronyc sources -v timedatectl set-timezone Asia/Shanghai #swap swapoff -a sed -ri 's/.*swap.*/#&/' /etc/fstab #kernel cat > /etc/modules-load.d/k8s.conf <<EOF overlay br_netfilter EOF modprobe overlay modprobe br_netfilter cat > /etc/sysctl.d/k8s.conf <<EOF net.bridge.bridge-nf-call-iptables = 1 net.bridge.bridge-nf-call-ip6tables = 1 net.ipv4.ip_forward = 1 EOF sysctl --system #ipvs cat > /etc/modules-load.d/ipvs.conf << EOF modprobe -- ip_vs modprobe -- ip_vs_rr modprobe -- ip_vs_wrr modprobe -- ip_vs_sh modprobe -- nf_conntrack EOF modprobe -- ip_vs modprobe -- ip_vs_rr modprobe -- ip_vs_wrr modprobe -- ip_vs_sh modprobe -- nf_conntrack cat >> /etc/modules <<EOF ip_vs_sh ip_vs_wrr ip_vs_rr ip_vs nf_conntrack EOF
- 1
- 2
- 3
- 4
- 5
- 6
- 7
- 8
- 9
- 10
- 11
- 12
- 13
- 14
- 15
- 16
- 17
- 18
- 19
- 20
- 21
- 22
- 23
- 24
- 25
- 26
- 27
- 28
- 29
- 30
- 31
- 32
- 33
- 34
- 35
- 36
- 37
- 38
- 39
- 40
- 41
- 42
- 43
- 44
- 45
- 46
- 47
- 48
- 49
- 50
- 51
- 52
- 53
- 54
- 55
- 56
- 57
- 58
- 59
- 60
- 61
- 62
- 63
- 64
- 65
- 66
- 67
离线安装RKE2
参考官方链接:https://docs.rke2.io/zh/install/airgap
在mu01服务器下载相关安装包和脚本
curl -OLs https://github.com/rancher/rke2/releases/download/v1.26.5%2Brke2r1/rke2-images.linux-amd64.tar.zst
curl -OLs https://github.com/rancher/rke2/releases/download/v1.26.5%2Brke2r1/rke2.linux-amd64.tar.gz
curl -OLs https://github.com/rancher/rke2/releases/download/v1.26.5%2Brke2r1/sha256sum-amd64.txt
curl -sfL https://get.rke2.io --output install.sh
- 1
- 2
- 3
- 4
- 5
在cu01-03服务器执行
mkdir /root/rke2-artifacts && cd /root/rke2-artifacts/
#scp 从mu01将前面下载的4个文件复制到上述目录
chmod +x install.sh
mkdir -p /etc/rancher/rke2
cat > /etc/rancher/rke2/registries.yaml << EOF
mirrors:
"*":
endpoint:
- "https://192.168.1.20:9443"
EOF
- 1
- 2
- 3
- 4
- 5
- 6
- 7
- 8
- 9
- 10
