- 1爆火!!!中文版 Llama3 开源了!!_ollama llama3 强制用中文回答
- 2520表白神器,小贺只能帮你到这了......
- 32024年,计算机相关专业还值得选择吗?_计算机专业现在饱和了吗
- 4Android 应用程序集成Google 登录及二次封装_com.google.android.gms.auth.api
- 5error: RPC failed; curl 18 transfer closed with outstanding read data remaining fatal: the remote en_linux搭建http server 下载文件出现curl: (18) transfer close
- 6Android Studio 安卓模拟器无法连接网络_androidstudio模拟器没网络
- 7Elasticsearch介绍2
- 8Kubernetes1.23搭建Elasticsearch7集群(集群加密)_kubernetes部署单机elasticsearch7.16.2
- 9【Diffusers库】第五篇 加载pipeline、model、schedulers_diffusers pipline没有本地模型
- 10神仙级AI大模型入门教程(非常详细),从零基础入门到精通,从看这篇开始!_大模型教程
Spring OAuth2 授权服务器配置详解,百度java面试难度_registeredclientrepository
赞
踩
定义一个客户端可以通过下面的Builder方法实现:
RegisteredClient registeredClient = RegisteredClient.withId(UUID.randomUUID().toString())
// 唯一的客户端ID和密码
.clientId(“felord-client”)
.clientSecret(“secret”)
// 名称 可不定义
.clientName(“felord”)
// 授权方法
.clientAuthenticationMethod(ClientAuthenticationMethod.CLIENT_SECRET_BASIC)
// 授权类型
.authorizationGrantType(AuthorizationGrantType.AUTHORIZATION_CODE)
.authorizationGrantType(AuthorizationGrantType.REFRESH_TOKEN)
.authorizationGrantType(AuthorizationGrantType.CLIENT_CREDENTIALS)
// 回调地址名单,不在此列将被拒绝 而且只能使用IP或者域名 不能使用 localhost
.redirectUri(“http://127.0.0.1:8080/login/oauth2/code/felord-oidc”)
.redirectUri(“http://127.0.0.1:8080/authorized”)
.redirectUri(“http://127.0.0.1:8080/foo/bar”)
.redirectUri(“https://baidu.com”)
// OIDC支持
.scope(OidcScopes.OPENID)
// 其它Scope
.scope(“message.read”)
.scope(“message.write”)
// JWT的配置项 包括TTL 是否复用refreshToken等等
.tokenSettings(TokenSettings.builder().build())
// 配置客户端相关的配置项,包括验证密钥或者 是否需要授权页面
.clientSettings(ClientSettings.builder().requireAuthorizationConsent(true).build())
.build();
持久化到数据库的RegisteredClient用JSON表示为:
{
“id”: “658cd010-4d8c-4824-a8c7-a86b642299af”,
“client_id”: “felord-client”,
“client_id_issued_at”: “2021-11-11 18:01:09”,
“client_secret”: “{bcrypt}$2a 10 10 10XKZ8iUckDcdQWnqw682zV.DVyGuov8Sywx1KyAn4tySsw.Jtltg0.”,
“client_secret_expires_at”: null,
“client_name”: “felord”,
“client_authentication_methods”: “client_secret_basic”,
“authorization_grant_types”: “refresh_token,client_credentials,authorization_code”,
“redirect_uris”: “http://127.0.0.1:8080/foo/bar,http://127.0.0.1:8080/authorized,http://127.0.0.1:8080/login/oauth2/code/felord-oidc,https://baidu.com”,
“scopes”: “openid,message.read,message.write”,
