- 1修改jar包文件并重新打包_android jar重新打包
- 2Golang框架:cobra_golang cobra
- 3第31篇-SAP MRP最小安全库存和服务水平的研究学习、思考_sap里service level
- 4bfs的Floodfill算法_floodfill算法例题
- 5GPT-4对编程开发的支持_gpt4可以写代码吗
- 6<网络安全>《68 微课堂<第9课 常见IT系统集成商简介>》
- 7Suno AI:如何使用应用程序通过 AI 创作精彩歌曲
- 8Django图书商城系统实战开发 - 实现个人中心管理_django个人中心
- 9python 机器人聊天_使用python构建您的第一个聊天机器人并将其集成到电报中
- 10vue3 自定义指令_vue3自定义指令流程
基于OpenSSL设计旁路解密HTTPS流量_openssl实现ssl解码
赞
踩
1 引言
1.1 编写目的
记录本次开发SSL/TLS加解密功能中对OpenSSL的二次开发和设计细节
1.2 背景
目前开发产品是以旁路方式接入网络,监控访问客户服务器的网络流量,为了支持对HTTPS数据的解析,需要开发解密TLS密文的功能。
通过实现对SSL/TLS协议的解析,加密数据的解密,可以提供明文的应用层数据为后续的特征检测、样本还原等功能提供支持。
1.3 参考资料
2 总体设计
2.1 需求概述
本次通过调研和选型,最终确定总体方案是基于OpenSSL 1.0.2u源码进行二次开发和设计,最终支持旁路接入流量,对流量进行解密的功能。
2.2 总体设计图
2.3 流程设计
为了实现以上的方案,需要对当前的OpenSSL源码进行如下一些定制化修改或重新设计:
- OpenSSL中已有的SSL/TLS协议解析功能,需要融入到现在项目代码的协议解析框架中。
- OpenSSL原有设计是支持客户端和服务器端的方式,如果旁路接入,客户端和服务器的流量都会接入,需要使用统一的接口,对双向的流量进行解析和解密。
- 因为是旁路接入,在SSL/TLS协商过程中,对部分协商细节需要进行改写或者裁剪。
- 目前进行的是单包解析,就是在SSL/TLS层之前已经完成对数据包的重组,在SSL/TLS层已经是按照最大传输单元大小的有序的数据包进行解析。因为TLS层的最大加密数据块大小是2^14字节,解密时必须按照加密块的大小进行解密,所以在传输层一定会进行分包,因此,在解密时,需要把分包的数据进行重组,然后再解密。
下边对以上几个功能详细介绍下具体的设计细节。
- 首先介绍下对旁路OpenSSL的总体设计:
在原有OpenSSL的设计是可以把OpenSSL分别部署到客户端或者服务端,使用OpenSSL中提供的客户端和服务端适配的接口,可以实现SSL/TLS建立连接、加解密等功能。
对于旁路OpenSSL来说,只存在解密的操作,当接入客户端请求的数据时,旁路OpenSSL扮演服务端的角色,对客户端的数据进行解析,获取计算密钥需要的参数,当接入服务端响应数据时,旁路OpenSSL扮演客户端的角色,对服务端的数据进行解析,获取计算密钥需要的参数。
为实现以上功能,目前基于对OpenSSL的服务端进行改写,OpenSSL的服务端读的操作流程不需要改动,可以把写的操作流程改为读取服务端响应数据,从而实现双向数据的解密功能。
2.4 功能描述
2.5 功能设计
2.5.1 SSL/TLS协议解析
在OpenSSL1.0.2u中已经有了对SSL/TLS协议的解析,本模块主要是把这部分功能融入到当前项目的协议解析框架中。
在当前协议解析的框架中,TCP层会通过端口号进行判断应用层协议类型,然后调用相应的应用层协议解析接口,并把应用层数据传输过去。
为了解析SSL/TLS协议,先参考RFC规范,提取需要的字段信息,定义如下结构体,记录相应的信息:
struct ssltls_private_area { u_int8_t *cache; //缓存, 为了缓存分包的数据 int cache_used_len; //目前缓存的数据长度 u_int32_t ssl_ack_seq; //记录数据包的ack号 u_int32_t ssl_seq; //记录数据包的seq号 u_int8_t ssltls_flg; struct TLSPlaintext tls_plaintext; //TLS记录层协议头部信息 struct ProtocolVersion temp_version; //TLS版本号 //client hello struct ProtocolVersion client_version; //记录客户端请求数据包的TLS版本号 struct HSRandom client_random; //客户端请求数据包的Random u_int8_t client_SessionID_len; //客户端请求数据包中的SessionID长度 u_int8_t client_SessionID[TLS_MAX_SESSION_ID_LEN]; //客户端请求数据包中的SessionID //server hello struct ProtocolVersion server_version; //记录服务端响应数据包的TLS版本号 struct HSRandom server_random; //服务端响应数据包的Random u_int8_t server_SessionID_len; //服务端响应数据包中的SessionID长度 u_int8_t server_SessionID[TLS_MAX_SESSION_ID_LEN]; //客服务端响应数据包中的SessionID u_int16_t server_CipherSuite; //加密套件 u_int8_t server_Compression; //压缩方法 //server certificates int server_CertificatesLen; //ssl info struct SSLSocketInfo ssl_info; //ssl连接信息 };
- 1
- 2
- 3
- 4
- 5
- 6
- 7
- 8
- 9
- 10
- 11
- 12
- 13
- 14
- 15
- 16
- 17
- 18
- 19
- 20
- 21
- 22
- 23
- 24
- 25
- 26
- 27
- 28
- 29
- 30
- 31
在SSL/TLS协议解析中,在解析SSL/TLS协商数据包时提取信息,填充以上结构体,关于TLS版本号、客户端和服务端的Random、SessionID等信息。
以上信息都在SSL/TLS协商的前两个数据包中,一个是客户端的请求数据包ClientHello,一个是服务端的响应数据包ServerHello。
//解析ClientHello子消息
static u_int8_t handshake_client_hello(Packet_t *packet, u_int8_t *data, int datalen)
//解析ServerHello子消息
static u_int8_t handshake_server_hello(Packet_t *packet, u_int8_t *data, int datalen)
- 1
- 2
- 3
- 4
在提取以上信息之后,需要调用ssl3_accept接口,这个接口是OpenSSL提供的TLS建立连接的接口,其中会完成整个TLS协商过程,关于对密码套件的解析,提取计算非对称加密、对称加密密钥需要的一些参数等,但是在调用接口前,需要把TLS层的数据保存到TLS的缓冲区。对于客户端请求数据包和服务端响应数据包,需要分别保存到读缓冲区和写缓冲区
//拷贝服务端响应数据到wbuff
int copy_skb_to_wbuff(int8_t *tdp_payload, int32_t tdp_payloadlen, SSL* s);
//拷贝客户端请求数据到rbuff
int copy_skb_to_rbuff(int8_t *tdp_payload, int32_t tdp_payloadlen, SSL* s);
- 1
- 2
- 3
- 4
2.5.2 SSL/TLS建立连接
SSL/TLS建立连接的过程主要调用ssl3_accept接口函数,函数中会解析不同的协商数据包,通过切换到不同的状态,直到最后状态变为SSL_ST_OK,表示SSL/TLS连接建立成功。
下边是整个协商过程中,在ssl3_accept接口函数中切换的状态:

在SessionID和SessionTicket会话恢复流程中,会有一些状态差异,因为恢复过程中,比如重新计算密钥等过程就不需要了,会复用之前会话的密钥等信息。
下边是改写后的ssl3_accept接口源码,因为函数源码实在太长,这里裁剪了一些主要流程中的代码,只介绍SSL/TLS的主要握手流程中的状态切换过程:
int ssl3_accept(SSL *s) { BUF_MEM *buf; unsigned long alg_k, Time = (unsigned long)time(NULL); void (*cb) (const SSL *ssl, int type, int val) = NULL; int ret = -1; int new_state, state, skip = 0; RAND_add(&Time, sizeof(Time), 0); ERR_clear_error(); clear_sys_error(); if (s->info_callback != NULL) cb = s->info_callback; else if (s->ctx->info_callback != NULL) cb = s->ctx->info_callback; #ifndef MODIFY_BY_VENUS_FLAG char pbuf[SSL3_RT_MAX_PLAIN_LENGTH + 1460] = {0}; int num = 0; int i = 0; int total_num = get_ssl3_ciphers_num(); #endif #ifdef MODIFY_BY_VENUS_FLAG //在调用ssl3_accept接口前已对ssl状态进行初始化,初始化状态为SSL_ST_ACCEPT|SSL_ST_BEFORE // s->in_handshake的值标识整个SSL/TLS握手状态是否完成,初始值为0,在调用ssl3_accept接口前会执行s->in_handshake++,在整个SSL/TLS握手过程中其值为1,如果SSL/TLS握手成功,会设置为0 /* init things to blank */ s->in_handshake++; if (!SSL_in_init(s) || SSL_in_before(s)) SSL_clear(s); #endif if (s->cert == NULL) { SSLerr(SSL_F_SSL3_ACCEPT, SSL_R_NO_CERTIFICATE_SET); return (-1); } #ifndef OPENSSL_NO_HEARTBEATS /* * If we're awaiting a HeartbeatResponse, pretend we already got and * don't await it anymore, because Heartbeats don't make sense during * handshakes anyway. */ if (s->tlsext_hb_pending) { s->tlsext_hb_pending = 0; s->tlsext_hb_seq++; } #endif for (;;) { state = s->state; switch (s->state) { case SSL_ST_RENEGOTIATE: s->renegotiate = 1; /* s->state=SSL_ST_ACCEPT; */ case SSL_ST_BEFORE: case SSL_ST_ACCEPT: case SSL_ST_BEFORE | SSL_ST_ACCEPT: case SSL_ST_OK | SSL_ST_ACCEPT: s->server = 1; if (cb != NULL) cb(s, SSL_CB_HANDSHAKE_START, 1); if ((s->version >> 8) != 3) { SSLerr(SSL_F_SSL3_ACCEPT, ERR_R_INTERNAL_ERROR); s->state = SSL_ST_ERR; return -1; } s->type = SSL_ST_ACCEPT; if (s->init_buf == NULL) { if ((buf = BUF_MEM_new()) == NULL) { ret = -1; s->state = SSL_ST_ERR; goto end; } if (!BUF_MEM_grow(buf, SSL3_RT_MAX_PLAIN_LENGTH)) { BUF_MEM_free(buf); ret = -1; s->state = SSL_ST_ERR; goto end; } s->init_buf = buf; } if (!ssl3_setup_buffers(s)) { ret = -1; s->state = SSL_ST_ERR; goto end; } s->init_num = 0; s->s3->flags &= ~TLS1_FLAGS_SKIP_CERT_VERIFY; s->s3->flags &= ~SSL3_FLAGS_CCS_OK; /* * Should have been reset by ssl3_get_finished, too. */ s->s3->change_cipher_spec = 0; if (s->state != SSL_ST_RENEGOTIATE) { /* * Ok, we now need to push on a buffering BIO so that the * output is sent in a way that TCP likes :-) */ if (!ssl_init_wbio_buffer(s, 1)) { ret = -1; s->state = SSL_ST_ERR; goto end; } //初始化摘要验证 if (!ssl3_init_finished_mac(s)) { ret = -1; s->state = SSL_ST_ERR; goto end; } //设置为第一个状态SSL3_ST_SR_CLNT_HELLO_A s->state = SSL3_ST_SR_CLNT_HELLO_A; s->ctx->stats.sess_accept++; } else if (!s->s3->send_connection_binding && !(s->options & SSL_OP_ALLOW_UNSAFE_LEGACY_RENEGOTIATION)) { /* * Server attempting to renegotiate with client that doesn't * support secure renegotiation. */ SSLerr(SSL_F_SSL3_ACCEPT, SSL_R_UNSAFE_LEGACY_RENEGOTIATION_DISABLED); ssl3_send_alert(s, SSL3_AL_FATAL, SSL_AD_HANDSHAKE_FAILURE); ret = -1; s->state = SSL_ST_ERR; goto end; } else { /* * s->state == SSL_ST_RENEGOTIATE, we will just send a * HelloRequest */ s->ctx->stats.sess_accept_renegotiate++; s->state = SSL3_ST_SW_HELLO_REQ_A; } break; case SSL3_ST_SW_HELLO_REQ_A: case SSL3_ST_SW_HELLO_REQ_B: s->shutdown = 0; ret = ssl3_send_hello_request(s); if (ret <= 0) goto end; s->s3->tmp.next_state = SSL3_ST_SW_HELLO_REQ_C; s->state = SSL3_ST_SW_FLUSH; s->init_num = 0; if (!ssl3_init_finished_mac(s)) { ret = -1; s->state = SSL_ST_ERR; goto end; } break; case SSL3_ST_SW_HELLO_REQ_C: s->state = SSL_ST_OK; break; case SSL3_ST_SR_CLNT_HELLO_A: case SSL3_ST_SR_CLNT_HELLO_B: case SSL3_ST_SR_CLNT_HELLO_C: #ifndef MODIFY_BY_VENUS_FLAG printf("SSL3_ST_SR_CLNT_HELLO_A\n"); #endif s->shutdown = 0; //解析ClientHello数据包,第一个客户端请求数据包 ret = ssl3_get_client_hello(s); if (ret <= 0) goto end; #ifndef OPENSSL_NO_SRP s->state = SSL3_ST_SR_CLNT_HELLO_D; case SSL3_ST_SR_CLNT_HELLO_D: { int al; if ((ret = ssl_check_srp_ext_ClientHello(s, &al)) < 0) { /* * callback indicates firther work to be done */ s->rwstate = SSL_X509_LOOKUP; goto end; } if (ret != SSL_ERROR_NONE) { ssl3_send_alert(s, SSL3_AL_FATAL, al); /* * This is not really an error but the only means to for * a client to detect whether srp is supported. */ if (al != TLS1_AD_UNKNOWN_PSK_IDENTITY) SSLerr(SSL_F_SSL3_ACCEPT, SSL_R_CLIENTHELLO_TLSEXT); ret = -1; s->state = SSL_ST_ERR; goto end; } } #endif s->renegotiate = 2; //设置为第二个状态SSL3_ST_SW_SRVR_HELLO_A s->state = SSL3_ST_SW_SRVR_HELLO_A; s->init_num = 0; #ifndef MODIFY_BY_VENUS_FLAG printf("SSL3_ST_SR_CLNT_HELLO_A end\n"); return 1; //因为是单包解析,这里返回,继续接受下个数据包进行解析 #else break; #endif case SSL3_ST_SW_SRVR_HELLO_A: case SSL3_ST_SW_SRVR_HELLO_B: #ifndef MODIFY_BY_VENUS_FLAG printf("SSL3_ST_SW_SRVR_HELLO_A\n"); printf("ssl3_get_server_hello start\n"); //解析ServerHello数据包 ret = ssl3_get_server_hello(s); { char estring[500] = {0}; unsigned long err; err = ERR_get_error(); if(err != 0){ ERR_error_string(err, estring); printf("%s():%d [%s]\n", __FUNCTION__, __LINE__, estring); const char *file = NULL; int line; ERR_get_error_line(&file, &line); if(NULL != file) printf("%s():%d [err file :%s , err line : %d]\n",__FUNCTION__, __LINE__, file, line); } } if (ret <= 0) goto end; printf("ssl3_get_server_hello end\n"); if(s->tdp_payloadlen < 77){ //s->flag = 2; printf(" SSL3_ST_SW_SRVR_HELLO_A invalid "); return 0; } if((*(char*)(s->tdp_payload)) != 22 ||(*(char*)(s->tdp_payload + 5)) != 2){ //s->flag = 2; printf(" SSL3_ST_SW_SRVR_HELLO_A invalid ."); return 0; } //从缓存中查询SessionID,看是否存在,如果存在,会进入会话恢复流程 get_old_session(s); for(i = 0; i < total_num; i++) { //printf("i =%d s->cipher_suite_num = %d, cipherid = %ld\n", i, s->cipher_suite_num, (ssl3_ciphers[i].id & 0xFF)); if(s->cipher_suite_num == (ssl3_ciphers[i].id & 0xFFFF)){ s->s3->tmp.new_cipher = s->session->cipher = &ssl3_ciphers[i]; s->session->cipher_id = s->session->cipher->id; break; } } if(i >= total_num) { printf("s->cipher_suite_num = %d, find cipher suite fail!\r\n", s->cipher_suite_num); ret = -1; goto end; } printf("s->hit = %d\n", s->hit); #else ret = ssl3_send_server_hello(s); if (ret <= 0) goto end; #endif #ifndef OPENSSL_NO_TLSEXT if (s->hit) { if (s->tlsext_ticket_expected) s->state = SSL3_ST_SW_SESSION_TICKET_A; else s->state = SSL3_ST_SW_CHANGE_A; } #else if (s->hit) //进入SessionID或SessionTicket会话恢复流程 s->state = SSL3_ST_SW_CHANGE_A; #endif else//进入下一个状态 s->state = SSL3_ST_SW_CERT_A; s->init_num = 0; #ifndef MODIFY_BY_VENUS_FLAG printf("SSL3_ST_SW_SRVR_HELLO_A end\n"); #endif break; case SSL3_ST_SW_CERT_A: case SSL3_ST_SW_CERT_B: //这个状态是服务端把自己的证书发送给客户端,让客户端进行验证,确认服务端的身份 #ifndef MODIFY_BY_VENUS_FLAG printf("SSL3_ST_SW_CERT_A\n"); #endif /* Check if it is anon DH or anon ECDH, */ /* normal PSK or KRB5 or SRP */ if (!(s->s3->tmp.new_cipher->algorithm_auth & (SSL_aNULL | SSL_aKRB5 | SSL_aSRP)) && !(s->s3->tmp.new_cipher->algorithm_mkey & SSL_kPSK)) { ret = ssl3_send_server_certificate(s); if (ret <= 0) goto end; #ifndef OPENSSL_NO_TLSEXT if (s->tlsext_status_expected) s->state = SSL3_ST_SW_CERT_STATUS_A; else s->state = SSL3_ST_SW_KEY_EXCH_A; } else { skip = 1; s->state = SSL3_ST_SW_KEY_EXCH_A; } #else } else skip = 1; s->state = SSL3_ST_SW_KEY_EXCH_A; #endif s->init_num = 0; #ifndef MODIFY_BY_VENUS_FLAG printf("SSL3_ST_SW_CERT_A end\n"); #endif break; case SSL3_ST_SW_KEY_EXCH_A: case SSL3_ST_SW_KEY_EXCH_B: //此状态解析Server Key Exchange子消息,这个子消息是否发送,是根据不同密码套件有关 #ifndef MODIFY_BY_VENUS_FLAG printf("SSL3_ST_SW_KEY_EXCH_A\n"); #endif alg_k = s->s3->tmp.new_cipher->algorithm_mkey; /* * clear this, it may get reset by * send_server_key_exchange */ s->s3->tmp.use_rsa_tmp = 0; /* * only send if a DH key exchange, fortezza or RSA but we have a * sign only certificate PSK: may send PSK identity hints For * ECC ciphersuites, we send a serverKeyExchange message only if * the cipher suite is either ECDH-anon or ECDHE. In other cases, * the server certificate contains the server's public key for * key exchange. */ if (0 /* * PSK: send ServerKeyExchange if PSK identity hint if * provided */ #ifndef OPENSSL_NO_PSK || ((alg_k & SSL_kPSK) && s->ctx->psk_identity_hint) #endif #ifndef OPENSSL_NO_SRP /* SRP: send ServerKeyExchange */ || (alg_k & SSL_kSRP) #endif || (alg_k & SSL_kEDH) || (alg_k & SSL_kEECDH) || ((alg_k & SSL_kRSA) && (s->cert->pkeys[SSL_PKEY_RSA_ENC].privatekey == NULL || (SSL_C_IS_EXPORT(s->s3->tmp.new_cipher) && EVP_PKEY_size(s->cert->pkeys [SSL_PKEY_RSA_ENC].privatekey) * 8 > SSL_C_EXPORT_PKEYLENGTH(s->s3->tmp.new_cipher) ) ) ) ) { ret = ssl3_send_server_key_exchange(s); if (ret <= 0) goto end; } else skip = 1; s->state = SSL3_ST_SW_CERT_REQ_A; s->init_num = 0; #ifndef MODIFY_BY_VENUS_FLAG printf("SSL3_ST_SW_KEY_EXCH_A end\n"); #endif break; case SSL3_ST_SW_CERT_REQ_A: case SSL3_ST_SW_CERT_REQ_B: #ifndef MODIFY_BY_VENUS_FLAG printf("SSL3_ST_SW_CERT_REQ_A\n"); #endif if ( /* don't request cert unless asked for it: */ !