- 11
参考《如何使用国内资源在 RKE2 上安装 Rancher HA》
https://www.cnblogs.com/rancherlabs/p/15955317.html
2.1 创建第一个 server 节点
在cu01服务器执行
cat > /etc/rancher/rke2/config.yaml <<EOF ##编辑配置文件
token: rke2-create-token ##tocken可以后面修改;
tls-san: 192.168.1.21 ##这里使用第一个节点ip;
system-default-registry: "192.168.1.20:9443" ##私有镜像库地址;
EOF
INSTALL_RKE2_ARTIFACT_PATH=/root/rke2-artifacts sh install.sh
systemctl start rke2-server && systemctl enable rke2-server
- 1
- 2
- 3
- 4
- 5
- 6
- 7
- 8
- 9
2.2 添加其他 server 节点
在cu02-03服务器执行
cat > /etc/rancher/rke2/config.yaml <<EOF
server: https://192.168.1.21:9345 ##添加首个节点的server地址;
token: "K10d3604865eb2d6abeec1ca0cf6c5463631683d750e721b8394ee63bc3c9e8d75a::server:bddd9454003b396829d27dc79dca324b" ##填写第一个server节点的token,通过在第一个节点查看/var/lib/rancher/rke2/server/token文件获得;
tls-san: 192.168.1.21 ##这里使用第一个节点ip
system-default-registry: "192.168.1.20:9443" ##私有镜像库地址;
EOF
INSTALL_RKE2_ARTIFACT_PATH=/root/rke2-artifacts sh install.sh
systemctl start rke2-server && systemctl enable rke2-server
- 1
- 2
- 3
- 4
- 5
- 6
- 7
- 8
- 9
- 10
2.3 验证集群
mkdir ~/.kube
ln -s /etc/rancher/rke2/rke2.yaml ~/.kube/config
chmod 600 ~/.kube/config
ln -s /var/lib/rancher/rke2/agent/etc/crictl.yaml /etc/crictl.yaml
ln -s /var/lib/rancher/rke2/bin/kubectl /usr/bin/kubectl
ln -s /var/lib/rancher/rke2/bin/crictl /usr/bin/crictl
kubectl get node
crictl ps
crictl images
- 1
- 2
- 3
- 4
- 5
- 6
- 7
- 8
- 9
- 10
但需要注意的是 RKE2 官方最佳实践表明,高可用集群应该由统一的 LB 入口访问,这样才是真正的高可用。
离线安装Rancher2.7.5
在mu01服务器下载相关安装包和脚本
# 先参考官方文档安装helm:https://helm.sh/docs/intro/install/ wget https://get.helm.sh/helm-v3.12.1-linux-amd64.tar.gz tar -zxvf helm-v3.12.1-linux-amd64.tar.gz # Find the helm binary in the unpacked directory, and move it to its desired destination mv linux-amd64/helm /usr/local/bin/helm helm repo add