“client_settings”: “{”@class":“java.util.Collections$UnmodifiableMap”,“settings.client.require-proof-key”:false,“settings.client.require-authorization-consent”:true}",
“token_settings”: “{”@class":“java.util.Collections$UnmodifiableMap”,“settings.token.reuse-refresh-tokens”:true,“settings.token.id-token-signature-algorithm”:[“org.springframework.security.oauth2.jose.jws.SignatureAlgorithm”,“RS256”],“settings.token.access-token-time-to-live”:[“java.time.Duration”,300.000000000],“settings.token.refresh-token-time-to-live”:[“java.time.Duration”,3600.000000000]}"
}
❝
注意上面的配置和你OAuth2.0客户端应用的配置息息相关。
既然持久化了,那自然需要操作该表的JDBC服务接口了,这个接口为RegisteredClientRepository。我们需要声明一个实现为Spring Bean,这里选择基于JDBC的实现:
@Bean
public RegisteredClientRepository registeredClientRepository(JdbcTemplate jdbcTemplate) {
return new JdbcRegisteredClientRepository(jdbcTemplate);
}
别忘记调用save(RegisteredClient)方法把需要注册的客户端信息持久化。
❝
该实现依赖
spring-boot-starter-jdbc类库,你也可以闲得慌使用Mybatis进行实现。
OAuth2授权信息持久化
记录授权的资源拥有者(Resource Owner)对某个客户端的某次授权记录。对应的Java类为OAuth2Authorization。下面是定义脚本:
CREATE TABLE oauth2_authorization
(
id varchar(100) NOT NULL,
registered_client_id varchar(100) NOT NULL,
principal_name varchar(200) NOT NULL,
authorization_grant_type varchar(100) NOT NULL,
attributes varchar(4000) NULL,
state varchar(500) NULL,
authorization_code_value blob NULL,
authorization_code_issued_at timestamp NULL,
authorization_code_expires_at timestamp NULL,
authorization_code_metadata varchar(2000) NULL,
access_token_value blob NULL,
access_token_issued_at timestamp NULL,
access_token_expires_at timestamp NULL,
access_token_metadata varchar(2000) NULL,
access_token_type varchar(100) NULL,
access_token_scopes varchar(1000) NULL,
oidc_id_token_value blob NULL,
oidc_id_token_issued_at timestamp NULL,
oidc_id_token_expires_at timestamp NULL,
oidc_id_token_metadata varchar(2000) NULL,
refresh_token_value blob NULL,
refresh_token_issued_at timestamp NULL,
refresh_token_expires_at timestamp NULL,
refresh_token_metadata varchar(2000) NULL,
PRIMARY KEY (id)
);
❝
这里的机制目前还没有研究,先挖个坑。
同样它也需要一个持久化服务接口OAuth2AuthorizationService并注入Spring IoC:
/**
* 管理OAuth2授权信息服务
* @param jdbcTemplate the jdbc template
* @param registeredClientRepository the registered client repository
* @return the o auth 2 authorization service
*/
@Bean
public OAuth2AuthorizationService authorizationService(JdbcTemplate jdbcTemplate,
RegisteredClientRepository registeredClientRepository) {
return new JdbcOAuth2AuthorizationService(jdbcTemplate,