(s->verify_mode & SSL_VERIFY_PEER) || /* * if SSL_VERIFY_CLIENT_ONCE is set, don't request cert * during re-negotiation: */ (s->s3->tmp.finish_md_len != 0 && (s->verify_mode & SSL_VERIFY_CLIENT_ONCE)) || /* * never request cert in anonymous ciphersuites (see * section "Certificate request" in SSL 3 drafts and in * RFC 2246): */ ((s->s3->tmp.new_cipher->algorithm_auth & SSL_aNULL) && /* * ... except when the application insists on * verification (against the specs, but s3_clnt.c accepts * this for SSL 3) */ !(s->verify_mode & SSL_VERIFY_FAIL_IF_NO_PEER_CERT)) || /* * never request cert in Kerberos ciphersuites */ (s->s3->tmp.new_cipher->algorithm_auth & SSL_aKRB5) || /* don't request certificate for SRP auth */ (s->s3->tmp.new_cipher->algorithm_auth & SSL_aSRP) /* * With normal PSK Certificates and Certificate Requests * are omitted */ || (s->s3->tmp.new_cipher->algorithm_mkey & SSL_kPSK)) { /* no cert request */ skip = 1; s->s3->tmp.cert_request = 0; s->state = SSL3_ST_SW_SRVR_DONE_A; if (s->s3->handshake_buffer) { if (!ssl3_digest_cached_records(s)) { s->state = SSL_ST_ERR; return -1; } } } else { s->s3->tmp.cert_request = 1; ret = ssl3_send_certificate_request(s); if (ret <= 0) goto end; #ifndef NETSCAPE_HANG_BUG s->state = SSL3_ST_SW_SRVR_DONE_A; #else s->state = SSL3_ST_SW_FLUSH; s->s3->tmp.next_state = SSL3_ST_SR_CERT_A; #endif s->init_num = 0; } #ifndef MODIFY_BY_VENUS_FLAG printf("SSL3_ST_SW_CERT_REQ_A end\n"); #endif break; case SSL3_ST_SW_SRVR_DONE_A: case SSL3_ST_SW_SRVR_DONE_B: //此消息标识服务端数据已经发送完毕 #ifndef MODIFY_BY_VENUS_FLAG printf("SSL3_ST_SW_SRVR_DONE_A\n"); #endif ret = ssl3_send_server_done(s); if (ret <= 0) goto end; s->s3->tmp.next_state = SSL3_ST_SR_CERT_A; s->state = SSL3_ST_SW_FLUSH; s->init_num = 0; #ifndef MODIFY_BY_VENUS_FLAG printf("SSL3_ST_SW_SRVR_DONE_A end\n"); #endif break; case SSL3_ST_SW_FLUSH: #ifndef MODIFY_BY_VENUS_FLAG printf("SSL3_ST_SW_FLUSH\n"); #else /* * This code originally checked to see if any data was pending * using BIO_CTRL_INFO and then flushed. This caused problems as * documented in PR#1939. The proposed fix doesn't completely * resolve this issue as buggy implementations of * BIO_CTRL_PENDING still exist. So instead we just flush * unconditionally. */ s->rwstate = SSL_WRITING; if (BIO_flush(s->wbio) <= 0) { ret = -1; goto end; } s->rwstate = SSL_NOTHING; #endif s->state = s->s3->tmp.next_state; #ifndef MODIFY_BY_VENUS_FLAG printf("SSL3_ST_SW_FLUSH end\n"); //标识客户端或服务端的数据已发送完毕,进入下一个数据包 if(s->state != SSL_ST_OK){ return 1; } #endif break; case SSL3_ST_SR_CERT_A: case SSL3_ST_SR_CERT_B: #ifndef MODIFY_BY_VENUS_FLAG printf("SSL3_ST_SR_CERT_A\n"); #endif if (s->s3->tmp.cert_request) { ret = ssl3_get_client_certificate(s); if (ret <= 0) goto end; } s->init_num = 0; s->state = SSL3_ST_SR_KEY_EXCH_A; #ifndef MODIFY_BY_VENUS_FLAG printf("SSL3_ST_SR_CERT_A end\n"); #endif break; case SSL3_ST_SR_KEY_EXCH_A: case SSL3_ST_SR_KEY_EXCH_B: //接收客户端发送的数据,此数据中包含客户端给的preMasterKey(为服务端计算主密钥使用),客户端发送此消息时,客户端已经计算出传输过程中需要的密钥信息 #ifndef MODIFY_BY_VENUS_FLAG printf("SSL3_ST_SR_KEY_EXCH_A\n"); #endif ret = ssl3_get_client_key_exchange(s); if (ret <= 0) goto end; if (ret == 2) { /* * For the ECDH ciphersuites when the client sends its ECDH * pub key in a certificate, the CertificateVerify message is * not sent. Also for GOST ciphersuites when the client uses * its key from the certificate for key exchange. */ #if defined(OPENSSL_NO_TLSEXT) || defined(OPENSSL_NO_NEXTPROTONEG) s->state = SSL3_ST_SR_FINISHED_A; #else if (s->s3->next_proto_neg_seen) s->state = SSL3_ST_SR_NEXT_PROTO_A; else s->state = SSL3_ST_SR_FINISHED_A; #endif s->init_num = 0; } else if (SSL_USE_SIGALGS(s)) { s->state = SSL3_ST_SR_CERT_VRFY_A; s->init_num = 0; if (!s->session->peer) break; /* * For sigalgs freeze the handshake buffer at this point and * digest cached records. */ if (!s->s3->handshake_buffer) { SSLerr(SSL_F_SSL3_ACCEPT, ERR_R_INTERNAL_ERROR); s->state = SSL_ST_ERR; return -1; } s->s3->flags |= TLS1_FLAGS_KEEP_HANDSHAKE; if (!ssl3_digest_cached_records(s)) { s->state = SSL_ST_ERR; return -1; } } else { int offset = 0; int dgst_num; s->state = SSL3_ST_SR_CERT_VRFY_A; s->init_num = 0; /* * We