rancher-latest https://releases.rancher.com/server-charts/latest mkdir ~/helm helm fetch rancher-latest/rancher helm repo add jetstack https://charts.jetstack.io helm repo update helm fetch jetstack/cert-manager --version v1.12.2 curl -L -o cert-manager-crd.yaml https://github.com/cert-manager/cert-manager/releases/download/v1.12.2/cert-manager.crds.yaml
- 1
- 2
- 3
- 4
- 5
- 6
- 7
- 8
- 9
- 10
- 11
- 12
- 13
- 14
- 15
- 16
把上面在mu01下载的文件都复制到cu01,同时把mu01的/usr/local/bin/helm复制到cu01中 /usr/local/bin/helm
3.1 安装 Cert-Manager
在cu01服务器执行
kubectl create namespace cert-manager
kubectl apply -f cert-manager-crd.yaml
helm install cert-manager ./cert-manager-v1.12.2.tgz \
--namespace cert-manager \
--set image.repository=quay.io/jetstack/cert-manager-controller \
--set webhook.image.repository=quay.io/jetstack/cert-manager-webhook \
--set cainjector.image.repository=quay.io/jetstack/cert-manager-cainjector \
--set startupapicheck.image.repository=quay.io/jetstack/cert-manager-ctl
- 1
- 2
- 3
- 4
- 5
- 6
- 7
- 8
3.2 添加 TLS 密文发布证书文件
参考链接:https://docs.rancher.cn/docs/rancher2/installation/resources/advanced/self-signed-ssl/_index/
cat > create_self-signed-cert.sh <<"EOF" #!/bin/bash -e help () { echo ' ================================================================ ' echo ' --ssl-domain: 生成ssl证书需要的主域名,如不指定则默认为www.rancher.local,如果是ip访问服务,则可忽略;' echo ' --ssl-trusted-ip: 一般ssl证书只信任域名的访问请求,有时候需要使用ip去访问server,那么需要给ssl证书添加扩展IP,多个IP用逗号隔开;' echo ' --ssl-trusted-domain: 如果想多个域名访问,则添加扩展域名(SSL_TRUSTED_DOMAIN),多个扩展域名用逗号隔开;' echo ' --ssl-size: ssl加密位数,默认2048;' echo ' --ssl-cn: 国家代码(2个字母的代号),默认CN;' echo ' 使用示例:' echo ' ./create_self-signed-cert.sh --ssl-domain=www.test.com --ssl-trusted-domain=www.test2.com \ ' echo ' --ssl-trusted-ip=1.1.1.1,2.2.2.2,3.3.3.3 --ssl-size=2048 --ssl-date=3650' echo ' ================================================================' } case "$1" in -h|--help) help; exit;; esac if [[ $1 == '' ]];then help; exit; fi CMDOPTS="$*" for OPTS in $CMDOPTS; do key=$(echo ${OPTS} | awk -F"=" '{print $1}' ) value=$(echo ${OPTS} | awk -F"=" '{print $2}' ) case "$key" in --ssl-domain) SSL_DOMAIN=$value ;; --ssl-trusted-ip) SSL_TRUSTED_IP=$value ;; --ssl-trusted-domain) SSL_TRUSTED_DOMAIN=$value ;; --ssl-size) SSL_SIZE=$value ;; --ssl-date) SSL_DATE=$value ;; --ca-date) CA_DATE=$value ;; --ssl-cn) CN=$value ;; esac done # CA相关配置 CA_DATE=${CA_DATE:-3650} CA_KEY=${CA_KEY:-cakey.pem} CA_CERT=${CA_CERT:-cacerts.pem} CA_DOMAIN=cattle-ca # ssl相关配置 SSL_CONFIG=${SSL_CONFIG:-$PWD/openssl.cnf} SSL_DOMAIN=${SSL_DOMAIN:-'www.rancher.local'} SSL_DATE=${SSL_DATE:-3650} SSL_SIZE=${SSL_SIZE:-2048} ## 国家代码(2个字母的代号),默认CN; CN=${CN:-CN} SSL_KEY=$SSL_DOMAIN.key SSL_CSR=$SSL_DOMAIN.csr SSL_CERT=$SSL_DOMAIN.crt echo -e "\033[32m ---------------------------- \033[0m" echo -e "\033[32m | 生成 SSL Cert | \033[0m" echo -e "\033[32m ---------------------------- \033[0m" if [[ -e ./${CA_KEY} ]]; then echo -e "\033[32m ====> 1. 发现已存在CA私钥,备份"${CA_KEY}"为"${CA_KEY}"-bak,然后重新创建 \033[0m" mv ${CA_KEY} "${CA_KEY}"-bak openssl genrsa -out ${CA_KEY} ${SSL_SIZE} else echo -e "\033[32m ====> 1. 生成新的CA私钥 ${CA_KEY} \033[0m" openssl genrsa -out ${CA_KEY} ${SSL_SIZE} fi if [[ -e ./${CA_CERT} ]]; then echo -e "\033[32m ====> 2. 发现已存在CA证书,先备份"${CA_CERT}"为"${CA_CERT}"-bak,然后重新创建 \033[0m" mv ${CA_CERT} "${CA_CERT}"-bak openssl req -x509 -sha256 -new -nodes -key ${CA_KEY} -days ${CA_DATE} -out ${CA_CERT} -subj "/C=${CN}/CN=${CA_DOMAIN}" else echo -e "\033[32m ====> 2. 生成新的CA证书 ${CA_CERT} \033[0m" openssl req -x509 -sha256 -new -nodes -key ${CA_KEY} -days ${CA_DATE} -out ${CA_CERT} -subj "/C=${CN}/CN=${CA_DOMAIN}" fi echo -e "\033[32m ====> 3. 