registeredClientRepository);
}
持久化到数据库的OAuth2Authorization用JSON表示为:
{
“id”: “aa2f6e7d-d9b9-4360-91ef-118cbb6d4b09”,
“registered_client_id”: “658cd010-4d8c-4824-a8c7-a86b642299af”,
“principal_name”: “felord”,
“authorization_grant_type”: “authorization_code”,
“attributes”: “{”@class":“java.util.CollectionsKaTeX parse error: Expected group as argument to '\"' at position 317: …rization_code\"}̲,\"responseType…UnmodifiableSet”,[“message.read”,“message.write”]],“state”:“9gTcVNXgV8Pn_Ron3bkFb6M92AYCodeWKoEd6xxaiUg=”,“additionalParameters”:{“@class”:“java.util.CollectionsKaTeX parse error: Expected group as argument to '\"' at position 18: …modifiableMap\"}̲,\"authorizatio…UnmodifiableMap”}},“java.security.Principal”:{“@class”:“org.springframework.security.authentication.UsernamePasswordAuthenticationToken”,“authorities”:[“java.util.CollectionsKaTeX parse error: Expected group as argument to '\"' at position 143: …":\"ROLE_USER\"}̲]],\"details\":…UnmodifiableSet”,[{“@class”:“org.springframework.security.core.authority.SimpleGrantedAuthority”,“authority”:“ROLE_USER”}]],“accountNonExpired”:true,“accountNonLocked”:true,“credentialsNonExpired”:true,“enabled”:true},“credentials”:null},“org.springframework.security.oauth2.server.authorization.OAuth2Authorization.AUTHORIZED_SCOPE”:[“java.util.Collections$UnmodifiableSet”,[“message.read”,“message.write”]]}",
“state”: null,
“authorization_code_value”: “EZFxDcsKoaGtyqRTS0oNMg85EcVcyLdVssuD3SV-o0FvNXsSTRjTmCdu0ZPZnVIQ7K4TTSzrvLwBqoRXOigo_dWVNeqE44LjHHL_KtujM_Mxz8hLZgGhtfipvTdpWWR1”,
“authorization_code_issued_at”: “2021-11-11 18:44:45”,
“authorization_code_expires_at”: “2021-11-11 18:49:45”,
“authorization_code_metadata”: “{”@class":“java.util.Collections$UnmodifiableMap”,“metadata.token.invalidated”:true}",
“access_token_value”: “eyJ4NXQjUzI1NiI6IlZGR1F4Q21nSEloX2dhRi13UGIxeEM5b0tBMXc1bGEwRUZtcXFQTXJxbXciLCJraWQiOiJmZWxvcmRjbiIsImFsZyI6IlJTMjU2In0.eyJzdWIiOiJmZWxvcmQiLCJhdWQiOiJmZWxvcmQtY2xpZW50IiwibmJmIjoxNjM2NjI3NDg0LCJzY29wZSI6WyJtZXNzYWdlLnJlYWQiLCJtZXNzYWdlLndyaXRlIl0sImlzcyI6Imh0dHA6XC9cL2xvY2FsaG9zdDo5MDAwIiwiZXhwIjoxNjM2NjI3Nzg0LCJpYXQiOjE2MzY2Mjc0ODR9.CFzye9oIh8-ZMpyp9XoIXIQLnj2Sn17yZ9bgn7NYAbrp2hRq-Io_Se2SJpSEMa_Ce44aOGmcLTmIOILYUxlU08QCtHgr4UfCZttzroQhEn3Qui7fixBMprPYqxmu2KL5G_l3q5EWyh4G0ilHpByCBDeBGAl7FpaxSDlelnBfNGs9q6nJCs7aC40U_YPBRLoCBLVK1Y8t8kQvNu8NqCkS5D5DZAogpmlVg7jSIPz1UXVIh7iDTTQ1wJl6rZ1E87E0UroX4eSuYfMQ351y65IUlB14hvKhu03yDLTiVKtujOo3m0DAkJTbk3ZkFZEmDf4N3Yn-ktU7cyswQWa1bKf3og”,