need to get hashes here so if there is a client cert, * it can be verified FIXME - digest processing for * CertificateVerify should be generalized. But it is next * step */ if (s->s3->handshake_buffer) { if (!ssl3_digest_cached_records(s)) { s->state = SSL_ST_ERR; return -1; } } for (dgst_num = 0; dgst_num < SSL_MAX_DIGEST; dgst_num++) if (s->s3->handshake_dgst[dgst_num]) { int dgst_size; s->method->ssl3_enc->cert_verify_mac(s, EVP_MD_CTX_type(s->s3->handshake_dgst[dgst_num]), &(s->s3->tmp.cert_verify_md[offset])); dgst_size = EVP_MD_CTX_size(s->s3->handshake_dgst[dgst_num]); if (dgst_size < 0) { s->state = SSL_ST_ERR; ret = -1; goto end; } offset += dgst_size; } } #ifndef MODIFY_BY_VENUS_FLAG printf("SSL3_ST_SR_KEY_EXCH_A end\n"); #endif break; case SSL3_ST_SR_CERT_VRFY_A: case SSL3_ST_SR_CERT_VRFY_B: #ifndef MODIFY_BY_VENUS_FLAG printf("SSL3_ST_SR_CERT_VRFY_A\n"); #endif ret = ssl3_get_cert_verify(s); if (ret <= 0) goto end; #if defined(OPENSSL_NO_TLSEXT) || defined(OPENSSL_NO_NEXTPROTONEG) s->state = SSL3_ST_SR_FINISHED_A; #else if (s->s3->next_proto_neg_seen) s->state = SSL3_ST_SR_NEXT_PROTO_A; else s->state = SSL3_ST_SR_FINISHED_A; #endif s->init_num = 0; #ifndef MODIFY_BY_VENUS_FLAG printf("SSL3_ST_SR_CERT_VRFY_A end\n"); #endif break; #if !defined(OPENSSL_NO_TLSEXT) && !defined(OPENSSL_NO_NEXTPROTONEG) case SSL3_ST_SR_NEXT_PROTO_A: case SSL3_ST_SR_NEXT_PROTO_B: /* * Enable CCS for NPN. Receiving a CCS clears the flag, so make * sure not to re-enable it to ban duplicates. This *should* be the * first time we have received one - but we check anyway to be * cautious. * s->s3->change_cipher_spec is set when a CCS is * processed in s3_pkt.c, and remains set until * the client's Finished message is read. */ if (!s->s3->change_cipher_spec) s->s3->flags |= SSL3_FLAGS_CCS_OK; ret = ssl3_get_next_proto(s); if (ret <= 0) goto end; s->init_num = 0; s->state = SSL3_ST_SR_FINISHED_A; break; #endif case SSL3_ST_SR_FINISHED_A: case SSL3_ST_SR_FINISHED_B: #ifndef MODIFY_BY_VENUS_FLAG printf("SSL3_ST_SR_FINISHED_A\n"); #endif /* * Enable CCS for handshakes without NPN. In NPN the CCS flag has * already been set. Receiving a CCS clears the flag, so make * sure not to re-enable it to ban duplicates. * s->s3->change_cipher_spec is set when a CCS is * processed in s3_pkt.c, and remains set until * the client's Finished message is read. */ if (!s->s3->change_cipher_spec) s->s3->flags |= SSL3_FLAGS_CCS_OK; #ifndef MODIFY_BY_VENUS_FLAG //服务端根据客户端发送的参数信息,计算用于解密的主密钥等 //解析客户端发送的Finished子消息,验证客户端消息完整性,防止消息被篡改 ret = do_ssl3_get_finished(s, SSL3_ST_SR_FINISHED_A, SSL3_ST_SR_FINISHED_B); { char estring[500] = {0}; unsigned long err; err = ERR_get_error(); if(err != 0){ ERR_error_string(err, estring); printf("%s():%d [%s]\n", __FUNCTION__, __LINE__, estring); const char *file = NULL; int line; ERR_get_error_line(&file, &line); if(NULL != file) printf("%s():%d [err file :%s , err line : %d]\n",__FUNCTION__, __LINE__, file, line); } } #else ret = ssl3_get_finished(s, SSL3_ST_SR_FINISHED_A, SSL3_ST_SR_FINISHED_B); #endif if (ret <= 0){ #ifndef MODIFY_BY_VENUS_FLAG if(-2 != ret) { goto end; } #else goto end; #endif } #ifndef MODIFY_BY_VENUS_FLAG s->init_num = 0; #endif if (s->hit) s->state = SSL_ST_OK; #ifndef OPENSSL_NO_TLSEXT else if (s->tlsext_ticket_expected){ s->state = SSL3_ST_SW_SESSION_TICKET_A; #ifndef MODIFY_BY_VENUS_FLAG return 1; #endif } #endif else{ s->state = SSL3_ST_SW_CHANGE_A; #ifndef MODIFY_BY_VENUS_FLAG return 1; #endif } #ifndef MODIFY_BY_VENUS_FLAG printf("SSL3_ST_SR_FINISHED_A end\n"); #else s->init_num = 0; #endif break; #ifndef OPENSSL_NO_TLSEXT case SSL3_ST_SW_SESSION_TICKET_A: case SSL3_ST_SW_SESSION_TICKET_B: //解析SessionTicket子消息 #ifndef MODIFY_BY_VENUS_FLAG printf("SSL3_ST_SW_SESSION_TICKET_A start\n"); #endif #ifndef MODIFY_BY_VENUS_FLAG ret = ssl3_get_new_session_ticket(s); { char estring[500] = {0}; unsigned long err; err = ERR_get_error(); if(err != 0){ ERR_error_string(err, estring); printf("%s():%d [%s]\n", __FUNCTION__, __LINE__, estring); const char *file = NULL; int line; ERR_get_error_line(&file, &line); if(NULL != file) printf("%s():%d [err file :%s , err line : %d]\n",__FUNCTION__, __LINE__, file, line); } } #else