生成Openssl配置文件 ${SSL_CONFIG} \033[0m" cat > ${SSL_CONFIG} <<EOM [req] req_extensions = v3_req distinguished_name = req_distinguished_name [req_distinguished_name] [ v3_req ] basicConstraints = CA:FALSE keyUsage = nonRepudiation, digitalSignature, keyEncipherment extendedKeyUsage = clientAuth, serverAuth EOM if [[ -n ${SSL_TRUSTED_IP} || -n ${SSL_TRUSTED_DOMAIN} || -n ${SSL_DOMAIN} ]]; then cat >> ${SSL_CONFIG} <<EOM subjectAltName = @alt_names [alt_names] EOM IFS="," dns=(${SSL_TRUSTED_DOMAIN}) dns+=(${SSL_DOMAIN}) for i in "${!dns[@]}"; do echo DNS.$((i+1)) = ${dns[$i]} >> ${SSL_CONFIG} done if [[ -n ${SSL_TRUSTED_IP} ]]; then ip=(${SSL_TRUSTED_IP}) for i in "${!ip[@]}"; do echo IP.$((i+1)) = ${ip[$i]} >> ${SSL_CONFIG} done fi fi echo -e "\033[32m ====> 4. 生成服务SSL KEY ${SSL_KEY} \033[0m" openssl genrsa -out ${SSL_KEY} ${SSL_SIZE} echo -e "\033[32m ====> 5. 生成服务SSL CSR ${SSL_CSR} \033[0m" openssl req -sha256 -new -key ${SSL_KEY} -out ${SSL_CSR} -subj "/C=${CN}/CN=${SSL_DOMAIN}" -config ${SSL_CONFIG} echo -e "\033[32m ====> 6. 生成服务SSL CERT ${SSL_CERT} \033[0m" openssl x509 -sha256 -req -in ${SSL_CSR} -CA ${CA_CERT} \ -CAkey ${CA_KEY} -CAcreateserial -out ${SSL_CERT} \ -days ${SSL_DATE} -extensions v3_req \ -extfile ${SSL_CONFIG} echo -e "\033[32m ====> 7. 证书制作完成 \033[0m" echo echo -e "\033[32m ====> 8. 以YAML格式输出结果 \033[0m" echo "----------------------------------------------------------" echo "ca_key: |" cat $CA_KEY | sed 's/^/ /' echo echo "ca_cert: |" cat $CA_CERT | sed 's/^/ /' echo echo "ssl_key: |" cat $SSL_KEY | sed 's/^/ /' echo echo "ssl_csr: |" cat $SSL_CSR | sed 's/^/ /' echo echo "ssl_cert: |" cat $SSL_CERT | sed 's/^/ /' echo echo -e "\033[32m ====> 9. 附加CA证书到Cert文件 \033[0m" cat ${CA_CERT} >> ${SSL_CERT} echo "ssl_cert: |" cat $SSL_CERT | sed 's/^/ /' echo echo -e "\033[32m ====> 10. 重命名服务证书 \033[0m" echo "cp ${SSL_DOMAIN}.key tls.key" cp ${SSL_DOMAIN}.key tls.key echo "cp ${SSL_DOMAIN}.crt tls.crt" cp ${SSL_DOMAIN}.crt tls.crt EOF