“access_token_issued_at”: “2021-11-11 18:44:45”,
“access_token_expires_at”: “2021-11-11 18:49:45”,
“access_token_metadata”: “{”@class":“java.util.CollectionsKaTeX parse error: Expected '}', got 'EOF' at end of input: …til.CollectionsUnmodifiableMap”,“sub”:“felord”,“aud”:[“java.util.Collections S i n g l e t o n L i s t , ¨ [ f ¨ e l o r d − c l i e n t ] ¨ ] , n ¨ b f : ¨ [ j ¨ a v a . t i m e . I n s t a n t , ¨ 1636627484.674000000 ] , s ¨ c o p e : ¨ [ j ¨ a v a . u t i l . C o l l e c t i o n s SingletonList\",[\"felord-client\"]],\"nbf\":[\"java.time.Instant\",1636627484.674000000],\"scope\":[\"java.util.Collections SingletonList,¨[f¨elord−client]¨],n¨bf:¨[j¨ava.time.Instant,¨1636627484.674000000],s¨cope:¨[j¨ava.util.CollectionsUnmodifiableSet”,[“message.read”,“message.write”]],“iss”:[“java.net.URL”,“http://localhost:9000”],“exp”:[“java.time.Instant”,1636627784.674000000],“iat”:[“java.time.Instant”,1636627484.674000000]},“metadata.token.invalidated”:false}",
“access_token_type”: “Bearer”,
“access_token_scopes”: “message.read,message.write”,
“oidc_id_token_value”: null,
“oidc_id_token_issued_at”: null,
“oidc_id_token_expires_at”: null,
“oidc_id_token_metadata”: null,
“refresh_token_value”: “hbD9dVMpu855FhDDOYapwsQSx8zO9iPX5LUZKeXWzUcbE2rgYRV-sgXl5vGwyByLNljcqVyK9Pgquzbcoe6dkt0_yPQPJfxLY8ezEQ-QREBjxNYqecd6OI9SHMQkBObG”,
“refresh_token_issued_at”: “2021-11-11 18:44:45”,
“refresh_token_expires_at”: “2021-11-11 19:44:45”,
“refresh_token_metadata”: “{”@class":“java.util.Collections$UnmodifiableMap”,“metadata.token.invalidated”:false}"
}
❝
存储的东西还是比较全的,甚至把Java类都序列化了。
确认授权持久化
资源拥有者(Resource Owner)对授权的确认信息OAuth2AuthorizationConsent的持久化,这个比较简单。下面是定义脚本:
CREATE TABLE oauth2_authorization_consent
(
registered_client_id varchar(100) NOT NULL,
principal_name varchar(200) NOT NULL,
authorities varchar(1000) NOT NULL,
PRIMARY KEY (registered_client_id, principal_name)
);
对应的持久化服务接口为OAuth2AuthorizationConsentService,也要注入Spring IoC:
@Bean
public OAuth2AuthorizationConsentService authorizationConsentService(JdbcTemplate jdbcTemplate,
RegisteredClientRepository registeredClientRepository) {
return new JdbcOAuth2AuthorizationConsentService(jdbcTemplate, registeredClientRepository);
}
持久化到数据库的OAuth2AuthorizationConsent用JSON表示为:
{
“registered_client_id”: “658cd010-4d8c-4824-a8c7-a86b642299af”,
“principal_name”: “felord”,
“authorities”: “SCOPE_message.read,SCOPE_message.write”