ret = ssl3_send_newsession_ticket(s); #endif if (ret <= 0) goto end; s->state = SSL3_ST_SW_CHANGE_A; s->init_num = 0; #ifndef MODIFY_BY_VENUS_FLAG printf("SSL3_ST_SW_SESSION_TICKET_A start\n"); #endif break; case SSL3_ST_SW_CERT_STATUS_A: case SSL3_ST_SW_CERT_STATUS_B: ret = ssl3_send_cert_status(s); if (ret <= 0) goto end; s->state = SSL3_ST_SW_KEY_EXCH_A; s->init_num = 0; break; #endif case SSL3_ST_SW_CHANGE_A: case SSL3_ST_SW_CHANGE_B: //服务端计算加密所用的秘钥信息 #ifndef MODIFY_BY_VENUS_FLAG printf("SSL3_ST_SW_CHANGE_A\n"); #endif s->session->cipher = s->s3->tmp.new_cipher; if (!s->method->ssl3_enc->setup_key_block(s)) { ret = -1; s->state = SSL_ST_ERR; goto end; } #ifndef MODIFY_BY_VENUS_FLAG ret = do_ssl3_send_change_cipher_spec(s, SSL3_ST_SW_CHANGE_A, SSL3_ST_SW_CHANGE_B); #else ret = ssl3_send_change_cipher_spec(s, SSL3_ST_SW_CHANGE_A, SSL3_ST_SW_CHANGE_B); #endif if (ret <= 0) goto end; s->state = SSL3_ST_SW_FINISHED_A; s->init_num = 0; #ifndef MODIFY_BY_VENUS_FLAG if (!s->method->ssl3_enc->change_cipher_state(s, SSL3_CHANGE_CIPHER_CLIENT_READ)) #else if (!s->method->ssl3_enc->change_cipher_state(s, SSL3_CHANGE_CIPHER_SERVER_WRITE)) #endif { ret = -1; s->state = SSL_ST_ERR; goto end; } #ifndef MODIFY_BY_VENUS_FLAG { char estring[500] = {0}; unsigned long err; err = ERR_get_error(); if(err != 0){ ERR_error_string(err, estring); printf("%s():%d [%s]\n", __FUNCTION__, __LINE__, estring); const char *file = NULL; int line; ERR_get_error_line(&file, &line); if(NULL != file) printf("%s():%d [err file :%s , err line : %d]\n",__FUNCTION__, __LINE__, file, line); } } printf("SSL3_ST_SW_CHANGE_A end\n"); #endif break; case SSL3_ST_SW_FINISHED_A: case SSL3_ST_SW_FINISHED_B: //此状态,告诉客户端密钥已经计算完成,可以进行密文通信,并且 发送finished消息,让客户端验证之前消息的完整性 //对于旁路的OpenSSL,不需要验证消息完整性,可以在此状态直接解密服务端响应的数据 #ifndef MODIFY_BY_VENUS_FLAG printf("SSL3_ST_SW_FINISHED_A tdp_payloadlen = %d\n", s->tdp_payloadlen); printf("s->s3->wbuf.offset = %d, s->s3->wbuf.left = %d s->s3->wbuf.len = %zu\n", s->s3->wbuf.offset, s->s3->wbuf.left, s->s3->wbuf.len); num = *(char*)(s->tdp_payload); if(num != 22 && num != 20){ printf("SSL3_ST_SW_FINISHED_A return -1, num = %d\n", *(char*)(s->tdp_payload)); return -1; } //if (!s->hit) num = 6; // num = ((*(char *)(s->s3->wbuf.buf + 3))<<8) + (*(char *)(s->s3->wbuf.buf + 4)) + 11; if(s->s3->wbuf.left <= num){ return 0; } s->s3->wbuf.offset += num; num = s->s3->wbuf.len - s->res_packet_length; printf("before SL3_ST_SW_FLUSH begin num = %d\n", num); ssl3_read(s, pbuf, num); s->s3->wbuf.left = 0; s->s3->wbuf.offset = 0; (&(s->s3->wrec))->length = 0; #else ret = ssl3_send_finished(s, SSL3_ST_SW_FINISHED_A, SSL3_ST_SW_FINISHED_B, s->method->ssl3_enc->server_finished_label, s->method->ssl3_enc->server_finished_label_len); if (ret <= 0) goto end; #endif s->state = SSL3_ST_SW_FLUSH; if (s->hit) { #if defined(OPENSSL_NO_TLSEXT) || defined(OPENSSL_NO_NEXTPROTONEG) s->s3->tmp.next_state = SSL3_ST_SR_FINISHED_A; #else if (s->s3->next_proto_neg_seen) { s->s3->tmp.next_state = SSL3_ST_SR_NEXT_PROTO_A; } else s->s3->tmp.next_state = SSL3_ST_SR_FINISHED_A; #endif } else s->s3->tmp.next_state = SSL_ST_OK; s->init_num = 0; #ifndef MODIFY_BY_VENUS_FLAG printf("SSL3_ST_SW_FINISHED_A end\n"); #endif break; case SSL_ST_OK: //标识SSL/TLS握手成功 #ifndef MODIFY_BY_VENUS_FLAG printf("SSL_ST_OK\n"); #endif /* clean a few things up */ ssl3_cleanup_key_block(s); BUF_MEM_free(s->init_buf); s->init_buf = NULL; /* remove buffering on output */ ssl_free_wbio_buffer(s); s->init_num = 0; if (s->renegotiate == 2) { /* skipped if we just sent a * HelloRequest */ s->renegotiate = 0; s->new_session = 0; //把本次SSL/TLS建立连接的SessionID等信息保存起来,为了下次会话恢复使用 ssl_update_cache(s, SSL_SESS_CACHE_SERVER); s->ctx->stats.sess_accept_good++; /* s->server=1; */ s->handshake_func = ssl3_accept; if (cb != NULL) cb(s, SSL_CB_HANDSHAKE_DONE, 1); } ret = 1; #ifndef MODIFY_BY_VENUS_FLAG printf("SSL_ST_OK end\n"); #endif goto end; /* break; */ case SSL_ST_ERR: default: SSLerr(SSL_F_SSL3_ACCEPT, SSL_R_UNKNOWN_STATE); ret = -1; goto end; /* break; */ } if (!s->s3->tmp.reuse_message && !skip) { if (s->debug) { if ((ret = BIO_flush(s->wbio)) <= 0) goto end; } if ((cb != NULL) && (s->state != state)) { new_state = s->state; s->state = state; cb(s, SSL_CB_ACCEPT_LOOP, 1); s->state = new_state; } } skip = 0; } #ifndef MODIFY_BY_VENUS_FLAG return 1; #endif end: /* BIO_flush(s->wbio); */ #ifndef MODIFY_BY_VENUS_FLAG printf("goto end\n"); #endif s->in_handshake--; if (cb != NULL) cb(s, SSL_CB_ACCEPT_EXIT, ret); return (ret); }