- 1
- 2
- 3
- 4
- 5
- 6
- 7
- 8
- 9
- 10
- 11
- 12
- 13
- 14
- 15
- 16
- 17
- 18
- 19
- 20
- 21
- 22
- 23
- 24
- 25
- 26
- 27
- 28
- 29
- 30
- 31
- 32
- 33
- 34
- 35
- 36
- 37
- 38
- 39
- 40
- 41
- 42
- 43
- 44
- 45
- 46
- 47
- 48
- 49
- 50
- 51
- 52
- 53
- 54
- 55
- 56
- 57
- 58
- 59
- 60
- 61
- 62
- 63
- 64
- 65
- 66
- 67
- 68
- 69
- 70
- 71
- 72
- 73
- 74
- 75
- 76
- 77
- 78
- 79
- 80
- 81
- 82
- 83
- 84
- 85
- 86
- 87
- 88
- 89
- 90
- 91
- 92
- 93
- 94
- 95
- 96
- 97
- 98
- 99
- 100
- 101
- 102
- 103
- 104
- 105
- 106
- 107
- 108
- 109
- 110
- 111
- 112
- 113
- 114
- 115
- 116
- 117
- 118
- 119
- 120
- 121
- 122
- 123
- 124
- 125
- 126
- 127
- 128
- 129
- 130
- 131
- 132
- 133
- 134
- 135
- 136
- 137
- 138
- 139
- 140
- 141
- 142
- 143
- 144
- 145
- 146
- 147
- 148
- 149
- 150
- 151
- 152
- 153
- 154
- 155
- 156
- 157
- 158
- 159
chmod +x create_self-signed-cert.sh
# --ssl-domain: 生成ssl证书需要的主域名,如不指定则默认为www.rancher.local,如果是ip访问服务,则可忽略;
# --ssl-trusted-ip: 一般ssl证书只信任域名的访问请求,有时候需要使用ip去访问server,那么需要给ssl证书添加扩展IP,多个IP用逗号隔开;
# --ssl-trusted-domain: 如果想多个域名访问,则添加扩展域名(TRUSTED_DOMAIN),多个TRUSTED_DOMAIN用逗号隔开;
# --ssl-size: ssl加密位数,默认2048;
# --ssl-cn: 国家代码(2个字母的代号),默认CN;
使用示例:
./create_self-signed-cert.sh --ssl-domain=rancher.sslip.io --ssl-size=2048 --ssl-date=3650
kubectl -n cattle-system create secret tls tls-rancher-ingress \
--cert=tls.crt \
--key=tls.key
- 1
- 2
- 3
- 4
- 5
- 6
- 7
- 8
- 9
- 10
- 11
- 12
- 13
3.3 安装 Rancher
kubectl create namespace cattle-system