}
JWK
JWK全称JSON Web Key,是一个将加密的密钥用JSON对象描述的规范,和JWT一样是JOSE规范的重要组成部分。规范的详细定义可参考JWK文档。JWK参考示例:
{
“keys”: [
{
“kty”: “RSA”,
“x5t#S256”: “VFGQxCmgHIh_gaF-wPb1xC9oKA1w5la0EFmqqPMrqmw”,
“e”: “AQAB”,
“kid”: “felordcn”,
“x5c”: [
“MIIDczCCAlugAwIBAgIEURwmYzANBgkqhkiG9w0BAQsFADBqMQ0wCwYDVQQGEwQoY24pMQ0wCwYDVQQIEwQoaG4pMQ0wCwYDVQQHEwQoenopMRMwEQYDVQQKEwooZmVsb3JkY24pMRMwEQYDVQQLEwooZmVsb3JkY24pMREwDwYDVQQDEwgoRmVsb3JkKTAeFw0yMTEwMTgwNDUwMTRaFw0yMjEwMTgwNDUwMTRaMGoxDTALBgNVBAYTBChjbikxDTALBgNVBAgTBChobikxDTALBgNVBAcTBCh6eikxEzARBgNVBAoTCihmZWxvcmRjbikxEzARBgNVBAsTCihmZWxvcmRjbikxETAPBgNVBAMTCChGZWxvcmQpMIIBIjANBgkqhkiG9w0BAQEFAAOCAQ8AMIIBCgKCAQEAgo0TPk1td7iROmmLcGbOsZ2F68kTertDwRyk+leqBl+qyJAkjoVgVaCRRQHZmvu/YGp93vOaEd/zFdVj/rFvMXmwBxgYPOeSG0bHkYtFBaUiLf1vhW5lyiPHcGide3uw1p+il3JNiOpcnLCbAKZgzm4qaugeuOD02/M0YcMW2Jqg3SUWpC+9vu9yt5dVc1xpmpwEAamKzvynI3Zxl44ddlA8RRAS6kV0OUcKbEG63G3yZ4MHnhrFrZDuvlwfSSgn0wFOC/b6mJ+bUxByMAXKD0d4DS2B2mVl7RO5AzL4SFcqtZZE3Drtcli67bsENyOQeoTVaKO6gu5PEEFlQ7pHKwIDAQABoyEwHzAdBgNVHQ4EFgQUqbLZ76DtdEEpTZUcgP7LsdGk8/AwDQYJKoZIhvcNAQELBQADggEBAEzfhi6/B00NxSPKAYJea/0MIyHr4X8Ue6Du+xl2q0UFzSkyIiMcPNmOYW5L1PWGjxR5IIiUgxKI5bEvhLkHhkMV+GRQSPKJXeC3szHdoZ3fXDZnuC0I88a1YDsvzuVhyjLL/n5lETRT4QWo5LsAj5v7AX+p46HM0iqSyTptafm2wheEosFA3ro4+vEDRaMrKLY1KdJuvvrrQIRpplhB/JbncmjWrEEvICSLEXm+kdGFgWNXkNxF0PhTLyPu3tEb2xLmjFltALwi3KPUGv9zVjxb7KyYiMnVsOPnwpDLOyREM9j4RLDiwf0tsCqPqltVExvFZouoL26fhcozfcrqC70=”
],
“n”: “go0TPk1td7iROmmLcGbOsZ2F68kTertDwRyk-leqBl-qyJAkjoVgVaCRRQHZmvu_YGp93vOaEd_zFdVj_rFvMXmwBxgYPOeSG0bHkYtFBaUiLf1vhW5lyiPHcGide3uw1p-il3JNiOpcnLCbAKZgzm4qaugeuOD02_M0YcMW2Jqg3SUWpC-9vu9yt5dVc1xpmpwEAamKzvynI3Zxl44ddlA8RRAS6kV0OUcKbEG63G3yZ4MHnhrFrZDuvlwfSSgn0wFOC_b6mJ-bUxByMAXKD0d4DS2B2mVl7RO5AzL4SFcqtZZE3Drtcli67bsENyOQeoTVaKO6gu5PEEFlQ7pHKw”
}
]
}
❝
JWK的意义在于生成JWT和提供JWK端点给OAuth2.0资源服务器解码校验JWT。
公私钥
JWK会涉及到加密算法,这里使用RSASHA256算法来作为加密算法,并通过Keytool工具来生成.jks公私钥证书文件。当然你也可以通过openssl来生成pkcs12格式的证书。在Spring Security实战干货中已经对生成的方法进行了说明,这里不再赘述。
JWKSource
由于Spring Security的JOSE实现依赖的是nimbus-jose-jwt,所以这里只需要我们实现JWKSource <C extends SecurityContext>并注入Spring IoC即可。相关代码如下:
/**
* 加载JWK资源
* @return the jwk source
*/
@SneakyThrows
@Bean
public JWKSource jwkSource() {
//TODO 这里优化到配置
// 证书的路径
String path = “felordcn.jks”;
// 证书别名
String alias = “felordcn”;
自我介绍一下,小编13年上海交大毕业,曾经在小公司待过,也去过华为、OPPO等大厂,18年进入阿里一直到现在。
深知大多数Java工程师,想要提升技能,往往是自己摸索成长或者是报班学习,但对于培训机构动则几千的学费,着实压力不小。自己不成体系的自学效果低效又漫长,而且极易碰到天花板技术停滞不前!