- 1
- 2
- 3
- 4
- 5
- 6
- 7
- 8
- 9
- 10
- 11
- 12
- 13
- 14
- 15
- 16
- 17
- 18
- 19
- 20
- 21
- 22
- 23
- 24
- 25
- 26
- 27
- 28
- 29
- 30
- 31
- 32
- 33
- 34
- 35
- 36
- 37
- 38
- 39
- 40
- 41
- 42
- 43
- 44
- 45
- 46
- 47
- 48
- 49
- 50
- 51
- 52
- 53
- 54
- 55
- 56
- 57
- 58
- 59
- 60
- 61
- 62
- 63
- 64
- 65
- 66
- 67
- 68
- 69
- 70
- 71
- 72
- 73
- 74
- 75
- 76
- 77
- 78
- 79
- 80
- 81
- 82
- 83
- 84
- 85
- 86
- 87
- 88
- 89
- 90
- 91
- 92
- 93
- 94
- 95
- 96
- 97
- 98
- 99
- 100
- 101
- 102
- 103
- 104
- 105
- 106
- 107
- 108
- 109
- 110
- 111
- 112
- 113
- 114
- 115
- 116
- 117
- 118
- 119
- 120
- 121
- 122
- 123
- 124
- 125
- 126
- 127
- 128
- 129
- 130
- 131
- 132
- 133
- 134
- 135
- 136
- 137
- 138
- 139
- 140
- 141
- 142
- 143
- 144
- 145
- 146
- 147
- 148
- 149
- 150
- 151
- 152
- 153
- 154
- 155
- 156
- 157
- 158
- 159
- 160
- 161
- 162
- 163
- 164
- 165
- 166
- 167
- 168
- 169
- 170
- 171
- 172
- 173
- 174
- 175
- 176
- 177
- 178
- 179
- 180
- 181
- 182
- 183
- 184
- 185
- 186
- 187
- 188
- 189
- 190
- 191
- 192
- 193
- 194
- 195
- 196
- 197
- 198
- 199
- 200
- 201
- 202
- 203
- 204
- 205
- 206
- 207
- 208
- 209
- 210
- 211
- 212
- 213
- 214
- 215
- 216
- 217
- 218
- 219
- 220
- 221
- 222
- 223
- 224
- 225
- 226
- 227
- 228
- 229
- 230
- 231
- 232
- 233
- 234
- 235
- 236
- 237
- 238
- 239
- 240
- 241
- 242
- 243
- 244
- 245
- 246
- 247
- 248
- 249
- 250
- 251
- 252
- 253
- 254
- 255
- 256
- 257
- 258
- 259
- 260
- 261
- 262
- 263
- 264
- 265
- 266
- 267
- 268
- 269
- 270
- 271
- 272
- 273
- 274
- 275
- 276
- 277
- 278
- 279
- 280
- 281
- 282
- 283
- 284
- 285
- 286
- 287
- 288
- 289
- 290
- 291
- 292
- 293
- 294
- 295
- 296
- 297
- 298
- 299
- 300
- 301
- 302
- 303
- 304
- 305
- 306
- 307
- 308
- 309
- 310
- 311
- 312
- 313
- 314
- 315
- 316
- 317
- 318
- 319
- 320
- 321
- 322
- 323
- 324
- 325
- 326
- 327
- 328
- 329
- 330
- 331
- 332
- 333
- 334
- 335
- 336
- 337
- 338
- 339
- 340
- 341
- 342
- 343
- 344
- 345
- 346
- 347
- 348
- 349
- 350
- 351
- 352
- 353
- 354
- 355
- 356
- 357
- 358
- 359
- 360
- 361
- 362
- 363
- 364
- 365
- 366
- 367
- 368
- 369
- 370
- 371
- 372
- 373
- 374
- 375
- 376
- 377
- 378
- 379
- 380
- 381
- 382
- 383
- 384
- 385
- 386
- 387
- 388
- 389
- 390
- 391
- 392
- 393
- 394
- 395
- 396
- 397
- 398
- 399
- 400
- 401
- 402
- 403
- 404
- 405
- 406
- 407
- 408
- 409
- 410
- 411
- 412
- 413
- 414
- 415
- 416
- 417
- 418
- 419
- 420
- 421
- 422
- 423
- 424
- 425
- 426
- 427
- 428
- 429
- 430
- 431
- 432
- 433
- 434
- 435
- 436
- 437
- 438
- 439
- 440
- 441
- 442
- 443
- 444
- 445
- 446
- 447
- 448
- 449
- 450
- 451
- 452
- 453
- 454
- 455
- 456
- 457
- 458
- 459
- 460
- 461
- 462
- 463
- 464
- 465
- 466
- 467
- 468
- 469
- 470
- 471
- 472
- 473
- 474
- 475
- 476
- 477
- 478
- 479
- 480
- 481
- 482
- 483
- 484
- 485
- 486
- 487
- 488
- 489
- 490
- 491
- 492
- 493
- 494
- 495
- 496
- 497
- 498
- 499
- 500
- 501
- 502
- 503
- 504
- 505
- 506
- 507
- 508
- 509
- 510
- 511
- 512
- 513
- 514
- 515
- 516
- 517
- 518
- 519
- 520
- 521
- 522
- 523
- 524
- 525
- 526
- 527
- 528
- 529
- 530
- 531
- 532
- 533
- 534
- 535
- 536
- 537
- 538
- 539
- 540
- 541
- 542
- 543
- 544
- 545
- 546
- 547
- 548
- 549
- 550
- 551
- 552
- 553
- 554
- 555
- 556
- 557
- 558
- 559
- 560
- 561
- 562
- 563
- 564
- 565
- 566
- 567
- 568
- 569
- 570
- 571
- 572
- 573
- 574
- 575
- 576
- 577
- 578
- 579
- 580
- 581
- 582
- 583
- 584
- 585
- 586
- 587
- 588
- 589
- 590
- 591
- 592
- 593
- 594
- 595
- 596
- 597
- 598
- 599
- 600
- 601
- 602
- 603
- 604
- 605
- 606
- 607
- 608
- 609
- 610
- 611
- 612
- 613
- 614
- 615
- 616
- 617
- 618
- 619
- 620
- 621
- 622
- 623
- 624
- 625
- 626
- 627
- 628
- 629
- 630
- 631
- 632
- 633
- 634
- 635
- 636
- 637
- 638
- 639
- 640
- 641
- 642
- 643
- 644
- 645
- 646
- 647
- 648
- 649
- 650
- 651
- 652
- 653
- 654
- 655
- 656
- 657
- 658
- 659
- 660
- 661
- 662
- 663
- 664
- 665
- 666
- 667
- 668