helm install rancher ./rancher-2.7.5.tgz --namespace cattle-system --set hostname=rancher.sslip.io --set cert-manager.version=v1.12.2 --set rancherImage=
docker.io/rancher/rancher --set systemDefaultRegistry=192.168.1.20:9443 --set useBundledSystemChart=true
kubectl -n cattle-system get pod
- 1
- 2
- 3
- 4
- 5
- 6
在生产环境中rancher.sslip.io要解析到负载均衡器对应的地址,这里仅用于测试,可以参考如下命令在cu04执行:
cat >> /etc/hosts << EOF
192.168.1.21 rancher.sslip.io
192.168.1.22 rancher.sslip.io
192.168.1.23 rancher.sslip.io
EOF
- 1
- 2
- 3
- 4
- 5
- 6
接着通过浏览器访问:https://rancher.sslip.io/
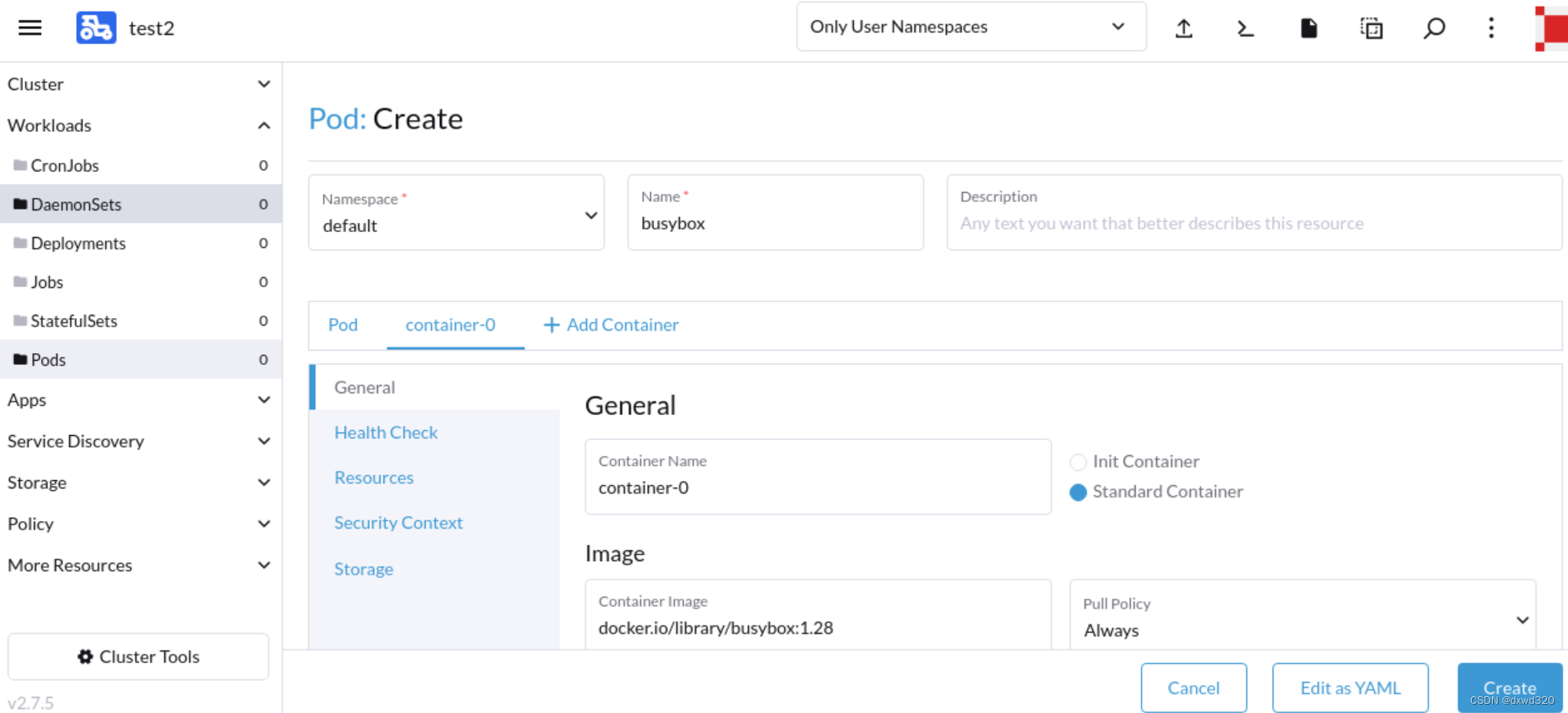
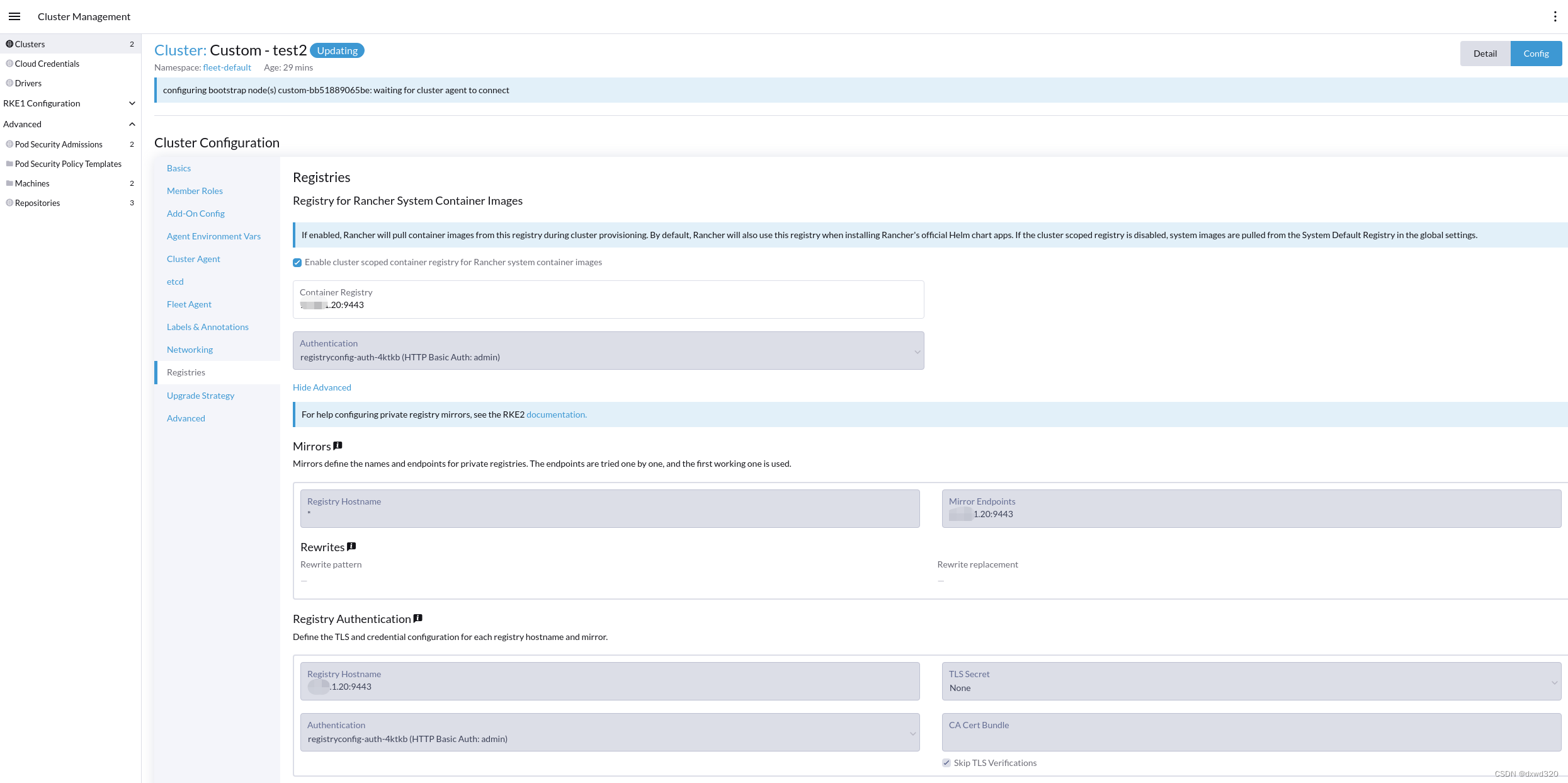
参考下图创建cluster
复制如图中的命令并在cu04执行
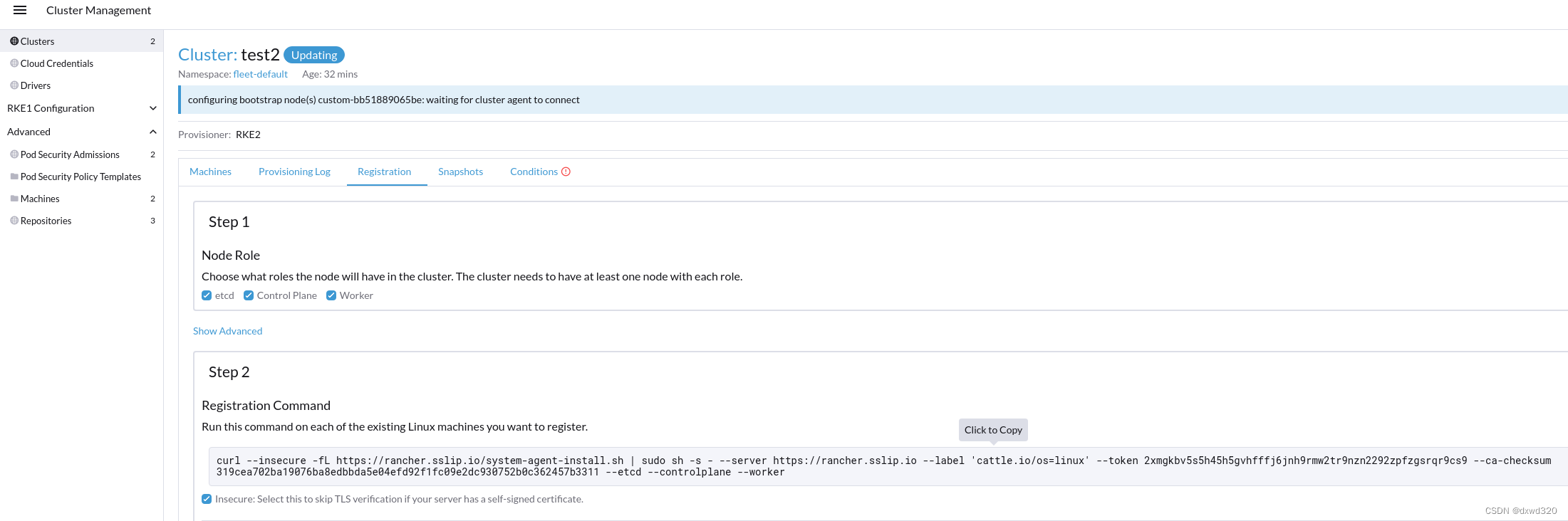
如果这里有报错:
curl failed to verify the legitimacy of the server
复制《3.2 添加 TLS 密文发布证书文件》步骤生成的cacerts.pem文件至cu04节点
修改上述命令类似:
curl --cacert cacerts.pem -fL https://rancher.sslip.io/system-agent-install.sh | sudo sh -s - --server https://rancher.sslip.io --label 'cattle.io/os=linux' --token gj6nntc5sznndbdpdlwntj7q46t4plm9dk58mnsvxmr2z7wp62zdx2 --ca-checksum 319cea702ba19076ba8edbbda5e04efd92f1fc09e2dc930752b0c362457b3311 --etcd --controlplane --worker
- 1
执行后如果发现卡在:Waiting for cluster agent to connect
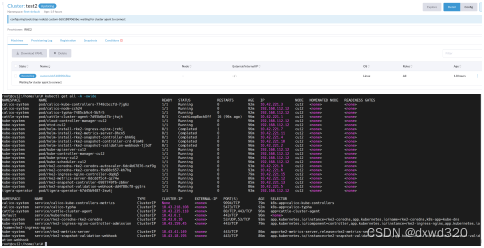
在cu04查看日志发现:
kubectl -n cattle-system logs pod/cattle-cluster-agent-7d95b6b47b-jtwjt
ERROR: https://rancher.sslip.io/ping is not accessible (Could not resolve host: rancher.sslip.io)
- 1
- 2
这是因为没有配置内部DNS造成的域名无法解析,可以参考官方文档临时规避:
Agent 无法连接 Rancher server:https://docs.rancher.cn/docs/rancher2/faq/install/_index/
kubectl -n cattle-system patch deployments cattle-cluster-agent --patch '{ "spec": { "template": { "spec": { "hostAliases": [ { "hostnames": [ "rancher.sslip.io" ], "ip": "192.168.1.21" } ] } } } }'
- 1
- 2
- 3
- 4
- 5
- 6
- 7
- 8
- 9
- 10
- 11
- 12
- 13
- 14
- 15
- 16
- 17
3.4 发布一个POD进行测试