因此收集整理了一份《2024年Java开发全套学习资料》,初衷也很简单,就是希望能够帮助到想自学提升又不知道该从何学起的朋友,同时减轻大家的负担。
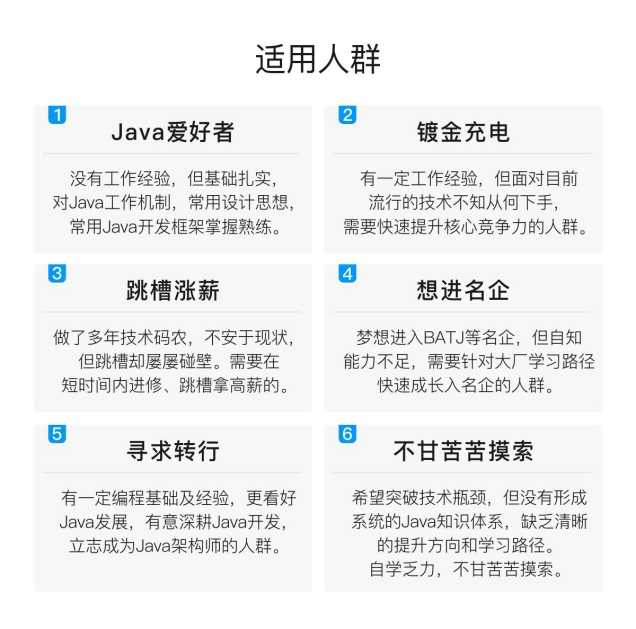


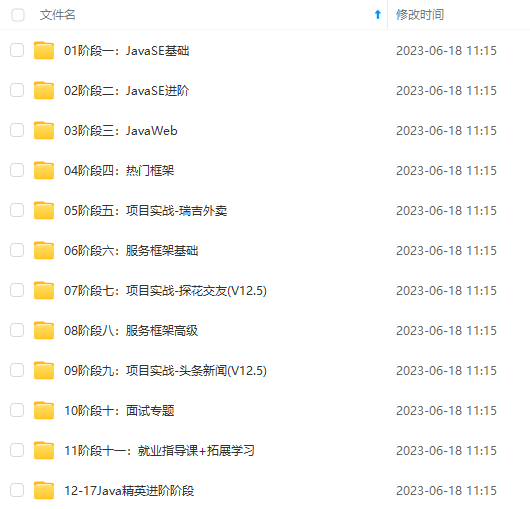
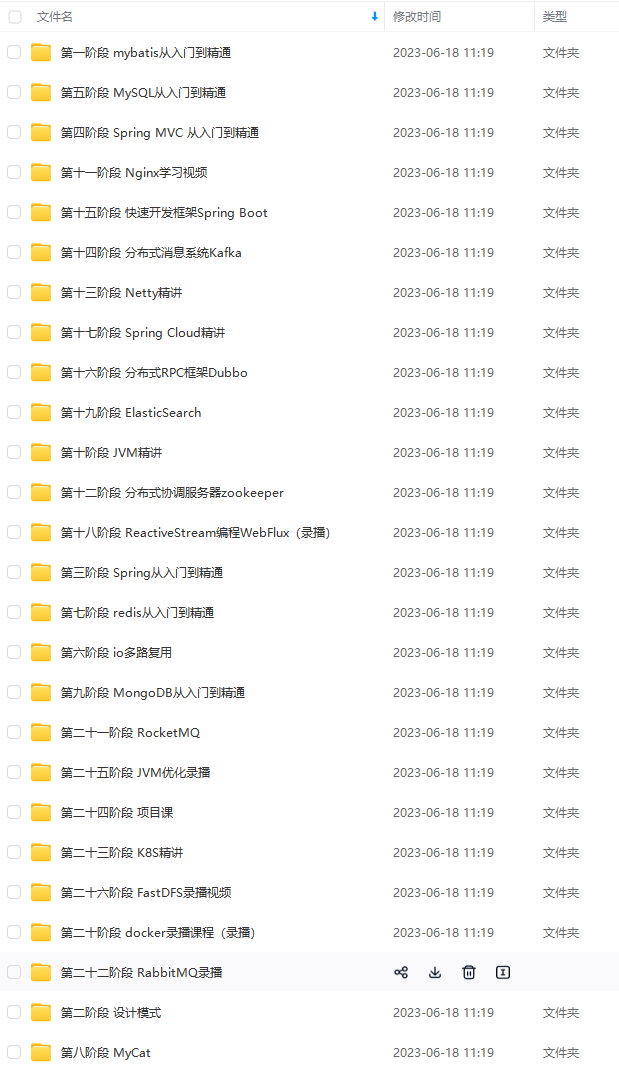
既有适合小白学习的零基础资料,也有适合3年以上经验的小伙伴深入学习提升的进阶课程,基本涵盖了95%以上Java开发知识点,真正体系化!