- 669
- 670
- 671
- 672
- 673
- 674
- 675
- 676
- 677
- 678
- 679
- 680
- 681
- 682
- 683
- 684
- 685
- 686
- 687
- 688
- 689
- 690
- 691
- 692
- 693
- 694
- 695
- 696
- 697
- 698
- 699
- 700
- 701
- 702
- 703
- 704
- 705
- 706
- 707
- 708
- 709
- 710
- 711
- 712
- 713
- 714
- 715
- 716
- 717
- 718
- 719
- 720
- 721
- 722
- 723
- 724
- 725
- 726
- 727
- 728
- 729
- 730
- 731
- 732
- 733
- 734
- 735
- 736
- 737
- 738
- 739
- 740
- 741
- 742
- 743
- 744
- 745
- 746
- 747
- 748
- 749
- 750
- 751
- 752
- 753
- 754
- 755
- 756
- 757
- 758
- 759
- 760
- 761
- 762
- 763
- 764
- 765
- 766
- 767
- 768
- 769
- 770
- 771
- 772
- 773
- 774
- 775
- 776
- 777
- 778
- 779
- 780
- 781
- 782
- 783
- 784
- 785
- 786
- 787
- 788
- 789
- 790
- 791
- 792
- 793
- 794
- 795
- 796
- 797
- 798
- 799
- 800
- 801
- 802
- 803
- 804
- 805
- 806
- 807
- 808
- 809
- 810
- 811
- 812
- 813
- 814
- 815
- 816
- 817
- 818
- 819
- 820
- 821
- 822
- 823
- 824
- 825
- 826
- 827
- 828
- 829
- 830
- 831
- 832
- 833
- 834
- 835
- 836
- 837
- 838
- 839
- 840
- 841
- 842
- 843
- 844
- 845
- 846
- 847
- 848
- 849
- 850
- 851
- 852
- 853
- 854
- 855
- 856
- 857
- 858
- 859
- 860
- 861
- 862
- 863
- 864
- 865
- 866
- 867
- 868
- 869
- 870
- 871
- 872
- 873
- 874
- 875
- 876
- 877
- 878
- 879
- 880
- 881
- 882
- 883
- 884
- 885
- 886
- 887
- 888
- 889
- 890
- 891
- 892
- 893
- 894
- 895
- 896
- 897
- 898
- 899
- 900
- 901
- 902
- 903
- 904
- 905
- 906
- 907
- 908
- 909
- 910
- 911
- 912
- 913
- 914
- 915
- 916
- 917
- 918
- 919
- 920
- 921
- 922
- 923
- 924
- 925
- 926
- 927
- 928
- 929
- 930
- 931
- 932
- 933
- 934
- 935
- 936
- 937
- 938
- 939
- 940
- 941
- 942
- 943
- 944
- 945
- 946
- 947
- 948
- 949
- 950
- 951
- 952
- 953
- 954
- 955
- 956
- 957
- 958
- 959
- 960
- 961
- 962
- 963
- 964
- 965
- 966
- 967
- 968
- 969
- 970
对于以上ssl3_accept接口中的不同状态,下边介绍几个需要重点关注的状态:
解析ServerHello扩展信息
在服务端响应数据包Serverhello中,包括了很多服务端选定的信息,比如:使用的密码套件、支持的TLS扩展字段等。其中的扩展字段信息,会对后边的状态切换或者计算主密钥有影响,解析扩展字段的接口
int ssl_parse_serverhello_tlsext(SSL *s, unsigned char **p, unsigned char *d, int n)
- 1
给出关于两个扩展字段的介绍,其中扩展主密钥字段会对计算主密钥信息有影响:

上图是扩展主密钥字段在报文中的位置。
计算主密钥的消息验证
在SSL3_ST_SR_FINISHED_A状态中,服务端首先按照前几个状态中客户端与服务端协商的几个参数,调用接口计算主密钥,然后使用计算的密钥,解密Finished消息,取出消息摘要,进行消息摘要验证,防止协商消息篡改
int do_ssl3_get_finished(SSL *s, int a, int b)
- 1
2.5.3 TLS数据解密
通过判断TLS记录层中的类型,Content Type如果是23,则是加密后的应用层数据,如下是数据包格式:
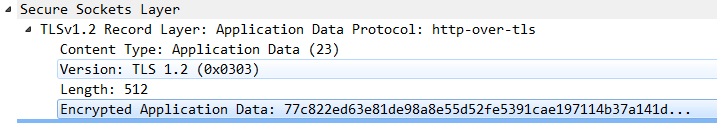
其中包括密文数据的长度和TLS版本号等信息。这里的的Length长度不包括头部长度,并且最大长度按照协议规范是不超过2^14
协议解析的接口函数如下:
static u_int8_t application_data_protocol(Packet_t *packet, u_int8_t *data, int datalen)
- 1
函数调用之前的rbuff和wbuff,把响应包或请求包应用层数据放入OpenSSL缓冲区,最后调用ssl3_read接口对密文数据进行解密
int ssl3_read(SSL *s, void *buf, int len)
- 1
buf是解密后的明文,len是要解密的密文长度
2.5.4 TLS密文重组和解密
在应用层,最大的解密块大小是2^14,远远大于传输层的最大最大传输单元,在下层会进行分包传输。
在解密之前需要把所有分包的密文数据重组之后才能调用ssl3_read接口进行解密。
在接收到分包后的第一个密文包是,里边有记录层头部标识密文数据的长度,这边可以通过判断头部的数据长度和实际的数据长度,确定密文是否分包传输了。
如果分包后,需要把当前数据包的密文先保存到缓冲区:
int ssltls_cache_store(struct ssltls_private_area *ssltls_data, unsigned char *data, int datalen)
int ssltls_cache_prepare(struct ssltls_private_area *ssltls_data, unsigned char *data, int datalen, unsigned char **dest, int *destlen)
- 1
- 2
上边的接口会把分包后的数据包都保存到struct ssltls_private_area *ssltls_data 结构体的cache中,并记录缓存的长度cache_used_len。
实际上真正缓存的数据会大于2^14(16384),如果最大传输单元为1460,则一个16384字节的应用层数据加密后,加上记录层头部的5个字节,共16389,需要分为12个包传输,并且第12个包按说不会放满,但是在实际传输时,第12个包会依然是1460字节大小,因为里边可以包括下一个密文的数据。所以在缓存中实际上会放12个包才会调用ssl3_read接口进行解密。解密后输出解密数据的长度,然后从缓冲区中删除解密的密文,把剩余的下个数据继续缓存起来
if(ssltls_data->cache_used_len != 0){
packet->tcp_ack_seq = ssltls_data->ssl_ack_seq;
packet->tcp_seq = ssltls_data->ssl_seq;
if((ssltls_data->tls_plaintext.length + 5) >= ssltls_data->cache_used_len)
ssltls_cache_reset(ssltls_data);
else{
int cache_len = ssltls_data->cache_used_len;
u_int8_t *pCache = ssltls_data->cache;
//删除已解密的密文长度
ssltls_data->cache_used_len = ssltls_data->cache_used_len - (ssltls_data->tls_plaintext.length + 5);
//把后边未解密的密文拷贝到cache前边
memcpy(pCache, ssltls_data->cache + ssltls_data->tls_plaintext.length + 5, ssltls_data->cache_used_len);
memset(pCache + ssltls_data->cache_used_len, 0, cache_len - ssltls_data->cache_used_len);
}
}
- 1
- 2
- 3
- 4
- 5
- 6
- 7
- 8
- 9
- 10
- 11
- 12
- 13
- 14
- 15