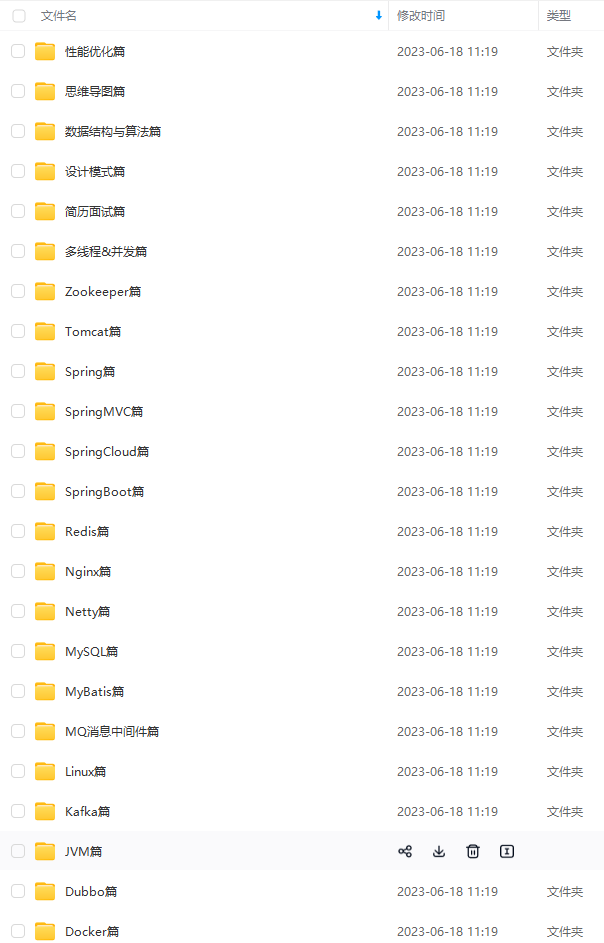
由于文件比较大,这里只是将部分目录大纲截图出来,每个节点里面都包含大厂面经、学习笔记、源码讲义、实战项目、讲解视频,并且后续会持续更新
如果你觉得这些内容对你有帮助,可以添加V获取:vip1024b (备注Java)

最后
光给面试题不给答案不是我的风格。这里面的面试题也只是凤毛麟角,还有答案的话会极大的增加文章的篇幅,减少文章的可读性
Java面试宝典2021版


最常见Java面试题解析(2021最新版)


2021企业Java面试题精选


一个人可以走的很快,但一群人才能走的更远。不论你是正从事IT行业的老鸟或是对IT行业感兴趣的新人,都欢迎扫码加入我们的的圈子(技术交流、学习资源、职场吐槽、大厂内推、面试辅导),让我们一起学习成长!

不是我的风格。这里面的面试题也只是凤毛麟角,还有答案的话会极大的增加文章的篇幅,减少文章的可读性
Java面试宝典2021版
[外链图片转存中…(img-opK8qkmy-1712763012400)]
[外链图片转存中…(img-QYJLhKWA-1712763012400)]
最常见Java面试题解析(2021最新版)
[外链图片转存中…(img-oCMIihOg-1712763012401)]
[外链图片转存中…(img-Fu6ntNyy-1712763012401)]
2021企业Java面试题精选
[外链图片转存中…(img-6TFOes21-1712763012401)]
[外链图片转存中…(img-9T0n4ilo-1712763012401)]
一个人可以走的很快,但一群人才能走的更远。不论你是正从事IT行业的老鸟或是对IT行业感兴趣的新人,都欢迎扫码加入我们的的圈子(技术交流、学习资源、职场吐槽、大厂内推、面试辅导),让我们一起学习成长!
[外链图片转存中…(img-S0W6bifh-1712763012402)]


